每一个技术出来都有它要解决的问题,VXLAN 也不例外。虚拟化(虚拟机和容器)的兴起使得一个数据中心会有成千上万的机器需要通信,而传统的 VLAN 技术只能支持 4096 个网络上限,已经满足不了不断扩展的数据中心规模越来越多的数据中心(尤其是公有云服务)需要提供多租户的功能,不同用户之间需要独立地分配 ip 和 MAC 地址,如何保证这个功能的扩展性和正确性也是一个待解决的问题云计算业务对业务灵活性要求很高,虚拟机可能会大规模迁移,并保证网络一直可用,也就是大二层的概念。解决这个问题同时保证二层的广播域不会过分扩大,也是云计算网络的要求传统二层+三层的网络在应对这些要求时变得力不从心,虽然很多改进型的技术比如堆叠、SVF、TRILL 等能够增加二层的范围,努力改进经典网络,但是要做到对网络改动小同时保证灵活性高却非常困难。为了解决这些问题,有很多方案被提出来,vxlan 就是其中之一。
1、DIY Flannel VxLAN Mode

# 1.环境配置VxLAN Tunnel:[root@k8s-1 ~]# yum -y install bridge-utils#1.k8s-1节点的配置:ip link add vxlan_docker type vxlan id 20 remote 172.12.1.12 dstport 4789 dev ens33ip link set vxlan_docker upbrctl addif docker0 vxlan_docker#2.k8s-2节点的配置:ip link add vxlan_docker type vxlan id 20 remote 172.12.1.11 dstport 4789 dev ens33ip link set vxlan_docker upbrctl addif docker0 vxlan_docker#配置说明第一步:创建接口vxlan0 type为vxlan,vni为20.第二部:创建的vxlan0 up起来.第三步:使用brctl 添加interface vxlan0 到bridge docker0上,连接docker0和vxlan的接口,这样数据包从docker0上来以后,就可以被vxlan封装了。# 2.启动相关容器:# 在k8s-1上创建容器:docker run --name vxlan-c01 -td burlyluo/nettoolbox //该容器的地址为:172.17.0.2。# 在k8s-2上创建容器:docker run --name vxlan-c01 -td burlyluo/nettoolbox //该容器的地址为:172.17.0.2。docker run --name vxlan-c02 -td burlyluo/nettoolbox //该容器的地址为:172.17.0.3。# 3.ping测:[root@k8s-1 ~]# docker exec -it vxlan-c01 bashbash-5.0# ping 172.17.0.3PING 172.17.0.3 (172.17.0.3): 56 data bytes64 bytes from 172.17.0.3: seq=0 ttl=64 time=1.446 ms64 bytes from 172.17.0.3: seq=1 ttl=64 time=0.643 ms^C--- 172.17.0.3 ping statistics ---2 packets transmitted, 2 packets received, 0% packet lossround-trip min/avg/max = 0.643/1.044/1.446 msbash-5.0######################地址信息:k8s-1节点:[root@k8s-1 ~]# ifconfig[root@k8s-1 ~]# docker exec -it vxlan-c01 ifconfigeth0 Link encap:Ethernet HWaddr 02:42:AC:11:00:02inet addr:172.17.0.2 Bcast:172.17.255.255 Mask:255.255.0.0UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1RX packets:19 errors:0 dropped:0 overruns:0 frame:0TX packets:3 errors:0 dropped:0 overruns:0 carrier:0collisions:0 txqueuelen:0RX bytes:1398 (1.3 KiB) TX bytes:182 (182.0 B)---#docker0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450inet 172.17.0.1 netmask 255.255.0.0 broadcast 172.17.255.255inet6 fe80::42:c9ff:feeb:2769 prefixlen 64 scopeid 0x20<link>ether 02:42:c9:eb:27:69 