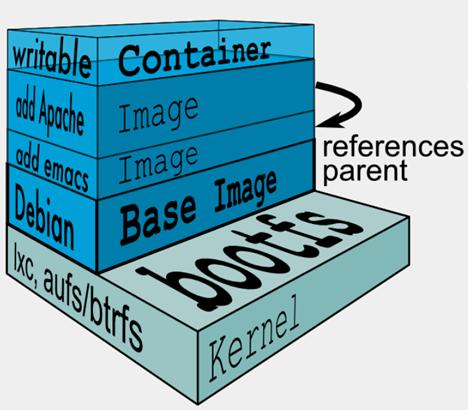
镜像组成
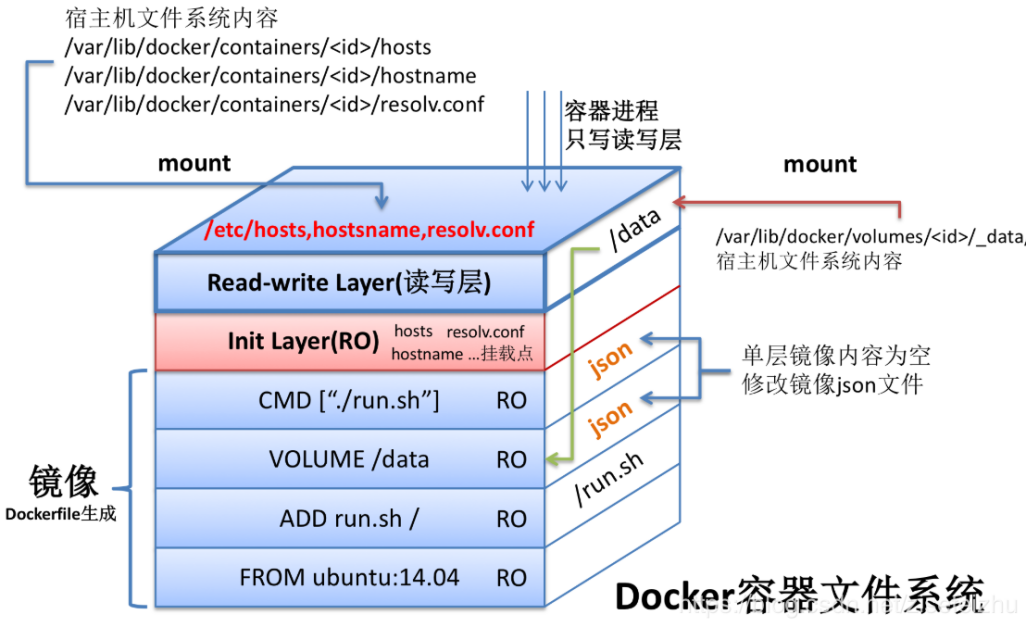
docker镜像由多个只读层叠加面成,启动容器时,docker会加载只读镜像层并在镜像栈顶部加一个读写层
如果运行中的容器修改了现有的一个已经存在的文件,那该文件将会从读写层下面的只读层复制到读写层,该文件版本仍然存在,只是已经被读写层中该文件的副本所隐藏,此即“写时复制(COW)”机制
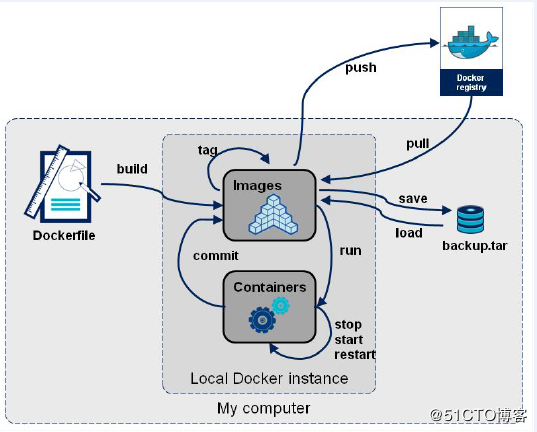
dockerfile —> image —> registry
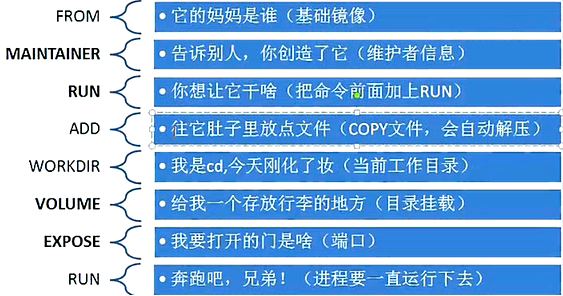
Dockerfile 文件有自己的书写格式和支持的命令,常用的Dockerfile 指令有:FROM 指定基镜像。MAINTAINER 设置镜像的作者信息,如作者姓名、邮箱等。COPY 将文件从本地复制到镜像,拷贝前需要保证本地源文件存在。ADD 与 COPY 类似,复制文件到镜像。不同的是,如果文件是归档文件(tar, zip, tgz, xz 等),会被自动解压。ENV 设置环境变量,格式: ENV key=value或ENV key value,运行容器后,可直接在容器中使用。EXPOSE 暴露容器中指定的端口,只是一个声明,主要用户了解应用监听的端口。VOLUME 挂载卷到容器,需要注意的是,保存镜像时不会保存卷中的数据。WORKDIR 设置当前工作目录,后续各层的当前目录都被指定。RUN 在容器中运行指定的命令。CMD 容器启动时运行的命令。Dockerfile 中可以有多个 CMD 指令,但只有最后一个生效。CMD 可以被 docker run 之后的参数替换。ENTRYPOINT 设置容器启动时运行的命令。Dockerfile 中可以有多个 ENTRYPOINT 指令,但只有最后一个生效。CMD 或 docker run 之后的参数会被当做参数传递给 ENTRYPOINT,这个是与CMD的区别。
Dockerfile整体就两类语句组成:
# Comment 注释信息
Instruction arguments 指令 参数,一行一个指令
Dockerfile文件名首字母必须大写
Dockerfile指令不区分大小写,但是为方便和参数做区分,通常指令使用大写字母
Dockerfile中指令按顺序从上至下依次执行
Dockerfile中第一个非注释行必须是FROM指令,用来指定制作当前镜像依据的是哪个基础镜像。
Dockerfile中需要调用的文件必须跟Dockerfile文件在同一目录下,或者在其子目录下,父目录或者其它路径无效
引用
https://www.cnblogs.com/edisonchou/p/dockerfile_inside_introduction.html
示例
FROM centos
#1、指定工作目录
WORKDIR /usr/local
#2、指定版本信息
ENV JAVA=jdk-8u181-linux-x64 TOMCAT=apache-tomcat-8.0.53
#3、创建目录,多个命令尽量在一个Dockerfile 命令中完成,避免构建多层,做好清理工作
RUN mkdir java \
&& mkdir tomcat \
&& cd java \
&& yum -y install wget \
&& wget -q -O jdk-linux.rpm --no-check-certificate --no-cookies --header "Cookie: oraclelicense=accept-securebackup-cookie" http://download.oracle.com/otn-pub/java/jdk/8u181-b13/96a7b8442fe848ef90c96a2fad6ed6d1/${JAVA}.rpm \
&& rpm -ivh jdk-linux.rpm \
&& rm -rf jdk-linux.rpm \
&& cd ../tomcat \
&& wget -q http://apache.claz.org/tomcat/tomcat-8/v8.0.53/bin/${TOMCAT}.tar.gz \
&& tar -zxv -f ${TOMCAT}.tar.gz \
&& rm -rf ${TOMCAT}.tar.gz \
&& rm -rf ${TOMCAT}/webapps/ROOT \
&& yum -y remove wget;
#4、把上下文目录中的 war 复制进来
ONBUILD COPY *.war ./tomcat/${TOMCAT}/webapps/
#5、启动容器
ONBUILD ENTRYPOINT ["/usr/local/tomcat/apache-tomcat-8.0.53/bin/catalina.sh","run"]
#6、基础环境构建完毕
CMD ["sh","-c","echo Environment construction completed"]
nginx官方docker镜像
nginxinc/docker-nginx
https://github.com/nginxinc/docker-nginx/blob/master/stable/alpine/Dockerfile
示列
https://blog.51cto.com/dengaosky/2426483
镜像联合构建
要求:
Docker 17.05或更高版本
https://blog.csdn.net/boling_cavalry/article/details/90742657
https://docs.docker.com/develop/develop-images/multistage-build/
编写Dockerfiles最佳实践(Docker 18.09).pdf
编写Dockerfiles最佳实践(Docker 18.09).pdf
基础镜像
[root@riyimei docker]# cat Dockerfile
FROM centos:7
ENV container docker
RUN (cd /lib/systemd/system/sysinit.target.wants/; for i in *; do [ $i == \
systemd-tmpfiles-setup.service ] || rm -f $i; done); \
rm -f /lib/systemd/system/multi-user.target.wants/*;\
rm -f /etc/systemd/system/*.wants/*;\
rm -f /lib/systemd/system/local-fs.target.wants/*; \
rm -f /lib/systemd/system/sockets.target.wants/*udev*; \
rm -f /lib/systemd/system/sockets.target.wants/*initctl*; \
rm -f /lib/systemd/system/basic.target.wants/*;\
rm -f /lib/systemd/system/anaconda.target.wants/*;
VOLUME [ "/sys/fs/cgroup" ]
CMD ["/usr/sbin/init"]
[root@riyimei docker]# docker build --rm -t local/c7-systemd .
