Exploit Title: SQL injection
Date: 2022-07-06
Software Link: https://www.sourcecodester.com/download-code?nid=14510&title=Online+Tours+%26+Travels+management+system+project+using+PHP+and+MySQL
Version: v1.0
Tested on: Linux Apache/2.4.38 MariaDB 10.3.34 php7.2.20
1. Vulnerability analysis
The file path that exists in vulnerabilities is: /admin/operations/packages.php. The INSERT sql satement(line 13 and line 14) did not filter the input val-username parameter, and brought it directly into the database to query, resulting in a SQL injection vulnerability: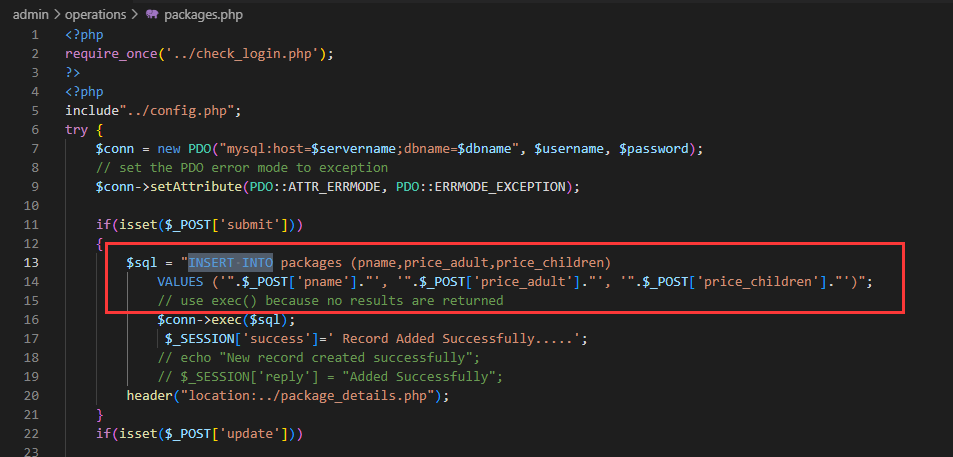
2. POC
