- 1#消息摘要算法
- 以输入流的方式去获取摘要DigestInputStream
- 以输出流的方式更改要加密的源数据DigestOnputStream
- 2#算法参数
- 3#KeyPair,非堆称加密的密钥对,java7提供了DH,ECDH,RSA,ECDSA,DSA等多种非对称加密和签名算法的实现,如构建DH密钥对时,密钥的长度要求为64位的倍数,范围为512-1024,默认长度为1024.生成一个DSA密钥对:
- 构建密钥对与还原密钥
- 结合随机数对象构建对称密钥,Java 7 支持AES密钥长度128,192,256位
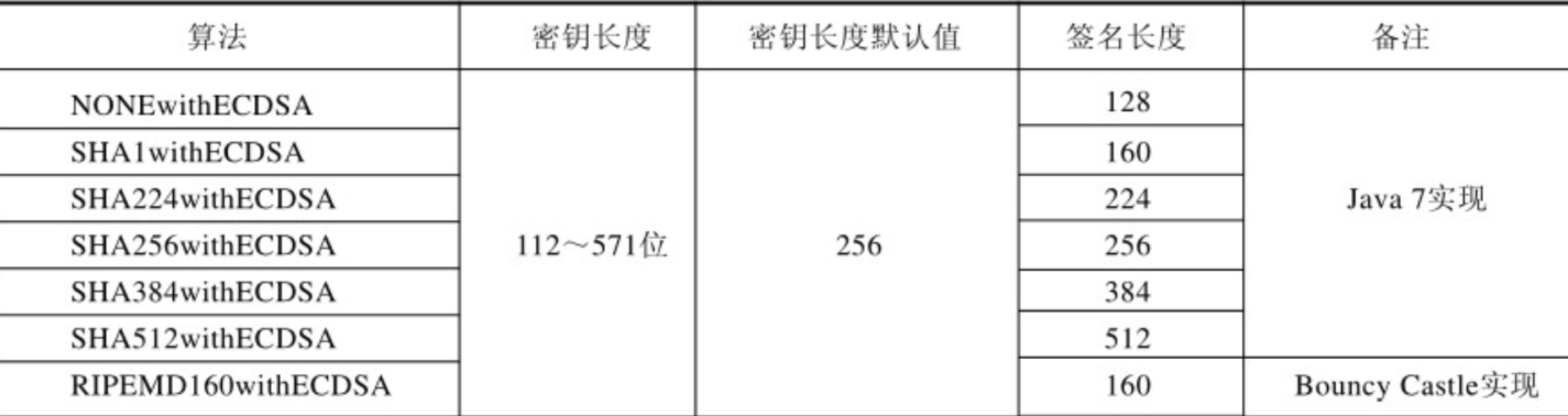
- 4#Signature签名,数字签名算法主要包括RSA,DSA,ECDSA三种,生成签名与验证
- 利用SignedObject生成签名与验证
- 数字时间戳Timestamp
- 5#KeyStore用于存储密钥和证书,从keyStore里根据别名获取私钥
- 6#Mac,安全消息摘要算法,区别与MessageDigest,需要有一个共享的密钥来生成,支持HmacMD5,