Sending build context to Docker daemon 2.56kB
Step 1/5 : FROM centos:7
7: Pulling from library/centos
ab5ef0e58194: Pull complete
Digest: sha256:4a701376d03f6b39b8c2a8f4a8e499441b0d567f9ab9d58e4991de4472fb813c
Status: Downloaded newer image for centos:7
---> 5e35e350aded
Step 2/5 : ENV container docker
---> Running in 49fc2862ce9e
Removing intermediate container 49fc2862ce9e
---> 33822cd236ef
Step 3/5 : RUN (cd /lib/systemd/system/sysinit.target.wants/; for i in *; do [ $i == systemd-tmpfiles-setup.service ] || rm -f $i; done); rm -f /lib/systemd/system/multi-user.target.wants/*;rm -f /etc/systemd/system/*.wants/*;rm -f /lib/systemd/system/local-fs.target.wants/*; rm -f /lib/systemd/system/sockets.target.wants/*udev*; rm -f /lib/systemd/system/sockets.target.wants/*initctl*; rm -f /lib/systemd/system/basic.target.wants/*;rm -f /lib/systemd/system/anaconda.target.wants/*;
---> Running in c4b4f8110113
Removing intermediate container c4b4f8110113
---> 68a87c415a5b
Step 4/5 : VOLUME [ "/sys/fs/cgroup" ]
---> Running in 3869cc1fd8f7
Removing intermediate container 3869cc1fd8f7
---> 74aad90ab141
Step 5/5 : CMD ["/usr/sbin/init"]
---> Running in 925030db2aba
Removing intermediate container 925030db2aba
---> 900b71d7e1bb
Successfully built 900b71d7e1bb
Successfully tagged local/c7-systemd:latest
手动打包系统镜像
tar --numeric-owner --exclude=/proc --exclude=/sys --exclude=/mnt --exclude=/tmp --exclude=/var/cache --exclude=/usr/share/{foomatic,backgrounds,perl5,fonts,cups,qt4,groff,kde4,icons,pixmaps,emacs,gnome-background-properties,sounds,gnome,games,desktop-directories} --exclude=/var/log -zcvf /tmp/rhel7.4-Base.tar.gz /
https://github.com/moby/moby/tree/master/contrib
https://raw.githubusercontent.com/moby/moby/master/contrib/mkimage-yum.sh
centos6
rpm -Uvh http://dl.Fedoraproject.org/pub/epel/6/x86_64/epel-release-6-8.noarch.rpm
yum -y install docker-io
./mkimage-yum.sh -y /etc/yum.conf centos6
centos7
mkimage-yum.sh
#!/usr/bin/env bash
#
# Create a base CentOS Docker image.
#
# This script is useful on systems with yum installed (e.g., building
# a CentOS image on CentOS). See contrib/mkimage-rinse.sh for a way
# to build CentOS images on other systems.
set -e
usage() {
cat << EOOPTS
$(basename $0) [OPTIONS] <name>
OPTIONS:
-p "<packages>" The list of packages to install in the container.
The default is blank. Can use multiple times.
-g "<groups>" The groups of packages to install in the container.
The default is "Core". Can use multiple times.
-y <yumconf> The path to the yum config to install packages from. The
default is /etc/yum.conf for Centos/RHEL and /etc/dnf/dnf.conf for Fedora
-t <tag> Specify Tag information.
default is reffered at /etc/{redhat,system}-release
EOOPTS
exit 1
}
# option defaults
yum_config=/etc/yum.conf
if [ -f /etc/dnf/dnf.conf ] && command -v dnf &> /dev/null; then
yum_config=/etc/dnf/dnf.conf
alias yum=dnf
fi
# for names with spaces, use double quotes (") as install_groups=('Core' '"Compute Node"')
install_groups=()
install_packages=()
version=
while getopts ":y:p:g:t:h" opt; do
case $opt in
y)
yum_config=$OPTARG
;;
h)
usage
;;
p)
install_packages+=("$OPTARG")
;;
g)
install_groups+=("$OPTARG")
;;
t)
version="$OPTARG"
;;
\?)
echo "Invalid option: -$OPTARG"
usage
;;
esac
done
shift $((OPTIND - 1))
name=$1
if [[ -z $name ]]; then
usage
fi
# default to Core group if not specified otherwise
if [ ${#install_groups[*]} -eq 0 ]; then
install_groups=('Core')
fi
target=$(mktemp -d --tmpdir $(basename $0).XXXXXX)
set -x
mkdir -m 755 "$target"/dev
mknod -m 600 "$target"/dev/console c 5 1
mknod -m 600 "$target"/dev/initctl p
mknod -m 666 "$target"/dev/full c 1 7
mknod -m 666 "$target"/dev/null c 1 3
mknod -m 666 "$target"/dev/ptmx c 5 2
mknod -m 666 "$target"/dev/random c 1 8
mknod -m 666 "$target"/dev/tty c 5 0
mknod -m 666 "$target"/dev/tty0 c 4 0
mknod -m 666 "$target"/dev/urandom c 1 9
mknod -m 666 "$target"/dev/zero c 1 5
# amazon linux yum will fail without vars set
if [ -d /etc/yum/vars ]; then
mkdir -p -m 755 "$target"/etc/yum
cp -a /etc/yum/vars "$target"/etc/yum/
fi
if [[ -n "$install_groups" ]]; then
yum -c "$yum_config" --installroot="$target" --releasever=/ --setopt=tsflags=nodocs \
--setopt=group_package_types=mandatory -y groupinstall "${install_groups[@]}"
fi
if [[ -n "$install_packages" ]]; then
yum -c "$yum_config" --installroot="$target" --releasever=/ --setopt=tsflags=nodocs \
--setopt=group_package_types=mandatory -y install "${install_packages[@]}"
fi
yum -c "$yum_config" --installroot="$target" -y clean all
cat > "$target"/etc/sysconfig/network << EOF
NETWORKING=yes
HOSTNAME=localhost.localdomain
EOF
# effectively: febootstrap-minimize --keep-zoneinfo --keep-rpmdb --keep-services "$target".
# locales
rm -rf "$target"/usr/{{lib,share}/locale,{lib,lib64}/gconv,bin/localedef,sbin/build-locale-archive}
# docs and man pages
rm -rf "$target"/usr/share/{man,doc,info,gnome/help}
# cracklib
rm -rf "$target"/usr/share/cracklib
# i18n
rm -rf "$target"/usr/share/i18n
# yum cache
rm -rf "$target"/var/cache/yum
mkdir -p --mode=0755 "$target"/var/cache/yum
# sln
rm -rf "$target"/sbin/sln
# ldconfig
rm -rf "$target"/etc/ld.so.cache "$target"/var/cache/ldconfig
mkdir -p --mode=0755 "$target"/var/cache/ldconfig
if [ -z "$version" ]; then
for file in "$target"/etc/{redhat,system}-release; do
if [ -r "$file" ]; then
version="$(sed 's/^[^0-9\]*\([0-9.]\+\).*$/\1/' "$file")"
break
fi
done
fi
if [ -z "$version" ]; then
echo >&2 "warning: cannot autodetect OS version, using '$name' as tag"
version=$name
fi
tar --numeric-owner -c -C "$target" . | docker import - $name:$version
docker run -i -t --rm $name:$version /bin/bash -c 'echo success'
rm -rf "$target"
[root@master ~]# ll /etc/yum.repos.d/
total 12
-rw-r--r--. 1 root root 2523 May 6 00:07 CentOS-Base.repo
-rw-r--r-- 1 root root 1946 Jun 16 2020 elrepo.repo
-rw-r--r--. 1 root root 664 Jan 11 2020 epel.repo
镜像名称需要小写
./mkimage-yum.sh -y /etc/yum.conf centos7
[BEGIN] 2021-05-06 23:25:13
[root@master image]# ./mkimage-yum.sh -y /etc/yum.conf centos7
+ mkdir -m 755 /tmp/mkimage-yum.sh.u7pzDD/dev
+ mknod -m 600 /tmp/mkimage-yum.sh.u7pzDD/dev/console c 5 1
+ mknod -m 600 /tmp/mkimage-yum.sh.u7pzDD/dev/initctl p
+ mknod -m 666 /tmp/mkimage-yum.sh.u7pzDD/dev/full c 1 7
+ mknod -m 666 /tmp/mkimage-yum.sh.u7pzDD/dev/null c 1 3
+ mknod -m 666 /tmp/mkimage-yum.sh.u7pzDD/dev/ptmx c 5 2
+ mknod -m 666 /tmp/mkimage-yum.sh.u7pzDD/dev/random c 1 8
+ mknod -m 666 /tmp/mkimage-yum.sh.u7pzDD/dev/tty c 5 0
+ mknod -m 666 /tmp/mkimage-yum.sh.u7pzDD/dev/tty0 c 4 0
+ mknod -m 666 /tmp/mkimage-yum.sh.u7pzDD/dev/urandom c 1 9
+ mknod -m 666 /tmp/mkimage-yum.sh.u7pzDD/dev/zero c 1 5
+ '[' -d /etc/yum/vars ']'
+ mkdir -p -m 755 /tmp/mkimage-yum.sh.u7pzDD/etc/yum
+ cp -a /etc/yum/vars /tmp/mkimage-yum.sh.u7pzDD/etc/yum/
+ [[ -n Core ]]
+ yum -c /etc/yum.conf --installroot=/tmp/mkimage-yum.sh.u7pzDD --releasever=/ --setopt=tsflags=nodocs --setopt=group_package_types=mandatory -y groupinstall Core
There is no installed groups file.