To trigger the vulerability, we need first log in to the background of the website as an administrator, the administrator account password is located “Username and Password.txt” under the Credentials folder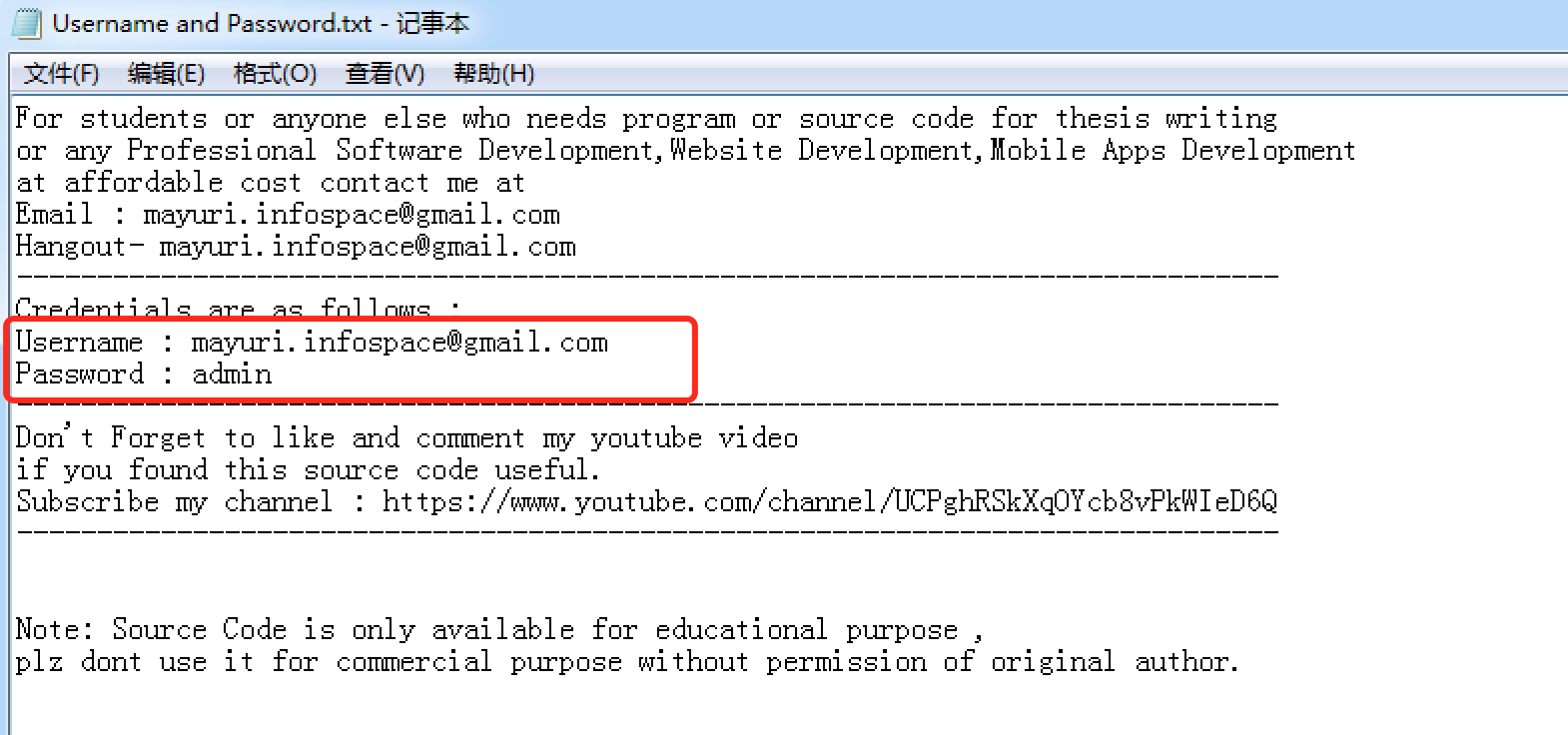
Then, Click “Package Management” and “Add Package Details” in order: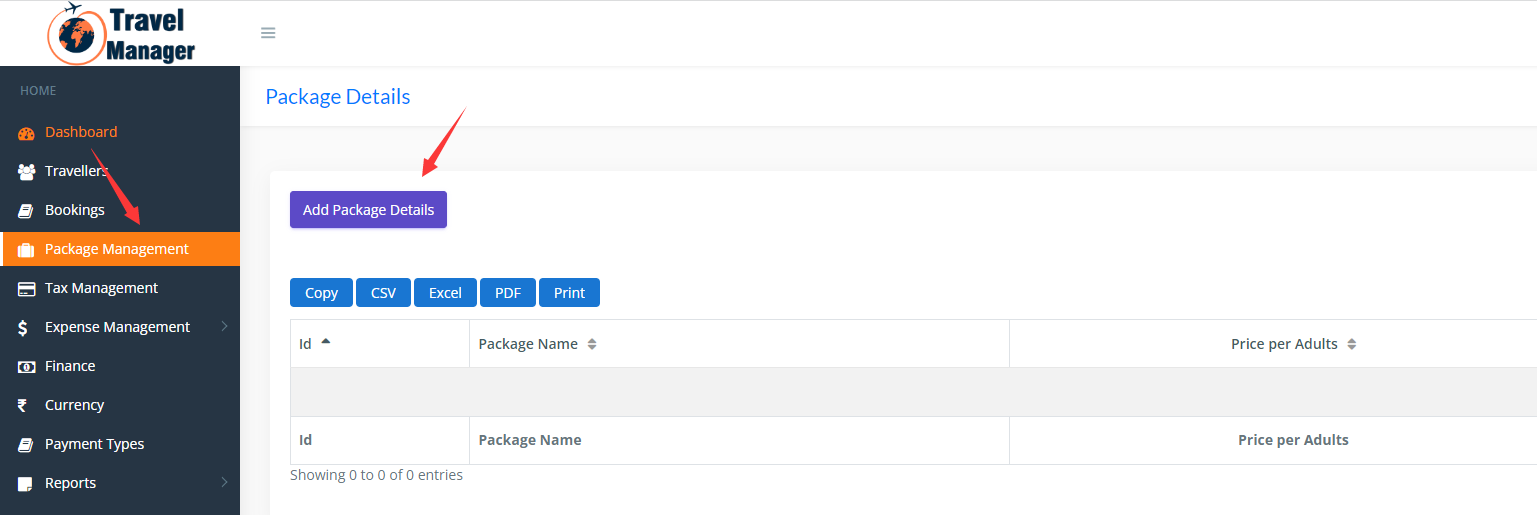
Fill in the form, Click “Save” and grab the datapackage.
The package looks like follow picture(the target is my own docker):
change the pname parameter into
test', (select sleep(2.5)), 44);--+
and click “Send”, the response will be received after 2.5s(2500 milis) wait.
it shows that this place could be used to leak the database.