- HmacSHA1,HmacSHA256,HmacSHA384,HmacSHA512 5种消息摘要算法
- 7#SecretKeyFactory,密钥工厂,用于生产密钥,用于byte数组还原成密钥对象
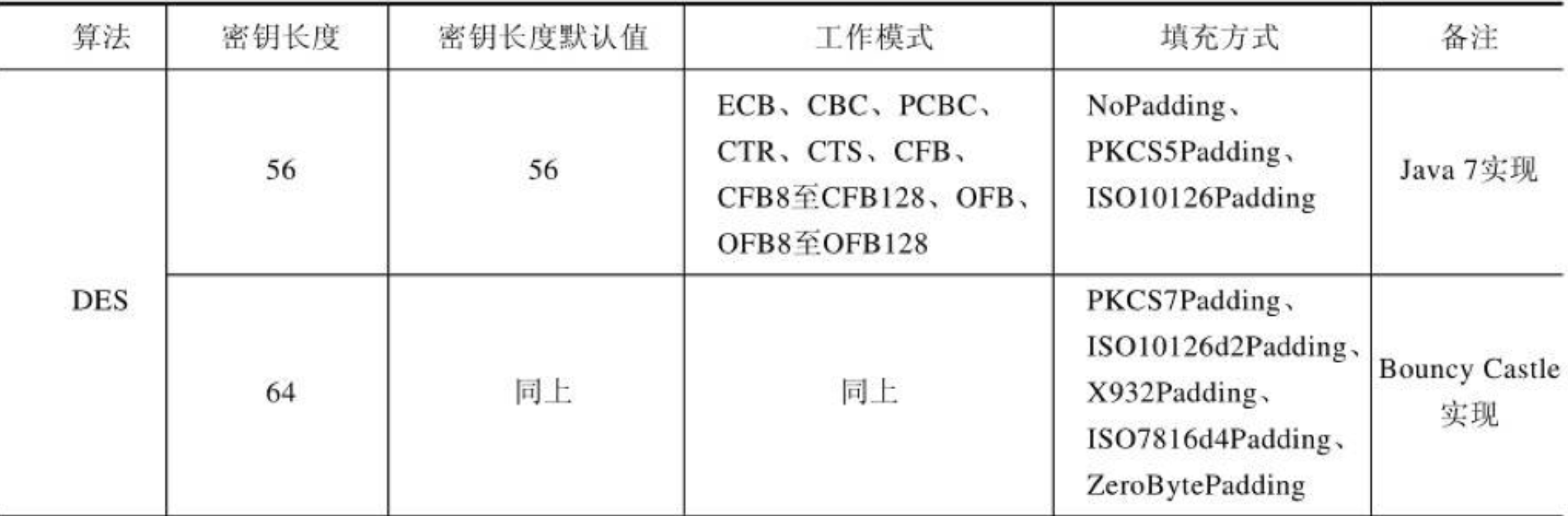
- 8#加解密的核心Cipher,参数transformation的格式“算法/工作模式/填充模式”,不同的算法支持不同的工作模式和填充模式
- 9#KeySpec,密钥规范,用于还原公私钥和对称密钥,X509EncodedKeySpec用于非对称的公钥构建,PKCS8EncodedKeySpec用于非对称的私钥构建,SecretKeySpec用于对称密钥构建,DESKeySpec指定DES算法,DESedeKeySpec指定三重DES加密算法,PBEKeySpec指定PBE算法
- 10#证书Certificate,关于数字证书,其实就是机构给网站的一张可用凭证,用来表明发送者是否为真正的发送者,里面有传输时用到的公钥,如下
- 加载证书