Maybe run: yum groups mark convert (see man yum)
base | 3.6 kB 00:00:00
extras | 2.9 kB 00:00:00
updates | 2.9 kB 00:00:00
base/7/x86_64/primary_db FAILED
http://mirrors.aliyuncs.com/centos/7/os/x86_64/repodata/6d0c3a488c282fe537794b5946b01e28c7f44db79097bb06826e1c0c88bad5ef-primary.sqlite.bz2: [Errno 14] curl#6 - "Could not resolve host: mirrors.aliyuncs.com; Unknown error"
Trying other mirror.
base/7/x86_64/primary_db FAILED
http://mirrors.cloud.aliyuncs.com/centos/7/os/x86_64/repodata/6d0c3a488c282fe537794b5946b01e28c7f44db79097bb06826e1c0c88bad5ef-primary.sqlite.bz2: [Errno 14] curl#6 - "Could not resolve host: mirrors.cloud.aliyuncs.com; Unknown error"
Trying other mirror.
(1/4): extras/7/x86_64/primary_db | 236 kB 00:00:00
(2/4): base/7/x86_64/group_gz | 153 kB 00:00:00
(3/4): updates/7/x86_64/primary_db | 8.0 MB 00:00:01
(4/4): base/7/x86_64/primary_db | 6.1 MB 00:00:01
Resolving Dependencies
--> Running transaction check
Dependencies Resolved
=================================================================================================================================================
Package Arch Version Repository Size
=================================================================================================================================================
Installing for group install "Core":
audit x86_64 2.8.5-4.el7 base 256 k
basesystem noarch 10.0-7.el7.centos base 5.0 k
bash x86_64 4.2.46-34.el7 base 1.0 M
btrfs-progs x86_64 4.9.1-1.el7 base 678 k
coreutils x86_64 8.22-24.el7_9.2 updates 3.3 M
cronie x86_64 1.4.11-23.el7 base 92 k
curl x86_64 7.29.0-59.el7_9.1 updates 271 k
dhclient x86_64 12:4.2.5-82.el7.centos base 286 k
e2fsprogs x86_64 1.42.9-19.el7 base 701 k
filesystem x86_64 3.2-25.el7 base 1.0 M
firewalld noarch 0.6.3-13.el7_9 updates 449 k
glibc x86_64 2.17-324.el7_9 updates 3.6 M
hostname x86_64 3.13-3.el7_7.1 base 17 k
initscripts x86_64 9.49.53-1.el7_9.1 updates 440 k
iproute x86_64 4.11.0-30.el7 base 805 k
iprutils x86_64 2.4.17.1-3.el7_7 updates 243 k
iptables x86_64 1.4.21-35.el7 base 432 k
iputils x86_64 20160308-10.el7 base 148 k
irqbalance x86_64 3:1.0.7-12.el7 base 45 k
kbd x86_64 1.15.5-15.el7 base 348 k
kexec-tools x86_64 2.0.15-51.el7_9.2 updates 351 k
less x86_64 458-9.el7 base 120 k
man-db x86_64 2.6.3-11.el7 base 832 k
ncurses x86_64 5.9-14.20130511.el7_4 base 304 k
openssh-clients x86_64 7.4p1-21.el7 base 655 k
openssh-server x86_64 7.4p1-21.el7 base 459 k
parted x86_64 3.1-32.el7 base 609 k
passwd x86_64 0.79-6.el7 base 106 k
plymouth x86_64 0.8.9-0.34.20140113.el7.centos base 116 k
policycoreutils x86_64 2.5-34.el7 base 917 k
procps-ng x86_64 3.3.10-28.el7 base 291 k
rootfiles noarch 8.1-11.el7 base 7.3 k
rpm x86_64 4.11.3-45.el7 base 1.2 M
rsyslog x86_64 8.24.0-57.el7_9 updates 621 k
selinux-policy-targeted noarch 3.13.1-268.el7_9.2 updates 7.0 M
setup noarch 2.8.71-11.el7 base 166 k
shadow-utils x86_64 2:4.6-5.el7 base 1.2 M
sudo x86_64 1.8.23-10.el7_9.1 updates 843 k
systemd x86_64 219-78.el7_9.3 updates 5.1 M
tar x86_64 2:1.26-35.el7 base 846 k
tuned noarch 2.11.0-11.el7_9 updates 269 k
util-linux x86_64 2.23.2-65.el7_9.1 updates 2.0 M
vim-minimal x86_64 2:7.4.629-8.el7_9 updates 443 k
xfsprogs x86_64 4.5.0-22.el7 base 897 k
yum noarch 3.4.3-168.el7.centos base 1.2 M
Installing for dependencies:
acl x86_64 2.2.51-15.el7 base 81 k
audit-libs x86_64 2.8.5-4.el7 base 102 k
bc x86_64 1.06.95-13.el7 base 115 k
bind-export-libs x86_64 32:9.11.4-26.P2.el7_9.5 updates 1.1 M
binutils x86_64 2.27-44.base.el7 base 5.9 M
bzip2-libs x86_64 1.0.6-13.el7 base 40 k
ca-certificates noarch 2020.2.41-70.0.el7_8 base 382 k
centos-logos noarch 70.0.6-3.el7.centos base 21 M
centos-release x86_64 7-9.2009.1.el7.centos updates 27 k
chkconfig x86_64 1.7.6-1.el7 base 182 k
cpio x86_64 2.11-28.el7 base 211 k
cracklib x86_64 2.9.0-11.el7 base 80 k
cracklib-dicts x86_64 2.9.0-11.el7 base 3.6 M
cronie-anacron x86_64 1.4.11-23.el7 base 36 k
crontabs noarch 1.11-6.20121102git.el7 base 13 k
cryptsetup-libs x86_64 2.0.3-6.el7 base 339 k
cyrus-sasl-lib x86_64 2.1.26-23.el7 base 155 k
dbus x86_64 1:1.10.24-15.el7 base 245 k
dbus-glib x86_64 0.100-7.el7 base 102 k
dbus-libs x86_64 1:1.10.24-15.el7 base 169 k
dbus-python x86_64 1.1.1-9.el7 base 206 k
device-mapper x86_64 7:1.02.170-6.el7_9.5 updates 297 k
device-mapper-libs x86_64 7:1.02.170-6.el7_9.5 updates 325 k
dhcp-common x86_64 12:4.2.5-82.el7.centos base 176 k
dhcp-libs x86_64 12:4.2.5-82.el7.centos base 133 k
diffutils x86_64 3.3-5.el7 base 322 k
dmidecode x86_64 1:3.2-5.el7_9.1 updates 82 k
dracut x86_64 033-572.el7 base 329 k
dracut-network x86_64 033-572.el7 base 103 k
e2fsprogs-libs x86_64 1.42.9-19.el7 base 168 k
ebtables x86_64 2.0.10-16.el7 base 123 k
elfutils-default-yama-scope noarch 0.176-5.el7 base 33 k
elfutils-libelf x86_64 0.176-5.el7 base 195 k
elfutils-libs x86_64 0.176-5.el7 base 291 k
ethtool x86_64 2:4.8-10.el7 base 127 k
expat x86_64 2.1.0-12.el7 base 81 k
file-libs x86_64 5.11-37.el7 base 340 k
findutils x86_64 1:4.5.11-6.el7 base 559 k
fipscheck x86_64 1.4.1-6.el7 base 21 k
fipscheck-lib x86_64 1.4.1-6.el7 base 11 k
firewalld-filesystem noarch 0.6.3-13.el7_9 updates 51 k
gawk x86_64 4.0.2-4.el7_3.1 base 874 k
gdbm x86_64 1.10-8.el7 base 70 k
glib2 x86_64 2.56.1-8.el7 updates 2.5 M
glibc-common x86_64 2.17-324.el7_9 updates 12 M
gmp x86_64 1:6.0.0-15.el7 base 281 k
gnupg2 x86_64 2.0.22-5.el7_5 base 1.5 M
gobject-introspection x86_64 1.56.1-1.el7 base 241 k
gpgme x86_64 1.3.2-5.el7 base 146 k
grep x86_64 2.20-3.el7 base 344 k
groff-base x86_64 1.22.2-8.el7 base 942 k
gzip x86_64 1.5-10.el7 base 130 k
hardlink x86_64 1:1.0-19.el7 base 14 k
hwdata x86_64 0.252-9.7.el7 base 2.5 M
info x86_64 5.1-5.el7 base 233 k
ipset x86_64 7.1-1.el7 base 39 k
ipset-libs x86_64 7.1-1.el7 base 64 k
