1.1 登陆位置注入测试
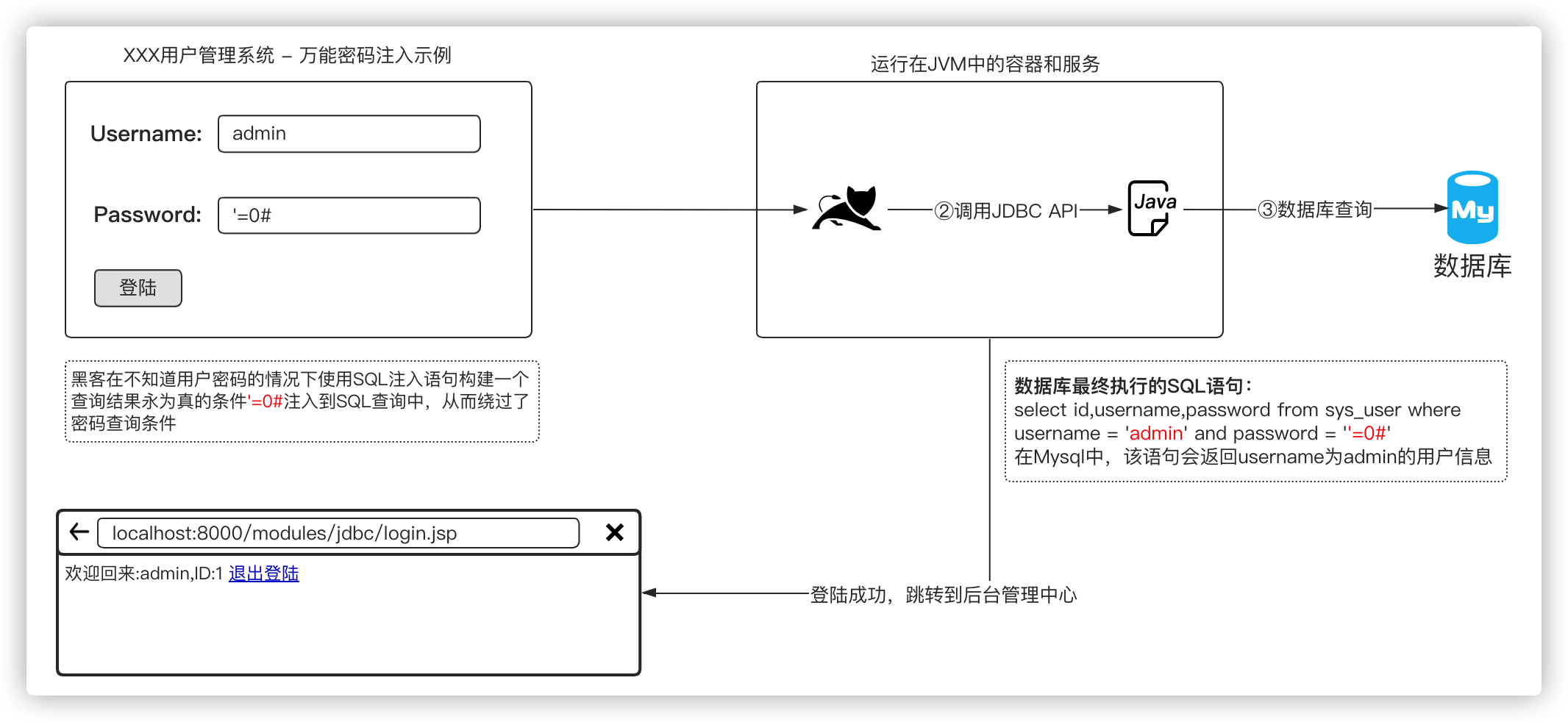
后台登陆系统注入在前些年是非常常见的,我们通常会使用' or '1'='1之类的注入语句来构建一个查询结果永为真的SQL,俗称:万能密码。
示例 - 用户登陆注入代码:
<%@ page contentType="text/html;charset=UTF-8" language="java" %><%@ page import="java.sql.Connection" %><%@ page import="java.sql.DriverManager" %><%@ page import="java.sql.ResultSet" %><%@ page import="java.util.HashMap" %><%@ page import="java.util.Map" %><%// MYSQL sys_user示例表,测试时请先创建对应的数据库和表//// CREATE TABLE `sys_user` (// `id` int(9) unsigned NOT NULL AUTO_INCREMENT COMMENT '用户ID',// `username` varchar(16) NOT NULL COMMENT '用户名',// `password` varchar(32) NOT NULL COMMENT '用户密码',// `user_avatar` varchar(255) DEFAULT NULL COMMENT '用户头像',// `register_time` datetime DEFAULT NULL COMMENT '注册时间',// PRIMARY KEY (`id`),// UNIQUE KEY `idx_sys_user_username` (`username`) USING BTREE// ) ENGINE=InnoDB AUTO_INCREMENT=6 DEFAULT CHARSET=utf8 COMMENT='系统用户表'//// INSERT INTO `sys_user` VALUES ('1', 'admin', '123456', '/res/images/avatar/default.png', '2020-05-05 17:21:27'), ('2', 'test', '123456', '/res/images/avatar/default.png', '2020-05-06 18:27:10'), ('3', 'root', '123456', '/res/images/avatar/default.png', '2020-05-06 18:28:27'), ('4', 'user', '123456', '/res/images/avatar/default.png', '2020-05-06 18:31:34'), ('5', 'rasp', '123456', '/res/images/avatar/default.png', '2020-05-06 18:32:08');%><%String sessionKey = "USER_INFO";Object sessionUser = session.getAttribute(sessionKey);// 退出登陆if (sessionUser != null && "exit".equals(request.getParameter("action"))) {session.removeAttribute(sessionKey);out.println("<script>alert('再见!');location.reload();</script>");return;}Map<String, String> userInfo = null;// 检查用户是否已经登陆成功if (sessionUser instanceof Map) {userInfo = (Map<String, String>) sessionUser;out.println("<p>欢迎回来:" + userInfo.get("username") + ",ID:" + userInfo.get("id") + " \r<a href='?action=exit'>退出登陆</a></p>");return;}String username = request.getParameter("username");String password = request.getParameter("password");// 处理用户登陆逻辑if (username != null && password != null) {userInfo = new HashMap<String, String>();ResultSet rs = null;Connection connection = null;try {Class.forName("com.mysql.jdbc.Driver");connection = DriverManager.getConnection("jdbc:mysql://localhost:3306/javaweb-bbs", "root", "root");String sql = "select id,username,password from sys_user where username = '" + username + "' and password = '" + password + "'";System.out.println(sql);rs = connection.prepareStatement(sql).executeQuery();while (rs.next()) {userInfo.put("id", rs.getString("id"));userInfo.put("username", rs.getString("username"));userInfo.put("password", rs.getString("password"));}// 检查是否登陆成功if (userInfo.size() > 0) {// 设置用户登陆信息session.setAttribute(sessionKey, userInfo);// 