txqueuelen 0 (Ethernet)RX packets 18 bytes 1252 (1.2 KiB)RX errors 0 dropped 0 overruns 0 frame 0TX packets 5 bytes 526 (526.0 B)TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500inet 172.12.1.11 netmask 255.255.255.0 broadcast 172.12.1.255inet6 fe80::e222:32bb:f400:f0c3 prefixlen 64 scopeid 0x20<link>ether 00:0c:29:bd:fb:4a txqueuelen 1000 (Ethernet)RX packets 2833 bytes 356496 (348.1 KiB)RX errors 0 dropped 0 overruns 0 frame 0TX packets 3103 bytes 1317158 (1.2 MiB)TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0vxlan_docker: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450inet6 fe80::4431:deff:fe40:88d1 prefixlen 64 scopeid 0x20<link>ether 46:31:de:40:88:d1 txqueuelen 1000 (Ethernet)RX packets 20 bytes 1364 (1.3 KiB)RX errors 0 dropped 0 overruns 0 frame 0TX packets 20 bytes 1364 (1.3 KiB)TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0# k8s-2 节点:[root@k8s-2 ~]# docker exec -it vxlan-c02 ifconfigeth0 Link encap:Ethernet HWaddr 02:42:AC:11:00:03inet addr:172.17.0.3 Bcast:172.17.255.255 Mask:255.255.0.0UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1RX packets:18 errors:0 dropped:0 overruns:0 frame:0TX packets:3 errors:0 dropped:0 overruns:0 carrier:0collisions:0 txqueuelen:0RX bytes:1328 (1.2 KiB) TX bytes:182 (182.0 B)---#docker0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450inet 172.17.0.1 netmask 255.255.0.0 broadcast 172.17.255.255inet6 fe80::42:dcff:fea0:192e prefixlen 64 scopeid 0x20<link>ether 02:42:dc:a0:19:2e txqueuelen 0 (Ethernet)RX packets 6 bytes 308 (308.0 B)RX errors 0 dropped 0 overruns 0 frame 0TX packets 5 bytes 526 (526.0 B)TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500inet 172.12.1.12 netmask 255.255.255.0 broadcast 172.12.1.255inet6 fe80::a9cd:74a4:47fc:9fec prefixlen 64 scopeid 0x20<link>ether 00:0c:29:e2:bf:86 txqueuelen 1000 (Ethernet)RX packets 2620 bytes 1116242 (1.0 MiB)RX errors 0 dropped 0 overruns 0 frame 0TX packets 2065 bytes 282698 (276.0 KiB)TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0vxlan_docker: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450inet6 fe80::d463:d8ff:fee1:8b73 prefixlen 64 scopeid 0x20<link>ether d6:63:d8:e1:8b:73 txqueuelen 1000 (Ethernet)RX packets 8 bytes 420 (420.0 B)RX errors 0 dropped 0 overruns 0 frame 0TX packets 20 bytes 1364 (1.3 KiB)TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0######################4.