json-c x86_64 0.11-4.el7_0 base 31 k
kbd-legacy noarch 1.15.5-15.el7 base 466 k
kbd-misc noarch 1.15.5-15.el7 base 1.4 M
keyutils-libs x86_64 1.5.8-3.el7 base 25 k
kmod x86_64 20-28.el7 base 123 k
kmod-libs x86_64 20-28.el7 base 51 k
kpartx x86_64 0.4.9-134.el7_9 updates 81 k
krb5-libs x86_64 1.15.1-50.el7 base 809 k
libacl x86_64 2.2.51-15.el7 base 27 k
libassuan x86_64 2.1.0-3.el7 base 63 k
libattr x86_64 2.4.46-13.el7 base 18 k
libblkid x86_64 2.23.2-65.el7_9.1 updates 183 k
libcap x86_64 2.22-11.el7 base 47 k
libcap-ng x86_64 0.7.5-4.el7 base 25 k
libcom_err x86_64 1.42.9-19.el7 base 42 k
libcurl x86_64 7.29.0-59.el7_9.1 updates 223 k
libdb x86_64 5.3.21-25.el7 base 720 k
libdb-utils x86_64 5.3.21-25.el7 base 132 k
libdrm x86_64 2.4.97-2.el7 base 151 k
libedit x86_64 3.0-12.20121213cvs.el7 base 92 k
libestr x86_64 0.1.9-2.el7 base 20 k
libfastjson x86_64 0.99.4-3.el7 base 27 k
libffi x86_64 3.0.13-19.el7 base 30 k
libgcc x86_64 4.8.5-44.el7 base 103 k
libgcrypt x86_64 1.5.3-14.el7 base 263 k
libgpg-error x86_64 1.12-3.el7 base 87 k
libidn x86_64 1.28-4.el7 base 209 k
libmnl x86_64 1.0.3-7.el7 base 23 k
libmount x86_64 2.23.2-65.el7_9.1 updates 185 k
libnetfilter_conntrack x86_64 1.0.6-1.el7_3 base 55 k
libnfnetlink x86_64 1.0.1-4.el7 base 26 k
libpciaccess x86_64 0.14-1.el7 base 26 k
libpipeline x86_64 1.2.3-3.el7 base 53 k
libpwquality x86_64 1.2.3-5.el7 base 85 k
libselinux x86_64 2.5-15.el7 base 162 k
libselinux-python x86_64 2.5-15.el7 base 236 k
libselinux-utils x86_64 2.5-15.el7 base 151 k
libsemanage x86_64 2.5-14.el7 base 151 k
libsepol x86_64 2.5-10.el7 base 297 k
libsmartcols x86_64 2.23.2-65.el7_9.1 updates 143 k
libss x86_64 1.42.9-19.el7 base 47 k
libssh2 x86_64 1.8.0-4.el7 base 88 k
libstdc++ x86_64 4.8.5-44.el7 base 306 k
libtasn1 x86_64 4.10-1.el7 base 320 k
libuser x86_64 0.60-9.el7 base 400 k
libutempter x86_64 1.1.6-4.el7 base 25 k
libuuid x86_64 2.23.2-65.el7_9.1 updates 84 k
libverto x86_64 0.2.5-4.el7 base 16 k
libxml2 x86_64 2.9.1-6.el7.5 base 668 k
logrotate x86_64 3.8.6-19.el7 base 70 k
lsscsi x86_64 0.27-6.el7 base 47 k
lua x86_64 5.1.4-15.el7 base 201 k
lz4 x86_64 1.8.3-1.el7 base 85 k
lzo x86_64 2.06-8.el7 base 59 k
mozjs17 x86_64 17.0.0-20.el7 base 1.4 M
ncurses-base noarch 5.9-14.20130511.el7_4 base 68 k
ncurses-libs x86_64 5.9-14.20130511.el7_4 base 316 k
nspr x86_64 4.25.0-2.el7_9 updates 127 k
nss x86_64 3.53.1-7.el7_9 updates 869 k
nss-pem x86_64 1.0.3-7.el7 base 74 k
nss-softokn x86_64 3.53.1-6.el7_9 updates 354 k
nss-softokn-freebl x86_64 3.53.1-6.el7_9 updates 322 k
nss-sysinit x86_64 3.53.1-7.el7_9 updates 66 k
nss-tools x86_64 3.53.1-7.el7_9 updates 535 k
nss-util x86_64 3.53.1-1.el7_9 updates 79 k
numactl-libs x86_64 2.0.12-5.el7 base 30 k
openldap x86_64 2.4.44-23.el7_9 updates 356 k
openssh x86_64 7.4p1-21.el7 base 510 k
openssl-libs x86_64 1:1.0.2k-21.el7_9 updates 1.2 M
p11-kit x86_64 0.23.5-3.el7 base 252 k
p11-kit-trust x86_64 0.23.5-3.el7 base 129 k
pam x86_64 1.1.8-23.el7 base 721 k
pcre x86_64 8.32-17.el7 base 422 k
pinentry x86_64 0.8.1-17.el7 base 73 k
pkgconfig x86_64 1:0.27.1-4.el7 base 54 k
plymouth-core-libs x86_64 0.8.9-0.34.20140113.el7.centos base 108 k
plymouth-scripts x86_64 0.8.9-0.34.20140113.el7.centos base 39 k
polkit x86_64 0.112-26.el7 base 170 k
polkit-pkla-compat x86_64 0.1-4.el7 base 39 k
popt x86_64 1.13-16.el7 base 42 k
pth x86_64 2.0.7-23.el7 base 89 k
pygpgme x86_64 0.3-9.el7 base 63 k
pyliblzma x86_64 0.5.3-11.el7 base 47 k
python x86_64 2.7.5-90.el7 updates 96 k
python-configobj noarch 4.7.2-7.el7 base 117 k
python-decorator noarch 3.4.0-3.el7 base 27 k
python-firewall noarch 0.6.3-13.el7_9 updates 355 k
python-gobject-base x86_64 3.22.0-1.el7_4.1 base 294 k
python-iniparse noarch 0.4-9.el7 base 39 k
python-libs x86_64 2.7.5-90.el7 updates 5.6 M
python-linux-procfs noarch 0.4.11-4.el7 base 33 k
python-perf x86_64 3.10.0-1160.25.1.el7 updates 8.1 M
python-pycurl x86_64 7.19.0-19.el7 base 80 k
python-pyudev noarch 0.15-9.el7 base 55 k
python-schedutils x86_64 0.4-6.el7 base 21 k
python-slip noarch 0.4.0-4.el7 base 31 k
python-slip-dbus noarch 0.4.0-4.el7 base 32 k
python-urlgrabber noarch 3.10-10.el7 base 108 k
pyxattr x86_64 0.5.1-5.el7 base 28 k
qrencode-libs x86_64 3.4.1-3.el7 base 50 k
readline x86_64 6.2-11.el7 base 193 k
rpm-build-libs x86_64 4.11.3-45.el7 base 107 k
rpm-libs x86_64 4.11.3-45.el7 base 278 k
rpm-python x86_64 4.11.3-45.el7 base 84 k
sed x86_64 4.2.2-7.el7 base 231 k
selinux-policy noarch 3.13.1-268.el7_9.2 updates 498 k
shared-mime-info x86_64 1.8-5.el7 base 312 k
snappy x86_64 1.1.0-3.el7 base 40 k
sqlite x86_64 3.7.17-8.el7_7.1 base 394 k
systemd-libs x86_64 219-78.el7_9.3 updates 418 k
systemd-sysv x86_64 219-78.el7_9.3 updates 97 k
sysvinit-tools x86_64 2.88-14.dsf.el7 base 63 k
tcp_wrappers-libs x86_64 7.6-77.el7 base 66 k
tzdata noarch 2021a-1.el7 updates 501 k
ustr x86_64 1.0.4-16.el7 base 92 k
virt-what x86_64 1.18-4.el7 base 29 k
which x86_64 2.20-7.el7 base 41 k
xz x86_64 5.2.2-1.el7 base 229 k
xz-libs x86_64 5.2.2-1.el7 base 103 k
yum-metadata-parser x86_64 1.1.4-10.el7 base 28 k
yum-plugin-fastestmirror noarch 1.1.31-54.el7_8 base 34 k
zlib x86_64 1.2.7-19.el7_9 updates 90 k
Transaction Summary
=================================================================================================================================================
Install 45 Packages (+179 Dependent packages)
Total download size: 136 M
Installed size: 559 M
Downloading packages:
| 8.1 MB 00:00:06
-------------------------------------------------------------------------------------------------------------------------------------------------
Total 6.3 MB/s | 136 MB 00:00:21
Running transaction check
Running transaction test
Transaction test succeeded
Running transaction
Complete!