- 构建证书签名
- 证书撤销列表CRL,用与验证证书是否被撤销或者无效
- 11#SSL,构建KeyManagerFactory
- 构建信任工厂
- 构建SSLSocketFactory
- 与服务端建立SSLSocket连接并且获取证书链
- 12#Base64算法,约为原文的4/3倍,字符数以4为单位的整数倍,java.util的基本实现
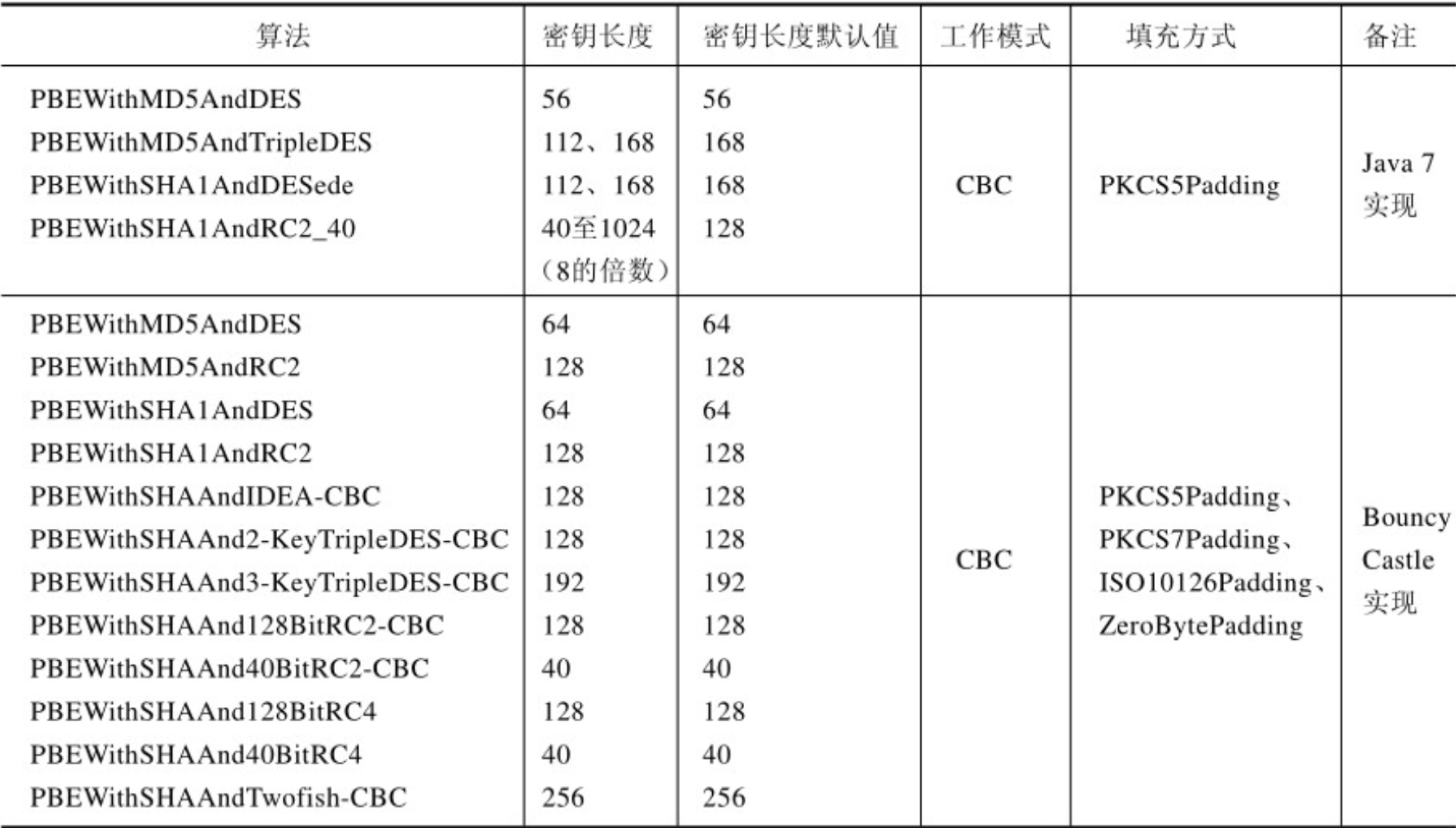
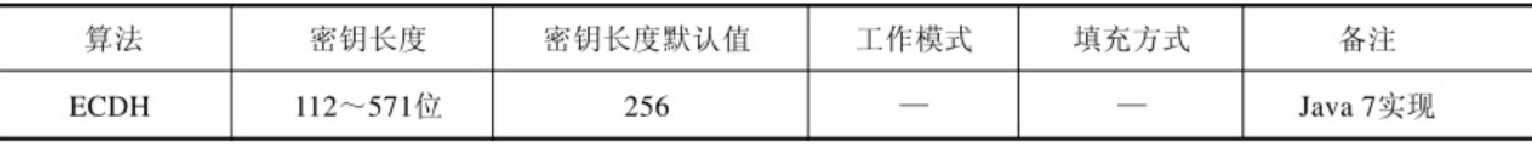
- 13#几种对称加密所支持的规格
- RSA签名算法
- DSA签名算法
- ECDSA签名算法
- PBE是一种基于口令和盐的对称加密算法,在初始化盐时,必须采用随机的方式SecureRandom构建,最终产生一个8个字节的字节数组,加解密如下
- #14有关HTTPS的数字证书验证流程
- 第一阶段为商榷算法
- 第二阶段为验证证书
- 第三阶段为产生密钥
- 第四阶段构建完成主密钥后,开始终止握手协议交互
- 第五阶段为加密交互
- 以上为所有内容!