抓包:#4.1:从容器到docker0网桥:eth0接口抓包No. Time Source Destination Protocol Length Info1 2021-07-26 20:54:03.857948 02:42:ac:11:00:02 Broadcast ARP 42 Who has 172.17.0.3? Tell 172.17.0.2Frame 1: 42 bytes on wire (336 bits), 42 bytes captured (336 bits)Ethernet II, Src: 02:42:ac:11:00:02 (02:42:ac:11:00:02), Dst: Broadcast (ff:ff:ff:ff:ff:ff)Address Resolution Protocol (request)No. Time Source Destination Protocol Length Info2 2021-07-26 20:54:03.858531 02:42:ac:11:00:03 02:42:ac:11:00:02 ARP 42 172.17.0.3 is at 02:42:ac:11:00:03Frame 2: 42 bytes on wire (336 bits), 42 bytes captured (336 bits)Ethernet II, Src: 02:42:ac:11:00:03 (02:42:ac:11:00:03), Dst: 02:42:ac:11:00:02 (02:42:ac:11:00:02)Address Resolution Protocol (reply)No. Time Source Destination Protocol Length Info3 2021-07-26 20:54:03.858537 172.17.0.2 172.17.0.3 ICMP 98 Echo (ping) request id=0x1d00, seq=0/0, ttl=64 (reply in 4)Frame 3: 98 bytes on wire (784 bits), 98 bytes captured (784 bits)Ethernet II, Src: 02:42:ac:11:00:02 (02:42:ac:11:00:02), Dst: 02:42:ac:11:00:03 (02:42:ac:11:00:03)Internet Protocol Version 4, Src: 172.17.0.2, Dst: 172.17.0.3Internet Control Message ProtocolNo. Time Source Destination Protocol Length Info4 2021-07-26 20:54:03.858948 172.17.0.3 172.17.0.2 ICMP 98 Echo (ping) reply id=0x1d00, seq=0/0, ttl=64 (request in 3)Frame 4: 98 bytes on wire (784 bits), 98 bytes captured (784 bits)Ethernet II, Src: 02:42:ac:11:00:03 (02:42:ac:11:00:03), Dst: 02:42:ac:11:00:02 (02:42:ac:11:00:02)Internet Protocol Version 4, Src: 172.17.0.3, Dst: 172.17.0.2Internet Control Message Protocol#4.2:学习对端VTEP的MAC地址:vxlan_docker上抓包No. Time Source Destination Protocol Length Info3 2021-07-26 20:54:03.857965 02:42:ac:11:00:02 Broadcast ARP 42 Who has 172.17.0.3? Tell 172.17.0.2Frame 3: 42 bytes on wire (336 bits), 42 bytes captured (336 bits)Ethernet II, Src: 02:42:ac:11:00:02 (02:42:ac:11:00:02), Dst: Broadcast (ff:ff:ff:ff:ff:ff)Address Resolution Protocol (request)No. Time Source Destination Protocol Length Info4 2021-07-26 20:54:03.858469 02:42:ac:11:00:03 02:42:ac:11:00:02 ARP 42 172.17.0.3 is at 02:42:ac:11:00:03Frame 4: 42 bytes on wire (336 bits), 42 bytes captured (336 bits)Ethernet II, Src: 02:42:ac:11:00:03 (02:42:ac:11:00:03), Dst: 02:42:ac:11:00:02 (02:42:ac:11:00:02)Address Resolution Protocol (reply)No. Time Source Destination Protocol Length Info5 2021-07-26 20:54:03.858549 172.17.0.2 172.17.0.3 ICMP 98 Echo (ping) request id=0x1d00, seq=0/0, ttl=64 (reply in 6)Frame 5: 98 bytes on wire (784 bits), 98 bytes captured (784 bits)Ethernet II, Src: 02:42:ac:11:00:02 (02:42:ac:11:00:02), Dst: 02:42:ac:11:00:03 (02:42:ac:11:00:03)Internet Protocol Version 4, Src: 172.17.0.2, Dst: 172.17.0.3Internet Control Message ProtocolNo. Time Source Destination Protocol Length Info6 2021-07-26 20:54:03.858915 172.17.0.3 172.17.0.2 ICMP 98 Echo (ping) reply id=0x1d00, seq=0/0, ttl=64 (request in 5)Frame 6: 98 bytes on wire (784 bits), 98 bytes captured (784 bits)Ethernet II, Src: 02:42:ac:11:00:03 (02:42:ac:11:00:03), Dst: 02:42:ac:11:00:02 (02:42:ac:11:00:02)Internet Protocol Version 4, Src: 172.17.0.3, Dst: 172.17.0.2Internet Control Message Protocol#4.3:构造VxLAN数据报文:No. Time Source Destination Protocol Length Info683 2021-07-26 20:54:03.857992 02:42:ac:11:00:02 Broadcast ARP 92 Who has 172.17.0.3? Tell 172.17.0.2Frame 683: 92 bytes on wire (736 bits), 92 bytes captured (736 bits)Ethernet II, Src: Vmware_bd:fb:4a (00:0c:29:bd:fb:4a), Dst: Vmware_e2:bf:86 (00:0c:29:e2:bf:86)Internet Protocol Version 4, Src: 172.12.1.11, Dst: 172.12.1.12User Datagram Protocol, Src Port: 51305, Dst Port: 4789Virtual eXtensible Local Area NetworkEthernet II, Src: 02:42:ac:11:00:02 (02:42:ac:11:00:02), Dst: Broadcast (ff:ff:ff:ff:ff:ff)Address Resolution Protocol (request)No. Time Source Destination Protocol Length Info684 2021-07-26 20:54:03.858469 02:42:ac:11:00:03 02:42:ac:11:00:02 ARP 92 172.17.0.3 is at 02:42:ac:11:00:03Frame 684: 92 bytes on wire (736 bits), 92 bytes captured (736 bits)Ethernet II, Src: Vmware_e2:bf:86 (00:0c:29:e2:bf:86), Dst: Vmware_bd:fb:4a (00:0c:29:bd:fb:4a)Internet Protocol Version 4, Src: 172.12.1.12, Dst: 172.12.1.11User Datagram Protocol, Src Port: 51881, Dst Port: 4789Virtual eXtensible Local Area NetworkEthernet II, Src: 02:42:ac:11:00:03 (02:42:ac:11:00:03), Dst: 02:42:ac:11:00:02 (02:42:ac:11:00:02)Address Resolution Protocol (reply)No. Time Source Destination Protocol Length Info685 2021-07-26 20:54:03.858562 172.17.0.2 172.17.0.3 ICMP 148 Echo (ping) request id=0x1d00, seq=0/0, ttl=64 (reply in 688)Frame 685: 148 bytes on wire (1184 bits), 148 bytes captured (1184 bits)Ethernet II, Src: Vmware_bd:fb:4a (00:0c:29:bd:fb:4a), Dst: Vmware_e2:bf:86 (00:0c:29:e2:bf:86)Internet Protocol Version 4, Src: 172.12.1.11, Dst: 172.12.1.12User Datagram Protocol, Src Port: 45497, Dst Port: 4789Virtual eXtensible Local Area NetworkEthernet II, Src: 02:42:ac:11:00:02 (02:42:ac:11:00:02), Dst: 02:42:ac:11:00:03 (02:42:ac:11:00:03)Internet Protocol Version 4, Src: 172.17.0.2, Dst: 172.17.0.3Internet Control Message ProtocolNo. Time Source Destination Protocol Length Info688 2021-07-26 20:54:03.858915 172.17.0.3 172.17.0.2 ICMP 148 Echo (ping) reply id=0x1d00, seq=0/0, ttl=64 (request in 685)Frame 688: 148 bytes on wire (1184 bits), 148 bytes captured (1184 bits)Ethernet II, Src: Vmware_e2:bf:86 (00:0c:29:e2:bf:86), Dst: Vmware_bd:fb:4a (00:0c:29:bd:fb:4a)Internet Protocol Version 4, Src: 172.12.1.12, Dst: 172.12.1.11User Datagram Protocol, Src Port: 59330, Dst Port: 4789Virtual eXtensible Local Area NetworkEthernet II, Src: 02:42:ac:11:00:03 (02:42:ac:11:00:03), Dst: 02:42:ac:11:00:02 (02:42:ac:11:00:02)Internet Protocol Version 4, Src: 172.17.0.3, Dst: 172.17.0.2Internet Control Message Protocol# 抓包可从这里获取:# https://github.com/BurlyLuo/cni/tree/master/weiluo/diy-vxlan
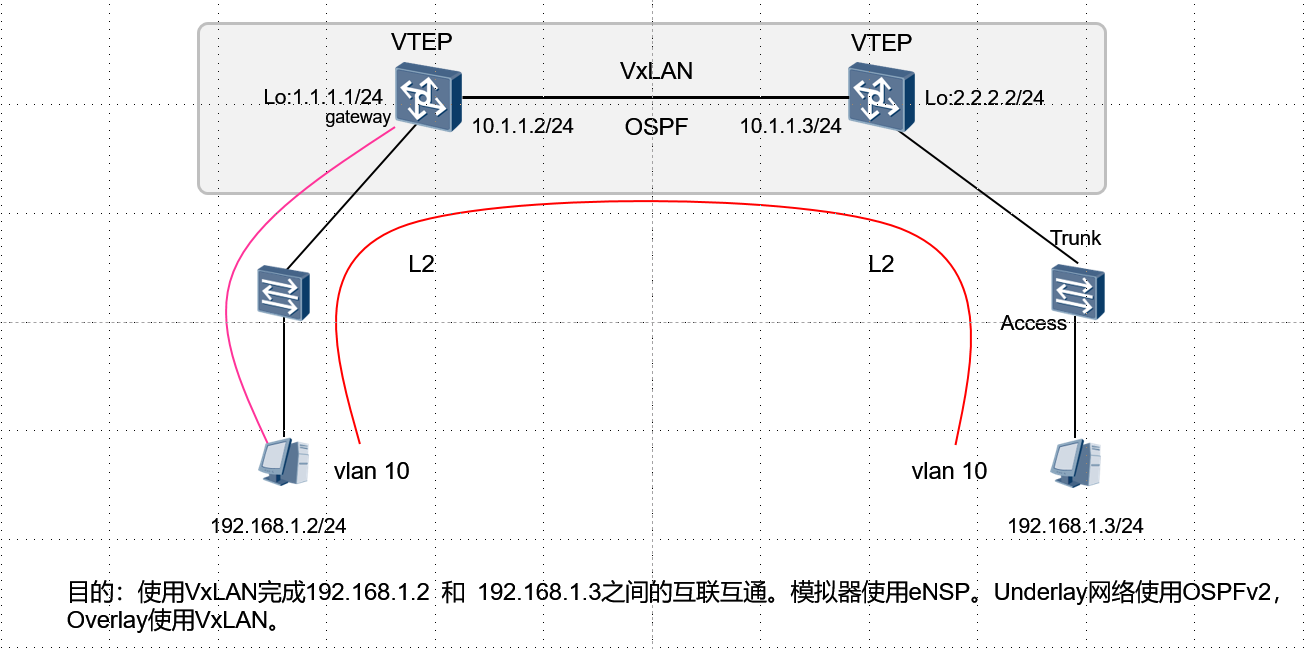
2、eNSP 实现VxLAN
环境:
# ENV 说明:
eNSP:1.3.00.100 V100R003C00 SPC100
CE: CE12800
VirtualBox: VirtualBox Graphical User Interface
Version 5.2.44 r139111 (Qt5.6.2)
Wireshark: Version 2.6.0 (v2.6.0-0-gc7239f02)
topo:
# 地址信息
10.1.1.1/24 10.1.1.2/24
G1/0/0 G1/0/0
1.1.1.1/32 CE1------------------------CE2 2.2.2.2/32
G1/0/1 | OSPF |G1/0/1
| |
| G0/0/1 G0/0/1 |
LSW1 LSW2
G0/0/2 | | G0/0/2
| |
| |
PC1 PC2
192.168.1.1 192.168.1.2
vlan 10 vlan 10
# 配置思路介绍:
# 统一原则:由于该类型设备为超核心设备,所以每一个步骤都需要commit。包括修改名字。
1.PC1和LSW1之间为普通二层接入,并被划分到相应的VLAN中。配置为Access接口类型。
2.LSW1和CE1之间靠近LSW1侧配置为普通Trunk类型。为了接入更多的VLAN,这里只有VLAN10,但可以配置多VLAN。
3.LSW1和CE1之间靠近CE1侧配置为使用dot1q 来封装VxLAN的数据报文。由于涉及到子接口配置,所以这里需要父接口和子接口都需要undo shutdown.
4.underlay网络使用OSPF网络。
配置说明:
##############################################################
# 左边Leg配置
##############################################################
#1. PC1配置:
PC>ipconfig
Link local IPv6 address...........: fe80::5689:98ff:fe1f:7471
IPv6 address......................: :: / 128
IPv6 gateway......................: ::
IPv4 address......................: 192.168.1.1 # 地址
Subnet mask.......................: 255.255.255.0 # 掩码
Gateway...........................: 0.0.0.0
Physical address..................: 54-89-98-1F-74-71 # MAC
DNS server........................:
#2. LSW1配置:
<LSW1>dis current-configuration
#
sysname LSW1 # 修改交换机名字为:LSW1
#
vlan batch 10 # 创建VLAN 10
#
cluster enable
ntdp enable
ndp enable
#
drop illegal-mac alarm
#
diffserv domain default
#
drop-profile default
#
aaa
authentication-scheme default
authorization-scheme default
accounting-scheme default
domain default
domain default_admin
local-user admin password simple admin
local-user admin service-type http
#
interface Vlanif1
#
interface MEth0/0/1
#
interface GigabitEthernet0/0/1
port link-type trunk # 配置LSW1和CE1之间靠近LSW1之间的接口为Trunk
port trunk allow-pass vlan 2 to 4094 # 配置该Trunk允许相应的VLAN通过。这里是全放通
#
interface GigabitEthernet0/0/2
port link-type access
port default vlan 10
#
interface GigabitEthernet0/0/3
#
interface GigabitEthernet0/0/4
#
interface GigabitEthernet0/0/5
#
interface GigabitEthernet0/0/6
#
interface GigabitEthernet0/0/7
#
interface GigabitEthernet0/0/8
#
interface GigabitEthernet0/0/9
#
interface GigabitEthernet0/0/10
#
interface GigabitEthernet0/0/11
#
interface GigabitEthernet0/0/12
#
interface GigabitEthernet0/0/13
#
interface GigabitEthernet0/0/14
#
interface GigabitEthernet0/0/15
#
interface GigabitEthernet0/0/16
#
interface GigabitEthernet0/0/17
#
interface GigabitEthernet0/0/18
#
interface GigabitEthernet0/0/19
#
interface GigabitEthernet0/0/20
#
interface GigabitEthernet0/0/21
#
interface GigabitEthernet0/0/22
#
interface GigabitEthernet0/0/23
#
interface GigabitEthernet0/0/24
#
interface NULL0
#
user-interface con 0
user-interface vty 0 4
#
return
<LSW1>
#3.CE1配置:
[~CE1]dis cu
[~CE1]dis current-configuration
!Software Version V200R005C10SPC607B607
!Last configuration was updated at 2021-07-26 21:16:32+00:00 by SYSTEM automatic
ally
!Last configuration was saved at 2020-11-08 14:25:28+00:00
#
sysname CE1
#
device board 17 board-type CE-MPUB
device board 1 board-type CE-LPUE
#
bridge-domain 10 # 配置BD域,由于这里BD域中实际上为了配置VNI,所以如果哪里需要该VNI的VxLAN封装的话,就引用即可
vxlan vni 10 # 配置VxLAN的VNI ID
#
aaa
#
authentication-scheme default
#
authorization-scheme default
#
accounting-scheme default
#
domain default
#
domain default_admin
#
interface MEth0/0/0
undo shutdown
#
interface GE1/0/0 # 配置接口
undo portswitch # 关闭portswitch,打开三层功能
undo shutdown # 开启该接口
ip address 10.1.1.1 255.255.255.0 # 配置underlay接口地址
#
interface GE1/0/1 # 配置父接口开启
undo shutdown
#
interface GE1/0/1.10 mode l2 # 配置子接口,并设置为L2模式