+ [[ -n '' ]]
+ yum -c /etc/yum.conf --installroot=/tmp/mkimage-yum.sh.qq2lHm -y clean all
Cleaning repos: base extras updates
Other repos take up 40 M of disk space (use --verbose for details)
+ cat
+ rm -rf /tmp/mkimage-yum.sh.u7pzDD/usr/lib/locale /tmp/mkimage-yum.sh.qq2lHm/usr/share/locale /tmp/mkimage-yum.sh.u7pzDD/usr/lib/gconv /tmp/mkimage-yum.sh.u7pzDD/usr/lib64/gconv /tmp/mkimage-yum.sh.u7pzDD/usr/bin/localedef /tmp/mkimage-yum.sh.u7pzDD/usr/sbin/build-locale-archive
+ rm -rf /tmp/mkimage-yum.sh.u7pzDD/usr/share/man /tmp/mkimage-yum.sh.qq2lHm/usr/share/doc /tmp/mkimage-yum.sh.u7pzDD/usr/share/info /tmp/mkimage-yum.sh.u7pzDD/usr/share/gnome/help
+ rm -rf /tmp/mkimage-yum.sh.u7pzDD/usr/share/cracklib
+ rm -rf /tmp/mkimage-yum.sh.u7pzDD/usr/share/i18n
+ rm -rf /tmp/mkimage-yum.sh.u7pzDD/var/cache/yum
+ mkdir -p --mode=0755 /tmp/mkimage-yum.sh.qq2lHm/var/cache/yum
+ rm -rf /tmp/mkimage-yum.sh.qq2lHm/sbin/sln
+ rm -rf /tmp/mkimage-yum.sh.qq2lHm/etc/ld.so.cache /tmp/mkimage-yum.sh.qq2lHm/var/cache/ldconfig
+ mkdir -p --mode=0755 /tmp/mkimage-yum.sh.qq2lHm/var/cache/ldconfig
+ '[' -z '' ']'
+ for file in '"$target"/etc/{redhat,system}-release'
+ '[' -r /tmp/mkimage-yum.sh.qq2lHm/etc/redhat-release ']'
++ sed 's/^[^0-9\]*\([0-9.]\+\).*$/\1/' /tmp/mkimage-yum.sh.qq2lHm/etc/redhat-release
+ version=7.9.2009
+ break
+ '[' -z 7.9.2009 ']'
+ tar --numeric-owner -c -C /tmp/mkimage-yum.sh.qq2lHm .
+ docker import - centos7:7.9.2009
sha256:b7ab681100c3f13c0810f5fdf591a9391ac42d4e0add83522bb659741f7e84b1
+ docker run -i -t --rm centos7:7.9.2009 /bin/bash -c 'echo success'
success
+ rm -rf /tmp/mkimage-yum.sh.qq2lHm
invalid reference format: repository name must be lowercase
[root@master image]# docker image ls |grep centos
centos7 7.9.2009 b7ab681100c3 2 minutes ago 283MB
[root@master image]#
[END] 2021-05-06 23:26:28
http://nl.alpinelinux.org/alpine/edge/main/
https://github.com/Docker-Hub-frolvlad/docker-alpine-glibc
mkimage-alpine.sh
#!/bin/sh
set -e
[ $(id -u) -eq 0 ] || {
printf >&2 '%s requires root\n' "$0"
exit 1
}
usage() {
printf >&2 '%s: [-r release] [-m mirror] [-s] [-c additional repository] [-a arch]\n' "$0"
exit 1
}
tmp() {
TMP=$(mktemp -d ${TMPDIR:-/var/tmp}/alpine-docker-XXXXXXXXXX)
ROOTFS=$(mktemp -d ${TMPDIR:-/var/tmp}/alpine-docker-rootfs-XXXXXXXXXX)
trap "rm -rf $TMP $ROOTFS" EXIT TERM INT
}
apkv() {
curl -sSL $MAINREPO/$ARCH/APKINDEX.tar.gz | tar -Oxz \
| grep --text '^P:apk-tools-static$' -A1 | tail -n1 | cut -d: -f2
}
getapk() {
curl -sSL $MAINREPO/$ARCH/apk-tools-static-$(apkv).apk \
| tar -xz -C $TMP sbin/apk.static
}
mkbase() {
$TMP/sbin/apk.static --repository $MAINREPO --no-cache --allow-untrusted \
--root $ROOTFS --initdb add alpine-base
}
conf() {
printf '%s\n' $MAINREPO > $ROOTFS/etc/apk/repositories
printf '%s\n' $ADDITIONALREPO >> $ROOTFS/etc/apk/repositories
}
pack() {
local id
id=$(tar --numeric-owner -C $ROOTFS -c . | docker import - alpine:$REL)
docker tag $id alpine:latest
docker run --rm alpine printf 'alpine:%s with id=%s created!\n' $REL $id
}
save() {
[ $SAVE -eq 1 ] || return 0
tar --numeric-owner -C $ROOTFS -c . | xz > rootfs.tar.xz
}
while getopts "hr:m:sc:a:" opt; do
case $opt in
r)
REL=$OPTARG
;;
m)
MIRROR=$OPTARG
;;
s)
SAVE=1
;;
c)
ADDITIONALREPO=$OPTARG
;;
a)
ARCH=$OPTARG
;;
*)
usage
;;
esac
done
REL=${REL:-edge}
MIRROR=${MIRROR:-http://nl.alpinelinux.org/alpine}
SAVE=${SAVE:-0}
MAINREPO=$MIRROR/$REL/main
ADDITIONALREPO=$MIRROR/$REL/${ADDITIONALREPO:-community}
ARCH=${ARCH:-$(uname -m)}
tmp
getapk
mkbase
conf
pack
save
[root@master image]# ./mkimage-alpine.sh alpine
tar: Ignoring unknown extended header keyword `APK-TOOLS.checksum.SHA1'
tar: Ignoring unknown extended header keyword `APK-TOOLS.checksum.SHA1'
fetch http://nl.alpinelinux.org/alpine/edge/main/x86_64/APKINDEX.tar.gz
(1/20) Installing musl (1.2.2-r2)
(2/20) Installing busybox (1.33.1-r1)
Executing busybox-1.33.1-r1.post-install
(3/20) Installing alpine-baselayout (3.2.0-r12)
Executing alpine-baselayout-3.2.0-r12.pre-install
Executing alpine-baselayout-3.2.0-r12.post-install
(4/20) Installing ifupdown-ng (0.11.2-r0)
(5/20) Installing openrc (0.43.3-r0)
Executing openrc-0.43.3-r0.post-install
(6/20) Installing alpine-conf (3.11.0-r2)
(7/20) Installing libcrypto1.1 (1.1.1k-r0)
(8/20) Installing libssl1.1 (1.1.1k-r0)
(9/20) Installing ca-certificates-bundle (20191127-r5)
(10/20) Installing libretls (3.3.2-r0)
(11/20) Installing ssl_client (1.33.1-r1)
(12/20) Installing zlib (1.2.11-r3)
(13/20) Installing apk-tools (2.12.5-r0)
(14/20) Installing busybox-suid (1.33.1-r1)
(15/20) Installing busybox-initscripts (3.2-r2)
Executing busybox-initscripts-3.2-r2.post-install
(16/20) Installing scanelf (1.2.9-r0)
(17/20) Installing musl-utils (1.2.2-r2)
(18/20) Installing libc-utils (0.7.2-r3)
(19/20) Installing alpine-keys (2.2-r0)
(20/20) Installing alpine-base (3.14.0_alpha20210212-r0)
Executing busybox-1.33.1-r1.trigger
OK: 9 MiB in 20 packages
alpine:edge with id=sha256:e80c06b9ef5ff10062ffb8cc0dfcc653cd2c3a0cc221e44f1d0b206a39522b12 created!