1#消息摘要算法
MessageDigest,支持MD2,MD5,SHA-1(SHA),SHA-256,SHA-384,SHA-512
6种消息摘要算法,不区分大小写
byte[] input = "caishuzhan".getBytes();try {MessageDigest messageDigest = MessageDigest.getInstance("SHA");messageDigest.update(input);byte[] digest = messageDigest.digest();} catch (NoSuchAlgorithmException e) {e.printStackTrace();}
以输入流的方式去获取摘要DigestInputStream
byte[] input = "caishuzhan".getBytes();try {MessageDigest messageDigest = MessageDigest.getInstance("MD5");DigestInputStream stream = new DigestInputStream(new ByteArrayInputStream(input), messageDigest);int read = stream.read(input, 0, input.length);byte[] digest = stream.getMessageDigest().digest();stream.close();} catch (Exception e) {e.printStackTrace();}
以输出流的方式更改要加密的源数据DigestOnputStream
byte[] input = "caishuzhan".getBytes();try {MessageDigest messageDigest = MessageDigest.getInstance("MD5");ByteArrayOutputStream outputStream = new ByteArrayOutputStream();DigestOutputStream stream = new DigestOutputStream(outputStream, messageDigest);stream.write(input);byte[] digest = stream.getMessageDigest().digest();stream.flush();stream.close();} catch (Exception e) {e.printStackTrace();}
2#算法参数
try {AlgorithmParameterGenerator generator = AlgorithmParameterGenerator.getInstance("DSA");generator.init(512);AlgorithmParameters parameters = generator.generateParameters();byte[] bytes = parameters.getEncoded();AlgorithmParameters ap = AlgorithmParameters.getInstance("DSA");BigInteger bigInteger = new BigInteger(bytes);ap.init(bigInteger.toByteArray());byte[] encoded = ap.getEncoded();} catch (Exception e) {e.printStackTrace();}
3#KeyPair,非堆称加密的密钥对,java7提供了DH,ECDH,RSA,ECDSA,DSA等多种非对称加密和签名算法的实现,如构建DH密钥对时,密钥的长度要求为64位的倍数,范围为512-1024,默认长度为1024.生成一个DSA密钥对:
try {KeyPairGenerator generator = KeyPairGenerator.getInstance("DSA");generator.initialize(1024);KeyPair keyPair = generator.generateKeyPair();} catch (Exception e) {e.printStackTrace();}
构建密钥对与还原密钥
try {KeyPairGenerator generator = KeyPairGenerator.getInstance("RSA");generator.initialize(1024);KeyPair keyPair = generator.generateKeyPair();byte[] bytes = keyPair.getPrivate().getEncoded();PKCS8EncodedKeySpec keySpec = new PKCS8EncodedKeySpec(bytes);KeyFactory factory = KeyFactory.getInstance("RSA");PrivateKey privateKey = factory.generatePrivate(keySpec);System.out.println("isEquels " +MessageDigest.isEqual(privateKey.getEncoded(),bytes));} catch (Exception e) {e.printStackTrace();}
结合随机数对象构建对称密钥,Java 7 支持AES密钥长度128,192,256位
KeyGenerator generator = KeyGenerator.getInstance("DES");generator.init(56,new SecureRandom());SecretKey secretKey = generator.generateKey();
4#Signature签名,数字签名算法主要包括RSA,DSA,ECDSA三种,生成签名与验证
byte[] data = "caishuzhan".getBytes();KeyPairGenerator dsa = KeyPairGenerator.getInstance("DSA");dsa.initialize(1024);KeyPair keyPair = dsa.generateKeyPair();Signature signature = Signature.getInstance(dsa.getAlgorithm());signature.initSign(keyPair.getPrivate());signature.update(data);byte[] sign = signature.sign();signature.initVerify(keyPair.getPublic());signature.update(data);boolean verify = signature.verify(sign);
利用SignedObject生成签名与验证
byte[] data = "caishuzhan".getBytes();KeyPairGenerator rsa = KeyPairGenerator.getInstance("DSA");rsa.initialize(1024);KeyPair keyPair = rsa.generateKeyPair();Signature signature = Signature.getInstance(rsa.getAlgorithm());SignedObject signedObject = new SignedObject(data,keyPair.getPrivate(),signature);byte[] sign = signedObject.getSignature();boolean verify = signedObject.verify(keyPair.getPublic(), signature);
数字时间戳Timestamp
CertificateFactory factory = CertificateFactory.getInstance("X509");CertPath certPath = factory.generateCertPath(new FileInputStream(""));Timestamp timestamp = new Timestamp(new Date(),certPath);
5#KeyStore用于存储密钥和证书,从keyStore里根据别名获取私钥
FileInputStream is = new FileInputStream("/Users/caishuzhan/Desktop/workspace/Awards/app/YHGJ.jks");KeyStore keyStore = KeyStore.getInstance(KeyStore.getDefaultType());keyStore.load(is,"123456".toCharArray());is.close();PrivateKey privateKey = (PrivateKey) keyStore.getKey("123456","123456".toCharArray());//或者KeyStore.PrivateKeyEntry entry = (KeyStore.PrivateKeyEntry) keyStore.getEntry("123456",new KeyStore.PasswordProtection("123456".toCharArray()));PrivateKey entryPrivateKey = entry.getPrivateKey();
6#Mac,安全消息摘要算法,区别与MessageDigest,需要有一个共享的密钥来生成,支持HmacMD5,
HmacSHA1,HmacSHA256,HmacSHA384,HmacSHA512 5种消息摘要算法
byte[] data = "caishuzhan".getBytes();KeyGenerator keyGenerator = KeyGenerator.getInstance("HmacMD5");SecretKey secretKey = keyGenerator.generateKey();Mac mac = Mac.getInstance(secretKey.getAlgorithm());mac.init(secretKey);byte[] bytes = mac.doFinal(data);
7#SecretKeyFactory,密钥工厂,用于生产密钥,用于byte数组还原成密钥对象
KeyGenerator generator = KeyGenerator.getInstance("DES");SecretKey secretKey = generator.generateKey();byte[] encoded = secretKey.getEncoded();SecretKeyFactory keyFactory = SecretKeyFactory.getInstance(secretKey.getAlgorithm());SecretKey key = keyFactory.generateSecret(new DESKeySpec(encoded));
8#加解密的核心Cipher,参数transformation的格式“算法/工作模式/填充模式”,不同的算法支持不同的工作模式和填充模式
byte[] data = "caishuzhan".getBytes();KeyGenerator generator = KeyGenerator.getInstance("DES");SecretKey secretKey = generator.generateKey();Cipher cipher = Cipher.getInstance("DES");//cipher.init(Cipher.WRAP_MODE,secretKey);//byte[] wrap = cipher.wrap(secretKey);// cipher.init(Cipher.UNWRAP_MODE,secretKey);// Key key = cipher.unwrap(wrap, "DES", Cipher.SECRET_KEY);cipher.init(Cipher.ENCRYPT_MODE,secretKey);byte[] doFinal = cipher.doFinal(data);cipher.init(Cipher.DECRYPT_MODE,secretKey);byte[] aFinal = cipher.doFinal(doFinal);
CipherInputStream和CipherOutputStream把加密内容序列化和反序列化
