参考:https://blog.csdn.net/u014761412/article/details/85785650
1)搞出密钥,要记住密码
openssl genrsa -des3 -out xx.key 4096
2)搞出证书私钥
openssl rsa -in xx.key -out xx.pem
3)搞出证书请求:
openssl req -new -key xx.pem -out xx.csr
4)搞出最终证书: -trustout可以解决某些Expecting: TRUSTED CERTIFICATE问题
openssl x509 -req -days 3650 -in xx.csr -signkey xx.pem -out xx.crt
or
openssl x509 -trustout -req -days 3650 -in xx.csr -signkey xx.pem -out xx.crt
5)在nginx配置:
不需要反向代理的:
server {listen 443 ssl http2;listen [::]:443 ssl http2;server_name www.xxx.com;root /usr/share/nginx/html;ssl_certificate "/etc/nginx/ssl/www.xxx.com.crt";ssl_certificate_key "/etc/nginx/ssl/www.xxx.com.pem";ssl_session_cache shared:SSL:1m;ssl_session_timeout 10m;ssl_ciphers HIGH:!aNULL:!MD5;ssl_prefer_server_ciphers on;# Load configuration files for the default server block.include /etc/nginx/default.d/*.conf;error_page 404 /404.html;location = /40x.html {}error_page 500 502 503 504 /50x.html;location = /50x.html {}}
需要反向代理的:
upstream upsxxx {
server xxx.com;
}
server {
listen 443 ssl http2 default_server;
listen [::]:443 ssl http2 default_server;
charset utf-8;
server_name xxx;
ssl_certificate /etc/nginx/xx.crt;
ssl_certificate_key xx.pem;
ssl_session_timeout 5m;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:ECDHE:ECDH:AES:HIGH:!NULL:!aNULL:!MD5:!ADH:!RC4;
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
ssl_prefer_server_ciphers on;
location / {
proxy_pass https://upsxxx;
proxy_next_upstream error timeout invalid_header http_500 http_502 http_503 http_504;
proxy_redirect off;
proxy_buffering off;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
}
error_page 500 502 503 504 /50x.html;
location = /50x.html {
root /usr/share/nginx/html;
}
}
效果:
会提示不安全,继续访问后: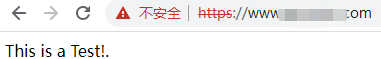
去掉提示,需要在浏览器设置信任或者花钱买证书。