[root@master image]#
[root@master image]# docker image ls |grep alpine
alpine edge e80c06b9ef5f 49 seconds ago 7.85MB
alpine latest e80c06b9ef5f 49 seconds ago 7.85MB
[root@master image]#
Alpine:
- curl
- net-tools:ifconfig、netstat、route 等命令
- iproute2:ip link、ip route、ss 等命令
- iptables
- iputils
- tcpdump
- busybox-extras:包含 telnet 命令
- iperf3:
- ethtool:用于获取以太网卡的配置信息,或者修改这些配置
- nftables:是一个 netfilter 项目,旨在替换现有的 {ip,ip6,arp,eb}tables 框架,为{ip,ip6}tables提供一个新的包过滤框架、一个新的用户空间实用程序(nft)和一个兼容层。它使用现有的钩子、链接跟踪系统、用户空间排队组件和 netfilter 日志子系统。
- keepalived:是基于 vrrp 协议的一款高可用软件。Keepailived 有一台主服务器和多台备份服务器,在主服务器和备份服务器上面部署相同的服务配置,使用一个虚拟IP地址对外提供服务,当主服务器出现故障时,虚拟IP地址会自动漂移到备份服务器
CentOS:
alpin
FROM alpine:3.11
RUN apk add --no-cache \
bash \
coreutils \
curl \
iproute2 \
iptables \
iputils \
net-tools \
tcpdump \
busybox-extras \
tzdata \
&& rm -f /etc/localtime \
&& ln -sv /usr/share/zoneinfo/Asia/Shanghai /etc/localtime \
&& echo "Asia/Shanghai" > /etc/timezone \
&& [ ! -e /etc/nsswitch.conf ] \
&& echo "hosts: files dns" > /etc/nsswitch.conf
Centos
FROM centos:7
RUN yum install -y \
telnet \
traceroute \
iproute \
iptables \
net-tools \
tcpdump \
tzdata \
&& rm -f /etc/localtime \
&& ln -sv /usr/share/zoneinfo/Asia/Shanghai /etc/localtime \
&& echo "Asia/Shanghai" > /etc/timezone \
&& yum clean all
清理untagged镜像
docker rmi $(docker images --filter dangling=true -q)
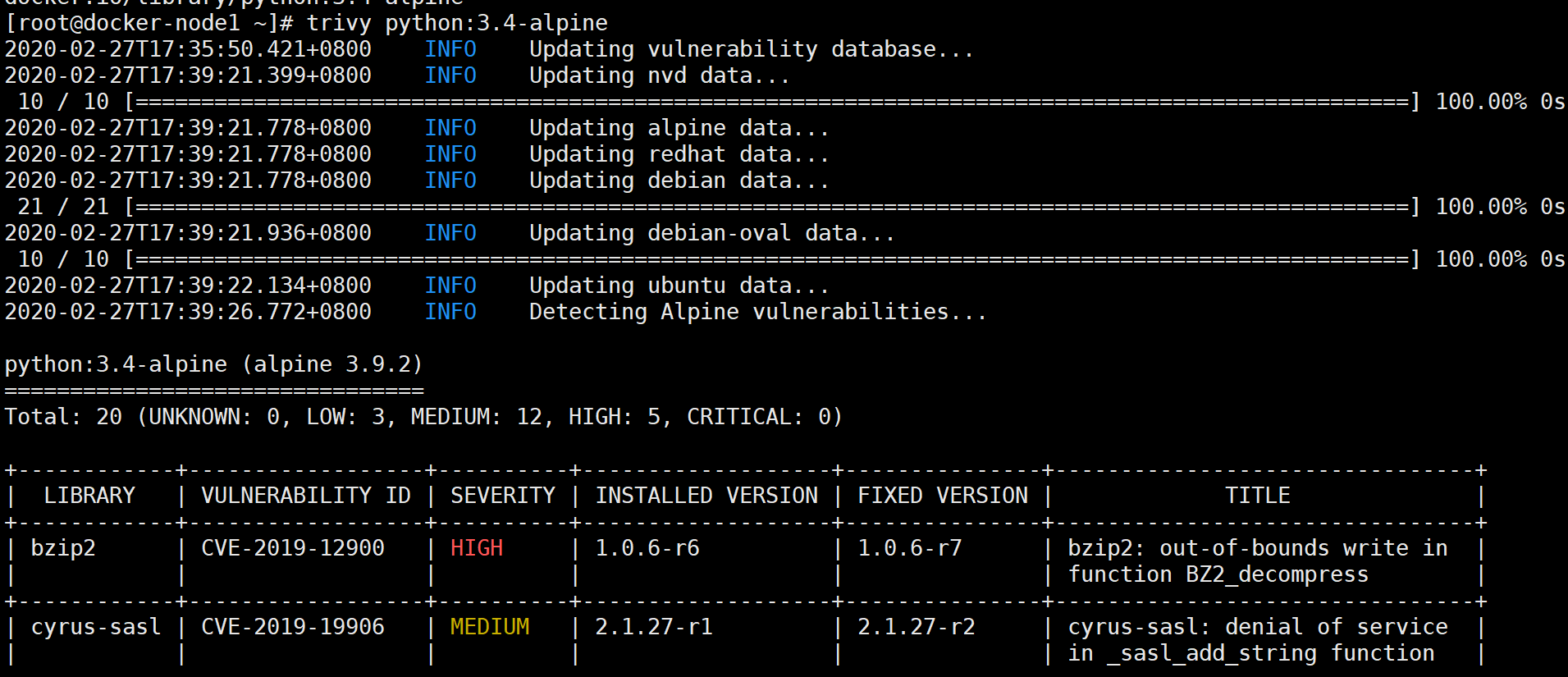
镜像安全
vim /etc/yum.repos.d/trivy.repo
[trivy]
name=Trivy repository
baseurl=https://knqyf263.github.io/trivy-repo/rpm/releases/$releasever/$basearch/
gpgcheck=0
enabled=1
yum -y install trivy
rpm -ivh https://github.com/aquasecurity/trivy/releases/download/v0.1.6/trivy_0.1.6_Linux-64bit.rpm
https://www.freebuf.com/sectool/207757.html
[root@rancher-server ~]#
[root@rancher-server ~]# docker run -it --net host --pid host --userns host --cap-add audit_control \
> -e DOCKER_CONTENT_TRUST=$DOCKER_CONTENT_TRUST \
> -v /etc:/etc:ro \
> -v /usr/bin/docker-containerd:/usr/bin/docker-containerd:ro \
> -v /usr/bin/docker-runc:/usr/bin/docker-runc:ro \
> -v /usr/lib/systemd:/usr/lib/systemd:ro \
> -v /var/lib:/var/lib:ro \
> -v /var/run/docker.sock:/var/run/docker.sock:ro \
> --label docker_bench_security \
> docker/docker-bench-security
Unable to find image 'docker/docker-bench-security:latest' locally
latest: Pulling from docker/docker-bench-security
cd784148e348: Pull complete
48fe0d48816d: Pull complete
164e5e0f48c5: Pull complete
378ed37ea5ff: Pull complete
Digest: sha256:ddbdf4f86af4405da4a8a7b7cc62bb63bfeb75e85bf22d2ece70c204d7cfabb8
Status: Downloaded newer image for docker/docker-bench-security:latest
# ------------------------------------------------------------------------------
# Docker Bench for Security v1.3.4
#
# Docker, Inc. (c) 2015-
#
# Checks for dozens of common best-practices around deploying Docker containers in production.
# Inspired by the CIS Docker Community Edition Benchmark v1.1.0.
# ------------------------------------------------------------------------------
Initializing Mon Apr 12 09:34:11 UTC 2021
[INFO] 1 - Host Configuration
[WARN] 1.1 - Ensure a separate partition for containers has been created
[NOTE] 1.2 - Ensure the container host has been Hardened
[INFO] 1.3 - Ensure Docker is up to date
[INFO] * Using 20.10.5, verify is it up to date as deemed necessary
[INFO] * Your operating system vendor may provide support and security maintenance for Docker
[INFO] 1.4 - Ensure only trusted users are allowed to control Docker daemon
[INFO] * docker:x:993
[WARN] 1.5 - Ensure auditing is configured for the Docker daemon
[WARN] 1.6 - Ensure auditing is configured for Docker files and directories - /var/lib/docker
[WARN] 1.7 - Ensure auditing is configured for Docker files and directories - /etc/docker
[WARN] 1.8 - Ensure auditing is configured for Docker files and directories - docker.service
[WARN] 1.9 - Ensure auditing is configured for Docker files and directories - docker.socket
[INFO] 1.10 - Ensure auditing is configured for Docker files and directories - /etc/default/docker
[INFO] * File not found
[INFO] 1.11 - Ensure auditing is configured for Docker files and directories - /etc/docker/daemon.json
[INFO] * File not found
[INFO] 1.12 - Ensure auditing is configured for Docker files and directories - /usr/bin/docker-containerd
[INFO] * File not found
[INFO] 1.13 - Ensure auditing is configured for Docker files and directories - /usr/bin/docker-runc
[INFO] * File not found
[INFO] 2 - Docker daemon configuration
[WARN] 2.1 - Ensure network traffic is restricted between containers on the default bridge
[PASS] 2.2 - Ensure the logging level is set to 'info'
[PASS] 2.3 - Ensure Docker is allowed to make changes to iptables
[PASS] 2.4 - Ensure insecure registries are not used
[PASS] 2.5 - Ensure aufs storage driver is not used
[INFO] 2.6 - Ensure TLS authentication for Docker daemon is configured
[INFO] * Docker daemon not listening on TCP
[INFO] 2.7 - Ensure the default ulimit is configured appropriately
[INFO] * Default ulimit doesn't appear to be set
[WARN] 2.8 - Enable user namespace support
[PASS] 2.9 - Ensure the default cgroup usage has been confirmed
[PASS] 2.10 - Ensure base device size is not changed until needed
[WARN] 2.11 - Ensure that authorization for Docker client commands is enabled
[WARN] 2.12 - Ensure centralized and remote logging is configured
[INFO] 2.13 - Ensure operations on legacy registry (v1) are Disabled (Deprecated)
[WARN] 2.14 - Ensure live restore is Enabled
[WARN] 2.15 - Ensure Userland Proxy is Disabled
[PASS] 2.16 - Ensure daemon-wide custom seccomp profile is applied, if needed
[PASS] 2.17 - Ensure experimental features are avoided in production
[WARN] 2.18 - Ensure containers are restricted from acquiring new privileges
[INFO] 3 - Docker daemon configuration files
[PASS] 3.1 - Ensure that docker.service file ownership is set to root:root
[PASS] 3.2 - Ensure that docker.service file permissions are set to 644 or more restrictive
[PASS] 3.3 - Ensure that docker.socket file ownership is set to root:root
[PASS] 3.4 - Ensure that docker.socket file permissions are set to 644 or more restrictive
[PASS] 3.5 - Ensure that /etc/docker directory ownership is set to root:root
[PASS] 3.6 - Ensure that /etc/docker directory permissions are set to 755 or more restrictive
[INFO] 3.7 - Ensure that registry certificate file ownership is set to root:root
[INFO] * Directory not found
[INFO] 3.8 - Ensure that registry certificate file permissions are set to 444 or more restrictive
[INFO] * Directory not found
[INFO] 3.9 - Ensure that TLS CA certificate file ownership is set to root:root
[INFO] * No TLS CA certificate found
[INFO] 3.10 - Ensure that TLS CA certificate file permissions are set to 444 or more restrictive
[INFO] * No TLS CA certificate found
[INFO] 3.11 - Ensure that Docker server certificate file ownership is set to root:root
[INFO] * No TLS Server certificate found
[INFO] 3.12 - Ensure that Docker server certificate file permissions are set to 444 or more restrictive
[INFO] * No TLS Server certificate found
[INFO] 3.13 - Ensure that Docker server certificate key file ownership is set to root:root
[INFO] * No TLS Key found
[INFO] 3.14 - Ensure that Docker server certificate key file permissions are set to 400
[INFO] * No TLS Key found
[PASS] 3.15 - Ensure that Docker socket file ownership is set to root:docker
[PASS] 3.16 - Ensure that Docker socket file permissions are set to 660 or more restrictive
[INFO] 3.17 - Ensure that daemon.json file ownership is set to root:root
[INFO] * File not found
[INFO] 3.18 - Ensure that daemon.json file permissions are set to 644 or more restrictive
[INFO] * File not found
[INFO] 3.19 - Ensure that /etc/default/docker file ownership is set to root:root
[INFO] * File not found
[INFO] 3.20 - Ensure that /etc/default/docker file permissions are set to 644 or more restrictive
[INFO] * File not found
[INFO] 4 - Container Images and Build File
[WARN] 4.1 - Ensure a user for the container has been created
[WARN] * Running as root: cnrancher
[WARN] * Running as root: vim
[WARN] * Running as root: harbor-log
[NOTE] 4.2 - Ensure that containers use trusted base images
[NOTE] 4.3 - Ensure unnecessary packages are not installed in the container
[NOTE] 4.4 - Ensure images are scanned and rebuilt to include security patches
[WARN] 4.5 - Ensure Content trust for Docker is Enabled
[WARN] 4.6 - Ensure HEALTHCHECK instructions have been added to the container image
[WARN] * No Healthcheck found: [cnrancher/rancher:v2.5.7-ent-rc3-linux-amd64]
[WARN] * No Healthcheck found: [busybox:latest]
[WARN] * No Healthcheck found: [sonatype/nexus3:latest]
[WARN] * No Healthcheck found: [goharbor/prepare:v2.2.0]
[WARN] * No Healthcheck found: [cnrancher/rancher:v2.4.13-ent2]
[WARN] * No Healthcheck found: [arush/gateone:http]
[WARN] * No Healthcheck found: [taobeier/vim:latest]
[WARN] * No Healthcheck found: [arush/cka_lab:latest]
[INFO] 4.7 - Ensure update instructions are not use alone in the Dockerfile
[INFO] * Update instruction found: [cnrancher/rancher:v2.5.7-ent-rc3-linux-amd64]
[INFO] * Update instruction found: [cnrancher/rancher:v2.4.13-ent2]
[INFO] * Update instruction found: [arush/gateone:http]
[INFO] * Update instruction found: [taobeier/vim:latest]
[NOTE] 4.8 - Ensure setuid and setgid permissions are removed in the images
[INFO] 4.9 - Ensure COPY is used instead of ADD in Dockerfile
[INFO] * ADD in image history: [cnrancher/rancher:v2.5.7-ent-rc3-linux-amd64]
[INFO] * ADD in image history: [busybox:latest]
[INFO] * ADD in image history: [sonatype/nexus3:latest]
[INFO] * ADD in image history: [goharbor/chartmuseum-photon:v2.2.0]
[INFO] * ADD in image history: [goharbor/redis-photon:v2.2.0]
[INFO] * ADD in image history: [goharbor/trivy-adapter-photon:v2.2.0]
[INFO] * ADD in image history: [goharbor/harbor-registryctl:v2.2.0]
[INFO] * ADD in image history: [goharbor/registry-photon:v2.2.0]
[INFO] * ADD in image history: [goharbor/nginx-photon:v2.2.0]
[INFO] * ADD in image history: [goharbor/harbor-log:v2.2.0]
[INFO] * ADD in image history: [goharbor/harbor-jobservice:v2.2.0]
[INFO] * ADD in image history: [goharbor/harbor-core:v2.2.0]
[INFO] * ADD in image history: [goharbor/harbor-portal:v2.2.0]
[INFO] * ADD in image history: [goharbor/harbor-db:v2.2.0]
[INFO] * ADD in image history: [goharbor/prepare:v2.2.0]
[INFO] * ADD in image history: [cnrancher/rancher:v2.4.13-ent2]
[INFO] * ADD in image history: [arush/gateone:http]
[INFO] * ADD in image history: [docker/docker-bench-security:latest]
[INFO] * ADD in image history: [taobeier/vim:latest]
[INFO] * ADD in image history: [arush/cka_lab:latest]
[NOTE] 4.10 - Ensure secrets are not stored in Dockerfiles
[NOTE] 4.11 - Ensure verified packages are only Installed
[INFO] 5 - Container Runtime
[WARN] 5.1 - Ensure AppArmor Profile is Enabled
[WARN] * No AppArmorProfile Found: cnrancher