File file = new File("/Users/caishuzhan/Desktop/cipher.txt");if (!file.exists()){file.createNewFile();}String data = "caishuzhan";KeyGenerator generator = KeyGenerator.getInstance("DES");SecretKey secretKey = generator.generateKey();Cipher cipher = Cipher.getInstance("DES");cipher.init(Cipher.ENCRYPT_MODE,secretKey);CipherOutputStream outputStream = new CipherOutputStream(new FileOutputStream(file),cipher);DataOutputStream dataOutputStream = new DataOutputStream(outputStream);dataOutputStream.writeUTF(data);dataOutputStream.flush();dataOutputStream.close();cipher.init(Cipher.DECRYPT_MODE,secretKey);CipherInputStream inputStream = new CipherInputStream(new FileInputStream(file),cipher);DataInputStream dataInputStream = new DataInputStream(inputStream);String s = dataInputStream.readUTF();dataInputStream.close();
9#KeySpec,密钥规范,用于还原公私钥和对称密钥,X509EncodedKeySpec用于非对称的公钥构建,PKCS8EncodedKeySpec用于非对称的私钥构建,SecretKeySpec用于对称密钥构建,DESKeySpec指定DES算法,DESedeKeySpec指定三重DES加密算法,PBEKeySpec指定PBE算法
KeyGenerator generator = KeyGenerator.getInstance("DES");SecretKey secretKey = generator.generateKey();byte[] encoded = secretKey.getEncoded();SecretKey key = new SecretKeySpec(encoded,secretKey.getAlgorithm());
10#证书Certificate,关于数字证书,其实就是机构给网站的一张可用凭证,用来表明发送者是否为真正的发送者,里面有传输时用到的公钥,如下
加载证书
CertificateFactory factory =CertificateFactory.getInstance("X.509");FileInputStream fileInputStream = new FileInputStream("");Certificate certificate = factory.generateCertificate(fileInputStream);fileInputStream.close();
构建证书签名
KeyStore keyStore = KeyStore.getInstance("jks");keyStore.load(new FileInputStream("D://test.jks"),"123456".toCharArray());X509Certificate certificate = (X509Certificate) keyStore.getCertificate("alias");Signature signature = Signature.getInstance(certificate.getSigAlgName());
证书撤销列表CRL,用与验证证书是否被撤销或者无效
CertificateFactory factory = CertificateFactory.getInstance("X.509");FileInputStream fileInputStream = new FileInputStream("");Certificate certificate = factory.generateCertificate(fileInputStream);CRL crl = factory.generateCRL(fileInputStream);crl.isRevoked(certificate);
11#SSL,构建KeyManagerFactory
KeyManagerFactory factory =KeyManagerFactory.getInstance("SunX509");FileInputStream is = new FileInputStream("/Users/caishuzhan/Desktop/workspace/Awards/app/YHGJ.jks");KeyStore keyStore = KeyStore.getInstance("jks");keyStore.load(is,"123456".toCharArray());is.close();factory.init(keyStore,"123456".toCharArray());
构建信任工厂
TrustManagerFactory factory = TrustManagerFactory.getInstance("SunX509");FileInputStream is = new FileInputStream("/Users/caishuzhan/Desktop/workspace/Awards/app/YHGJ.jks");KeyStore keyStore = KeyStore.getInstance("jks");keyStore.load(is,"123456".toCharArray());is.close();factory.init(keyStore);
构建SSLSocketFactory