跳转到登陆成功页面response.sendRedirect(request.getServletPath());} else {out.println("<script>alert('登陆失败,账号或密码错误!');history.back(-1)</script>");}} catch (Exception e) {out.println("<script>alert('登陆失败,服务器异常!');history.back(-1)</script>");} finally {// 关闭数据库连接if (rs != null)rs.close();if (connection != null)connection.close();}return;}%><html><head><title>Login Test</title></head><body><div style="margin: 30px;"><form action="#" method="POST">Username:<input type="text" name="username" value="admin"/><br/>Password:<input type="text" name="password" value="'=0#"/><br/><input type="submit" value="登陆"/></form></div></body></html>
sys_user表结构如下:
| id | username | password | user_avatar | register_time |
|---|---|---|---|---|
| 1 | admin | 123456 | /res/images/avatar/default.png | 2020-05-05 17:21:27 |
| 2 | test | 123456 | /res/images/avatar/default.png | 2020-05-06 18:27:10 |
访问示例中的后台登陆地址:http://localhost:8000/modules/jdbc/login.jsp,如下图: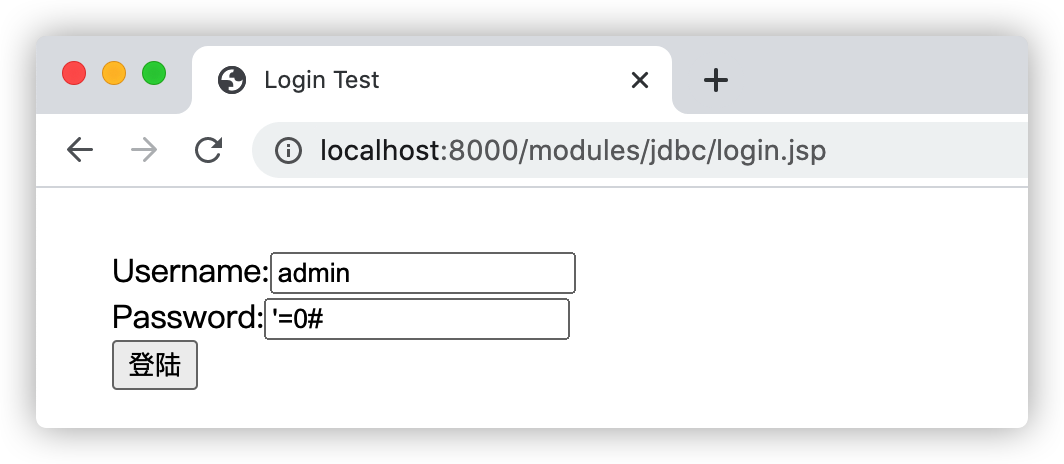
攻击者通过在密码参数处输入:'=0#即可使用SQL注入的方式改变查询逻辑,绕过密码认证并登陆系统,因此用于检测用户账号密码是否存在的SQL语句变成了:select id,username,password from sys_user where username = 'admin' and password = ''=0#'
其中的password的值预期是传入用户密码,但是实际上被攻击者传入了可改变查询逻辑的SQL语句,将运算结果改变为true,从而攻击者可以使用错误的用户及密码登陆系统,如下图: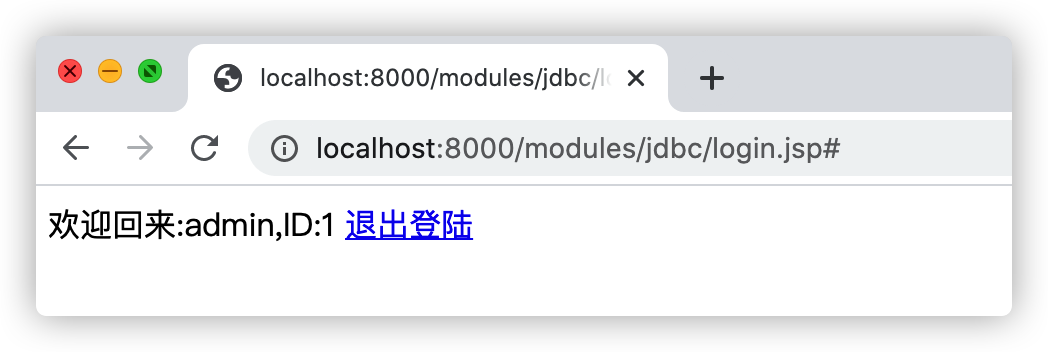
毫无疑问因为攻击者输入的信息足够的短小简洁,但是对于用户网站系统来说却有极强的杀伤性,绝大多数的WAF或者RASP产品都无法精准辨别'=0#的威胁性,无法正确做到精准防御。
万能密码登陆注入原理图解: