首先,说明一下我们要做的是,serverA 服务器的 usera 用户免密码登录 serverB 服务器的 userb用户。
我们先使用usera 登录 serverA 服务器
[root@serverA ~]# su - usera[usera@serverA ~]$ pwd/home/usera
然后在serverA上生成密钥对
1. [usera@serverA ~]$ ssh-keygen -t rsa2. Generating public/private rsa key pair.3. Enter file in which to save the key (/home/usera/.ssh/id_rsa):4. Created directory '/home/usera/.ssh'.5. Enter passphrase (empty for no passphrase):6. Enter same passphrase again:7. Your identification has been saved in /home/usera/.ssh/id_rsa.8. Your public key has been saved in /home/usera/.ssh/id_rsa.pub.9. The key fingerprint is:10. 39:f2:fc:70:ef:e9:bd:05:40:6e:64:b0:99:56:6e:01 usera@serverA11. The key's randomart image is:12. +--[ RSA 2048]----+13. | Eo* |14. | @ . |15. | = * |16. | o o . |17. | . S . |18. | + . . |19. | + . .|20. | + . o . |21. | .o= o. |22. +-----------------+
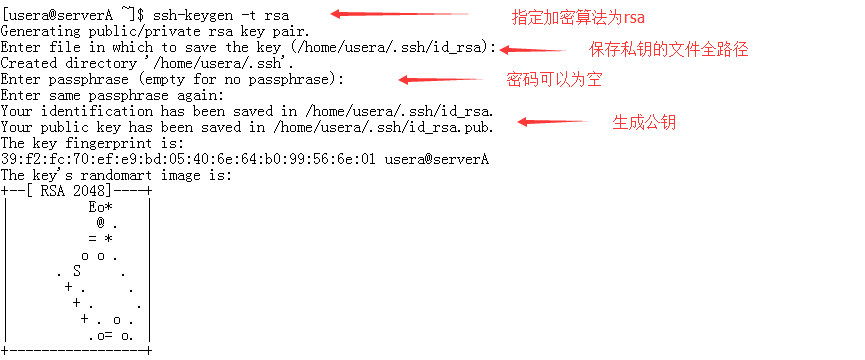
此时会在/home/usera/.ssh目录下生成密钥对
1. [usera@serverA ~]$ ls -la .ssh2. 总用量 163. drwx------ 2 usera usera 4096 8月 24 09:22 .4. drwxrwx--- 12 usera usera 4096 8月 24 09:22 ..5. -rw------- 1 usera usera 1675 8月 24 09:22 id_rsa6. -rw-r--r-- 1 usera usera 399 8月 24 09:22 id_rsa.pub
然后将公钥上传到serverB 服务器的,并以userb用户登录
1. [usera@portalweb1 ~]$ ssh-copy-id userb@10.124.84.202. The authenticity of host '10.124.84.20 (10.124.84.20)' can't be established.3. RSA key fingerprint is f0:1c:05:40:d3:71:31:61:b6:ad:7c:c2:f0:85:3c:cf.4. Are you sure you want to continue connecting (yes/no)? yes5. Warning: Permanently added '10.124.84.20' (RSA) to the list of known hosts.6. userb@10.124.84.29's password:7. Now try logging into the machine, with "ssh 'userb@10.124.84.20'", and check in:8.9. .ssh/authorized_keys10.11. to make sure we haven't added extra keys that you weren't expecting.

这个时候usera的公钥文件内容会追加写入到userb的 .ssh/authorized_keys 文件中
1. [usera@serverA ~]$ cat .ssh/id_rsa.pub2. ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEA2dpxfvifkpswsbusPCUWReD/mfTWpDEErHLWAxnixGiXLvHuS9QNavepZoCvpbZWHade88KLPkr5XEv6M5RscHXxmxJ1IE5vBLrrS0NDJf8AjCLQpTDguyerpLybONRFFTqGXAc/ximMbyHeCtI0vnuJlvET0pprj7bqmMXr/2lNlhIfxkZCxgZZQHgqyBQqk/RQweuYAiuMvuiM8Ssk/rdG8hL/n0eXjh9JV8H17od4htNfKv5+zRfbKi5vfsetfFN49Q4xa7SB9o7z6sCvrHjCMW3gbzZGYUPsj0WKQDTW2uN0nH4UgQo7JfyILRVZtwIm7P6YgsI7vma/vRP0aw== usera@serverA
查看serverB服务器userb用户下的 ~/.ssh/authorized_keys文件,内容是一样的,此处我就不粘贴图片了。
1. [userb@serverB ~]$ cat .ssh/authorized_keys2. ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEA2dpxfvifkpswsbusPCUWReD/mfTWpDEErHLWAxnixGiXLvHuS9QNavepZoCvpbZWHade88KLPkr5XEv6M5RscHXxmxJ1IE5vBLrrS0NDJf8AjCLQpTDguyerpLybONRFFTqGXAc/ximMbyHeCtI0vnuJlvET0pprj7bqmMXr/2lNlhIfxkZCxgZZQHgqyBQqk/RQweuYAiuMvuiM8Ssk/rdG8hL/n0eXjh9JV8H17od4htNfKv5+zRfbKi5vfsetfFN49Q4xa7SB9o7z6sCvrHjCMW3gbzZGYUPsj0WKQDTW2uN0nH4UgQo7JfyILRVZtwIm7P6YgsI7vma/vRP0aw== usera@serverA
另外我们要注意,.ssh目录的权限为700,其下文件authorized_keys和私钥的权限为600。否则会因为权限问题导致无法免密码登录。我们可以看到登陆后会有known_hosts文件生成。
1. [useb@serverB ~]$ ls -la .ssh2. total 243. drwx------. 2 useb useb 4096 Jul 27 16:13 .4. drwx------. 35 useb useb 4096 Aug 24 09:18 ..5. -rw------- 1 useb useb 796 Aug 24 09:24 authorized_keys6. -rw------- 1 useb useb 1675 Jul 27 16:09 id_rsa7. -rw-r--r-- 1 useb useb 397 Jul 27 16:09 id_rsa.pub8. -rw-r--r-- 1 useb useb 1183 Aug 11 13:57 known_hosts
这样做完之后我们就可以免密码登录了
[usera@serverA ~]$ ssh userb@10.124.84.20
另外,将公钥拷贝到服务器的~/.ssh/authorized_keys文件中方法有如下几种:
1、将公钥通过scp拷贝到服务器上,然后追加到~/.ssh/authorized_keys文件中,这种方式比较麻烦。scp -P 22 ~/.ssh/id_rsa.pub user@host:~/。
2、通过ssh-copy-id程序,就是我演示的方法,ssh-copyid user@host即可
3、可以通过cat ~/.ssh/id_rsa.pub | ssh -p 22 user@host ‘cat >> ~/.ssh/authorized_keys’,这个也是比较常用的方法,因为可以更改端口号。