public static KeyStore getKeyStore(String path,String password){KeyStore keyStore = null;try {FileInputStream is = new FileInputStream(path);keyStore = KeyStore.getInstance("jks");keyStore.load(is,password.toCharArray());is.close();} catch (Exception e) {e.printStackTrace();}return keyStore;}public static SSLSocketFactory getSSLSocketFactory(String password, String keyStorePath,String trustKeyStorePath){try {KeyStore keyStore = getKeyStore(keyStorePath,password);KeyManagerFactory keyManagerFactory =KeyManagerFactory.getInstance("SunX509");keyManagerFactory.init(keyStore,password.toCharArray());KeyStore trustKeyStore = getKeyStore(trustKeyStorePath,password);TrustManagerFactory trustManagerFactory = TrustManagerFactory.getInstance("SunX509");trustManagerFactory.init(trustKeyStore);SSLContext ctx = SSLContext.getInstance("SSL");ctx.init(keyManagerFactory.getKeyManagers(),trustManagerFactory.getTrustManagers(),null);SSLSocketFactory sf = ctx.getSocketFactory();return sf;} catch (Exception e) {e.printStackTrace();}return null;}
与服务端建立SSLSocket连接并且获取证书链
public Certificate[] getCertificates(){try {SSLSocketFactory factory = (SSLSocketFactory) SSLSocketFactory.getDefault();SSLSocket sslSocket = (SSLSocket) factory.createSocket();sslSocket.startHandshake();SSLSession session = sslSocket.getSession();sslSocket.close();return session.getPeerCertificates();} catch (Exception e) {System.out.println("e :"+ e.getMessage());e.printStackTrace();}return null;}
12#Base64算法,约为原文的4/3倍,字符数以4为单位的整数倍,java.util的基本实现
byte[] encode = Base64.getEncoder().encode("caishuzhan".getBytes());byte[] decode = Base64.getDecoder().decode(encode);
13#几种对称加密所支持的规格
RSA签名算法
DSA签名算法
ECDSA签名算法
PBE是一种基于口令和盐的对称加密算法,在初始化盐时,必须采用随机的方式SecureRandom构建,最终产生一个8个字节的字节数组,加解密如下
//明文String data = "caishuzhan";//口令String password = "password";SecureRandom random = new SecureRandom();byte[] salt = random.generateSeed(8);PBEKeySpec keySpec = new PBEKeySpec(password.toCharArray());SecretKeyFactory keyFactory = SecretKeyFactory.getInstance("PBEWithMD5AndDES");SecretKey secretKey = keyFactory.generateSecret(keySpec);PBEParameterSpec parameterSpec = new PBEParameterSpec(salt,100);Cipher cipher =Cipher.getInstance("PBEWithMD5AndDES");cipher.init(Cipher.ENCRYPT_MODE,secretKey,parameterSpec);byte[] doFinal = cipher.doFinal(data.getBytes());cipher.init(Cipher.DECRYPT_MODE,secretKey,parameterSpec);byte[] result = cipher.doFinal(doFinal);
#14有关HTTPS的数字证书验证流程
第一阶段为商榷算法
1)客户端产生随机数RNC,这个随机数为后续构建密钥做准备
2)客户端将自身支持的SSL(版本和种类),算法信息和随机数RNC发送给服务器
3)服务器接收到以后产生随机数RNS,为后续构建密钥做准备
4)服务器将自身支持的SSL(版本和种类),算法信息和随机数RNS 和 服务器证书 甚至包含客户端证书的请求(双向认证时)回应给客户端
此时,确认双方交互时所使用的加密算法
第二阶段为验证证书
1)客户端将该证书发送至认证机构,认证机构验证证书
2)认证机构返回结果,认证失败时提示警告
此时,认证完毕,客户端和服务器可以进行以服务端单向认证为基础的加密交互,如果服务端对客户端的身份有要求会要求客户端提供证书(双向认证时),一般情况下客户端证书不是必需,双向认证是电子商务确保安全的必要环节
第三阶段为产生密钥
1)客户端产生随机数,做为预备密钥PMS
2)客户端用服务器证书中的公钥对PMS加密
3)客户端将PMS加密信息发送到服务器
4)服务器使用私钥对信息解密获得PMS
5)客户端使用RNC,RNS和PMS构建主密钥MS
6)服务器使用RNC,RNS和PMS构建主密钥MS
5,6不存在次序关系,实际上异步完成
第四阶段构建完成主密钥后,开始终止握手协议交互

如果上述一些列操作中任何一端受到干扰发生异常,则重新进入协商算法阶段
第五阶段为加密交互

所有握手交互的现实封装在SSL层