服务对外暴露
集群内部服务之间可以通过 ingress-traefik 实现域名调用。那外网用户(与集群不在同一网络环境下的用户D)该怎么访问集群服务呢?
用户使用服务一般都是点击按钮,触发相应的域名链接(假如是java.od.com)调用,而在互联网上公认的域名将是解析到公认的ip地址,此ip地址对应一台服务器E,服务器E一般有2个网卡,一个对外流量一个对内流量(假设公网地址是108.108.108.108,内网地址是10.10.10.10),则在服务器E上部署Nginx服务实现代理转发,将通过公网地址进来的所有流量通过Nginx转发走内网流量到服务器F的81端口,即转发到traefik容器内部的80端口(traefik服务部署在内部Kubernetes集群服务器F上,已通过hostPort将容器80端口映射到服务器F的81端口),再由ingress服务进行转发,直到正常访问资源。
访问流程: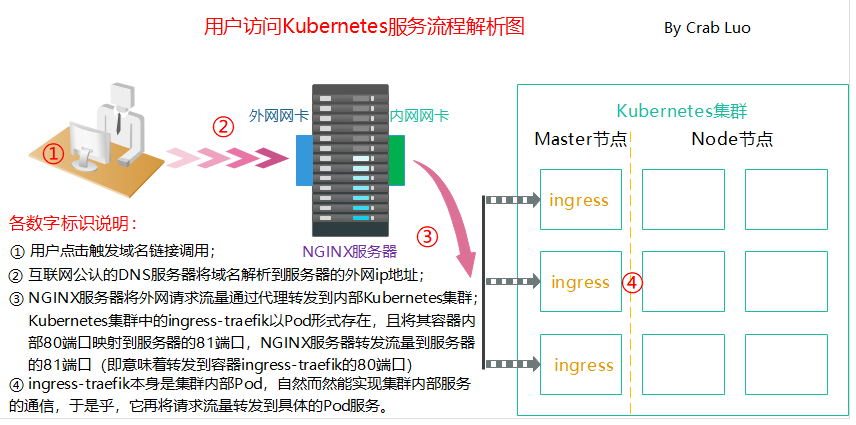
整体需求实现
环境说明
说明:
- 因资源有限,故将NG服务部署在master1,ingress-traefik以DaemonSet类型部署到3个master节点
- 给三台master打标签,以便能够运行ingress-traefik pod
标签:
kubectl label nodes master1 nickname=boss
kubectl label nodes master2 nickname=boss
kubectl label nodes master3 nickname=boss
nginx
yum -y install nginxsystemctl start nginxsystemctl enable nginx# cat /etc/nginx/nginx.conf |grep 'conf.d'include /etc/nginx/conf.d/*.conf;# 将所有*.od.com请求全部转发到default_backend_traefik# cat /etc/nginx/conf.d/od.com.confupstream default_backend_traefik {server 10.2.2.137:81 max_fails=3 fail_timeout=10s;server 10.2.2.166:81 max_fails=3 fail_timeout=10s;server 10.2.2.96:81 max_fails=3 fail_timeout=10s;}server {server_name *.od.com;location / {proxy_pass http://default_backend_traefik;proxy_set_header Host $http_host;proxy_set_header x-forwarded-for $proxy_add_x_forwarded_for;}}
开启ng文件服务
# cat /etc/nginx/conf.d/k8s-yaml.od.com.confserver {listen 80;server_name k8s-yaml.od.com;location / {autoindex on;default_type text/plain;root /data/k8s-yaml;}}# 服务重启systemclt restart nginx
ingress-traefik
ds.yaml
apiVersion: apps/v1#apiVersion: extensions/v1beta1kind: DaemonSetmetadata:name: traefik-ingressnamespace: kube-systemlabels:k8s-app: traefik-ingressspec:selector:matchLabels:k8s-app: traefik-ingresstemplate:metadata:labels:k8s-app: traefik-ingressname: traefik-ingressspec:serviceAccountName: traefik-ingress-controllerterminationGracePeriodSeconds: 60tolerations:- operator: "Exists"nodeSelector:#kubernetes.io/hostname: master1nickname: bosscontainers:- image: traefik:v1.7.2-alpinename: traefik-ingressports:- name: controllercontainerPort: 80hostPort: 81- name: admin-webcontainerPort: 8080securityContext:capabilities:drop:- ALLadd:- NET_BIND_SERVICEargs:- --api- --kubernetes- --logLevel=INFO- --insecureskipverify=true- --kubernetes.endpoint=https://10.2.2.6:6443 #集群vip地址- --accesslog- --accesslog.filepath=/var/log/traefik_access.log- --traefiklog- --traefiklog.filepath=/var/log/traefik.log- --metrics.prometheus
svc.yaml
kind: Service
apiVersion: v1
metadata:
name: traefik-ingress-service
namespace: kube-system
spec:
selector:
k8s-app: traefik-ingress
ports:
- protocol: TCP
port: 80
name: controller
- protocol: TCP
port: 8080
name: admin-web
ing.yaml
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: traefik-web-ui
namespace: kube-system
annotations:
kubernetes.io/ingress.class: traefik
spec:
rules:
- host: traefik.od.com
http:
paths:
- path: /
backend:
serviceName: traefik-ingress-service
servicePort: 8080
rbac.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: traefik-ingress-controller
namespace: kube-system
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRole
metadata:
name: traefik-ingress-controller
rules:
- apiGroups:
- ""
resources:
- services
- endpoints
- secrets
verbs:
- get
- list
- watch
- apiGroups:
- extensions
resources:
- ingresses
verbs:
- get
- list
- watch
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: traefik-ingress-controller
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: traefik-ingress-controller
subjects:
- kind: ServiceAccount
name: traefik-ingress-controller
namespace: kube-system
应用部署
kubectl apply -f .
整体效果展示
#地址解析
服务对应解析域名:traefik.od.com