encapsulation dot1q vid 10 # 配置封装类型为dot1q,且VLAN ID为10
bridge-domain 10 # 引用BD域,来打对应的VxLAN的VNI
#
interface GE1/0/2
shutdown
#
interface GE1/0/3
shutdown
#
interface GE1/0/4
shutdown
#
interface GE1/0/5
shutdown
#
interface GE1/0/6
shutdown
#
interface GE1/0/7
shutdown
#
interface GE1/0/8
shutdown
#
interface GE1/0/9
shutdown
#
interface LoopBack0
ip address 1.1.1.1 255.255.255.255 # 配置VTEP的地址
#
interface Nve1 # 配置VTEP
source 1.1.1.1 # 配置VTEP使用的源接口地址
vni 10 head-end peer-list 2.2.2.2 # 配置VTEP 针对于VNI 10 的使用头端复制来转发,且peer为另一个VTEP地址为:2.2.2.2
#
interface NULL0
#
ospf 1 router-id 1.1.1.1 # 配置OSPF underlay网络互联互通
area 0.0.0.0
network 0.0.0.0 255.255.255.255 # 这里配置全放通,生产中切记需要精确放通
#
ssh authorization-type default aaa
#
ssh server cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_
cbc aes128_cbc 3des_cbc
#
ssh server dh-exchange min-len 1024
#
ssh client cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_
cbc aes128_cbc 3des_cbc
#
user-interface con 0
#
vm-manager
#
return
[~CE1]
##############################################################
# 右边边Leg配置
##############################################################
# PC2配置:
PC>ipconfig
Link local IPv6 address...........: fe80::5689:98ff:fe46:4117
IPv6 address......................: :: / 128
IPv6 gateway......................: ::
IPv4 address......................: 192.168.1.2
Subnet mask.......................: 255.255.255.0
Gateway...........................: 0.0.0.0
Physical address..................: 54-89-98-46-41-17
DNS server........................:
# LSW2配置:
<LSW2>dis current-configuration
#
sysname LSW2
#
vlan batch 10
#
stp disable
#
cluster enable
ntdp enable
ndp enable
#
drop illegal-mac alarm
#
diffserv domain default
#
drop-profile default
#
aaa
authentication-scheme default
authorization-scheme default
accounting-scheme default
domain default
domain default_admin
local-user admin password simple admin
local-user admin service-type http
#
interface Vlanif1
#
interface MEth0/0/1
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 2 to 4094
#
interface GigabitEthernet0/0/2
port link-type access
port default vlan 10
#
interface GigabitEthernet0/0/3
#
interface GigabitEthernet0/0/4
#
interface GigabitEthernet0/0/5
#
interface GigabitEthernet0/0/6
#
interface GigabitEthernet0/0/7
#
interface GigabitEthernet0/0/8
#
interface GigabitEthernet0/0/9
#
interface GigabitEthernet0/0/10
#
interface GigabitEthernet0/0/11
#
interface GigabitEthernet0/0/12
#
interface GigabitEthernet0/0/13
#
interface GigabitEthernet0/0/14
#
interface GigabitEthernet0/0/15
#
interface GigabitEthernet0/0/16
#
interface GigabitEthernet0/0/17
#
interface GigabitEthernet0/0/18
#
interface GigabitEthernet0/0/19
#
interface GigabitEthernet0/0/20
#
interface GigabitEthernet0/0/21
#
interface GigabitEthernet0/0/22
#
interface GigabitEthernet0/0/23
#
interface GigabitEthernet0/0/24
#
interface NULL0
#
user-interface con 0
user-interface vty 0 4
#
return
<LSW2>
# CE2配置:
<CE2>dis current-configuration
!Software Version V200R005C10SPC607B607
!Last configuration was updated at 2021-07-26 21:16:32+00:00 by SYSTEM automatic
ally
!Last configuration was saved at 2020-11-08 14:25:33+00:00
#
sysname CE2
#
device board 17 board-type CE-MPUB
device board 1 board-type CE-LPUE
#
bridge-domain 10
vxlan vni 10
#
aaa
#
authentication-scheme default
#
authorization-scheme default
#
accounting-scheme default
#
domain default
#
domain default_admin
#
interface MEth0/0/0
undo shutdown
#
interface GE1/0/0
undo portswitch
undo shutdown
ip address 10.1.1.2 255.255.255.0
#
interface GE1/0/1
undo shutdown
#
interface GE1/0/1.10 mode l2
encapsulation dot1q vid 10
bridge-domain 10
#
interface GE1/0/2
shutdown
#
interface GE1/0/3
shutdown
#
interface GE1/0/4
shutdown
#
interface GE1/0/5
shutdown
#
interface GE1/0/6
shutdown
#
interface GE1/0/7
shutdown
#
interface GE1/0/8
shutdown
#
interface GE1/0/9
shutdown
#
interface LoopBack0
ip address 2.2.2.2 255.255.255.255
#
interface Nve1
source 2.2.2.2
vni 10 head-end peer-list 1.1.1.1
#
interface NULL0
#
ospf 1 router-id 2.2.2.2
area 0.0.0.0
network 0.0.0.0 255.255.255.255
#
ssh authorization-type default aaa
#
ssh server cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_
cbc aes128_cbc 3des_cbc
#
ssh server dh-exchange min-len 1024
#
ssh client cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_
cbc aes128_cbc 3des_cbc
#
user-interface con 0
#
vm-manager
#
return
RFC定义了VLAN扩展方案VXLAN(Virtual eXtensible Local Area Network,虚拟扩展局域网)。VXLAN采用MAC in UDP(User Datagram Protocol)封装方式,是NVO3(Network Virtualization over Layer 3)中的一种网络虚拟化技术。
服务器虚拟化技术的广泛部署,极大地增加了数据中心的计算密度;同时,为了实现业务的灵活变更,虚拟机VM需要能够在网络中不受限迁移,这给传统的“二层+三层”数据中心网络带来了新的挑战。
虚拟机规模受网络设备表项规格的限制
在传统二层网络环境下,数据报文是通过查询MAC地址表进行二层转发。服务器虚拟化后,VM的数量比原有的物理机发生了数量级的增长,伴随而来的便是VM网卡MAC地址数量的空前增加。而接入侧二层设备的MAC地址表规格较小,无法满足快速增长的VM数量。
网络隔离能力有限
VLAN作为当前主流的网络隔离技术,在标准定义中只有12比特,因此可用的VLAN数量仅4096个。对于公有云或其它大型虚拟化云计算服务这种动辄上万甚至更多租户的场景而言,VLAN的隔离能力无法满足。
虚拟机迁移范围受限
由于服务器资源等问题(如CPU过高,内存不够等),虚拟机迁移已经成为了一个常态性业务。 虚拟机迁移是指将虚拟机从一个物理机迁移到另一个物理机。为了保证虚拟机迁移过程中业务不中断,则需要保证虚拟机的IP地址、MAC地址等参数保持不变,这就要求虚拟机迁移必须发生在一个二层网络中。而传统的二层网络,将虚拟机迁移限制在了一个较小的局部范围内。
为了应对传统数据中心网络对服务器虚拟化技术的限制,VXLAN技术应运而生,其能够很好的解决上述问题。
针对虚拟机规模受设备表项规格限制
VXLAN将管理员规划的同一区域内的VM发出的原始报文封装成新的UDP报文,并使用物理网络的IP和MAC地址作为外层头,这样报文对网络中的其他设备只表现为封装后的参数。因此,极大降低了大二层网络对MAC地址规格的需求。
针对网络隔离能力限制
VXLAN引入了类似VLAN ID的用户标识,称为VXLAN网络标识VNI(VXLAN Network Identifier),由24比特组成,支持多达16M的VXLAN段,有效得解决了云计算中海量租户隔离的问题。
针对虚拟机迁移范围受限
VXLAN将VM发出的原始报文进行封装后通过VXLAN隧道进行传输,隧道两端的VM不需感知传输网络的物理架构。这样,对于具有同一网段IP地址的VM而言,即使其物理位置不在同一个二层网络中,但从逻辑上看,相当于处于同一个二层域。即VXLAN技术在三层网络之上,构建出了一个虚拟的大二层网络,只要虚拟机路由可达,就可以将其规划到同一个大二层网络中。这就解决了虚拟机迁移范围受限问题。
为了解决数据中心网络服务器虚拟化以及虚拟机不受限迁移问题,VXLAN特性应运而生。由于VXLAN特性在本质上属于一种VPN技术,因此,其同样能够应用在园区网络中,以实现分散物理站点之间的二层互联以及站点间的三层互联。
在当前的园区网中,租户站点与站点之间为了实现二、三层互联,需要部署相关设备以及多种二、三层网络技术。而基于Overlay的VXLAN技术,不感知当前的物理网络,能够在任意路由可达的网络上叠加二层虚拟网络,实现站点与站点之间的二层互联。同时,基于VXLAN三层网关,也能够实现站点与站点之间的三层互联。因此,通过VXLAN技术实现租户不同站点之间的互联更加快速、灵活。