[WARN] * No AppArmorProfile Found: vim
[WARN] * No AppArmorProfile Found: nginx
[WARN] * No AppArmorProfile Found: harbor-jobservice
[WARN] * No AppArmorProfile Found: trivy-adapter
[WARN] * No AppArmorProfile Found: harbor-core
[WARN] * No AppArmorProfile Found: registryctl
[WARN] * No AppArmorProfile Found: harbor-db
[WARN] * No AppArmorProfile Found: redis
[WARN] * No AppArmorProfile Found: registry
[WARN] * No AppArmorProfile Found: chartmuseum
[WARN] * No AppArmorProfile Found: harbor-portal
[WARN] * No AppArmorProfile Found: harbor-log
[WARN] 5.2 - Ensure SELinux security options are set, if applicable
[WARN] * No SecurityOptions Found: vim
[WARN] * No SecurityOptions Found: nginx
[WARN] * No SecurityOptions Found: harbor-jobservice
[WARN] * No SecurityOptions Found: trivy-adapter
[WARN] * No SecurityOptions Found: harbor-core
[WARN] * No SecurityOptions Found: registryctl
[WARN] * No SecurityOptions Found: harbor-db
[WARN] * No SecurityOptions Found: redis
[WARN] * No SecurityOptions Found: registry
[WARN] * No SecurityOptions Found: chartmuseum
[WARN] * No SecurityOptions Found: harbor-portal
[WARN] * No SecurityOptions Found: harbor-log
[PASS] 5.3 - Ensure Linux Kernel Capabilities are restricted within containers
[WARN] 5.4 - Ensure privileged containers are not used
[WARN] * Container running in Privileged mode: cnrancher
[PASS] 5.5 - Ensure sensitive host system directories are not mounted on containers
[PASS] 5.6 - Ensure ssh is not run within containers
[WARN] 5.7 - Ensure privileged ports are not mapped within containers
[WARN] * Privileged Port in use: 443 in cnrancher
[WARN] * Privileged Port in use: 80 in cnrancher
[NOTE] 5.8 - Ensure only needed ports are open on the container
[PASS] 5.9 - Ensure the host's network namespace is not shared
[WARN] 5.10 - Ensure memory usage for container is limited
[WARN] * Container running without memory restrictions: cnrancher
[WARN] * Container running without memory restrictions: vim
[WARN] * Container running without memory restrictions: nginx
[WARN] * Container running without memory restrictions: harbor-jobservice
[WARN] * Container running without memory restrictions: trivy-adapter
[WARN] * Container running without memory restrictions: harbor-core
[WARN] * Container running without memory restrictions: registryctl
[WARN] * Container running without memory restrictions: harbor-db
[WARN] * Container running without memory restrictions: redis
[WARN] * Container running without memory restrictions: registry
[WARN] * Container running without memory restrictions: chartmuseum
[WARN] * Container running without memory restrictions: harbor-portal
[WARN] * Container running without memory restrictions: harbor-log
[WARN] 5.11 - Ensure CPU priority is set appropriately on the container
[WARN] * Container running without CPU restrictions: cnrancher
[WARN] * Container running without CPU restrictions: vim
[WARN] * Container running without CPU restrictions: nginx
[WARN] * Container running without CPU restrictions: harbor-jobservice
[WARN] * Container running without CPU restrictions: trivy-adapter
[WARN] * Container running without CPU restrictions: harbor-core
[WARN] * Container running without CPU restrictions: registryctl
[WARN] * Container running without CPU restrictions: harbor-db
[WARN] * Container running without CPU restrictions: redis
[WARN] * Container running without CPU restrictions: registry
[WARN] * Container running without CPU restrictions: chartmuseum
[WARN] * Container running without CPU restrictions: harbor-portal
[WARN] * Container running without CPU restrictions: harbor-log
[WARN] 5.12 - Ensure the container's root filesystem is mounted as read only
[WARN] * Container running with root FS mounted R/W: cnrancher
[WARN] * Container running with root FS mounted R/W: vim
[WARN] * Container running with root FS mounted R/W: nginx
[WARN] * Container running with root FS mounted R/W: harbor-jobservice
[WARN] * Container running with root FS mounted R/W: trivy-adapter
[WARN] * Container running with root FS mounted R/W: harbor-core
[WARN] * Container running with root FS mounted R/W: registryctl
[WARN] * Container running with root FS mounted R/W: harbor-db
[WARN] * Container running with root FS mounted R/W: redis
[WARN] * Container running with root FS mounted R/W: registry
[WARN] * Container running with root FS mounted R/W: chartmuseum
[WARN] * Container running with root FS mounted R/W: harbor-portal
[WARN] * Container running with root FS mounted R/W: harbor-log
[WARN] 5.13 - Ensure incoming container traffic is binded to a specific host interface
[WARN] * Port being bound to wildcard IP: 0.0.0.0 in cnrancher
[WARN] * Port being bound to wildcard IP: 0.0.0.0 in cnrancher
[WARN] * Port being bound to wildcard IP: 0.0.0.0 in nginx
[WARN] 5.14 - Ensure 'on-failure' container restart policy is set to '5'
[WARN] * MaximumRetryCount is not set to 5: cnrancher
[WARN] * MaximumRetryCount is not set to 5: vim
[WARN] * MaximumRetryCount is not set to 5: nginx
[WARN] * MaximumRetryCount is not set to 5: harbor-jobservice
[WARN] * MaximumRetryCount is not set to 5: trivy-adapter
[WARN] * MaximumRetryCount is not set to 5: harbor-core
[WARN] * MaximumRetryCount is not set to 5: registryctl
[WARN] * MaximumRetryCount is not set to 5: harbor-db
[WARN] * MaximumRetryCount is not set to 5: redis
[WARN] * MaximumRetryCount is not set to 5: registry
[WARN] * MaximumRetryCount is not set to 5: chartmuseum
[WARN] * MaximumRetryCount is not set to 5: harbor-portal
[WARN] * MaximumRetryCount is not set to 5: harbor-log
[PASS] 5.15 - Ensure the host's process namespace is not shared
[PASS] 5.16 - Ensure the host's IPC namespace is not shared
[PASS] 5.17 - Ensure host devices are not directly exposed to containers
[INFO] 5.18 - Ensure the default ulimit is overwritten at runtime, only if needed
[INFO] * Container no default ulimit override: cnrancher
[INFO] * Container no default ulimit override: vim
[INFO] * Container no default ulimit override: nginx
[INFO] * Container no default ulimit override: harbor-jobservice
[INFO] * Container no default ulimit override: trivy-adapter
[INFO] * Container no default ulimit override: harbor-core
[INFO] * Container no default ulimit override: registryctl
[INFO] * Container no default ulimit override: harbor-db
[INFO] * Container no default ulimit override: redis
[INFO] * Container no default ulimit override: registry
[INFO] * Container no default ulimit override: chartmuseum
[INFO] * Container no default ulimit override: harbor-portal
[INFO] * Container no default ulimit override: harbor-log
[PASS] 5.19 - Ensure mount propagation mode is not set to shared
[PASS] 5.20 - Ensure the host's UTS namespace is not shared
[PASS] 5.21 - Ensure the default seccomp profile is not Disabled
[NOTE] 5.22 - Ensure docker exec commands are not used with privileged option
[NOTE] 5.23 - Ensure docker exec commands are not used with user option
[PASS] 5.24 - Ensure cgroup usage is confirmed
[WARN] 5.25 - Ensure the container is restricted from acquiring additional privileges
[WARN] * Privileges not restricted: cnrancher
[WARN] * Privileges not restricted: vim
[WARN] * Privileges not restricted: nginx
[WARN] * Privileges not restricted: harbor-jobservice
[WARN] * Privileges not restricted: trivy-adapter
[WARN] * Privileges not restricted: harbor-core
[WARN] * Privileges not restricted: registryctl
[WARN] * Privileges not restricted: harbor-db
[WARN] * Privileges not restricted: redis
[WARN] * Privileges not restricted: registry
[WARN] * Privileges not restricted: chartmuseum
[WARN] * Privileges not restricted: harbor-portal
[WARN] * Privileges not restricted: harbor-log
[WARN] 5.26 - Ensure container health is checked at runtime
[WARN] * Health check not set: cnrancher
[WARN] * Health check not set: vim
[INFO] 5.27 - Ensure docker commands always get the latest version of the image
[WARN] 5.28 - Ensure PIDs cgroup limit is used
[WARN] * PIDs limit not set: cnrancher
[WARN] * PIDs limit not set: vim
[WARN] * PIDs limit not set: nginx
[WARN] * PIDs limit not set: harbor-jobservice
[WARN] * PIDs limit not set: trivy-adapter
[WARN] * PIDs limit not set: harbor-core
[WARN] * PIDs limit not set: registryctl
[WARN] * PIDs limit not set: harbor-db
[WARN] * PIDs limit not set: redis
[WARN] * PIDs limit not set: registry
[WARN] * PIDs limit not set: chartmuseum
[WARN] * PIDs limit not set: harbor-portal
[WARN] * PIDs limit not set: harbor-log
[INFO] 5.29 - Ensure Docker's default bridge docker0 is not used
[INFO] * Container in docker0 network: vim
[INFO] * Container in docker0 network: cnrancher
[PASS] 5.30 - Ensure the host's user namespaces is not shared
[PASS] 5.31 - Ensure the Docker socket is not mounted inside any containers
[INFO] 6 - Docker Security Operations
[INFO] 6.1 - Avoid image sprawl
[INFO] * There are currently: 20 images
[INFO] 6.2 - Avoid container sprawl
[INFO] * There are currently a total of 20 containers, with 14 of them currently running
[INFO] 7 - Docker Swarm Configuration
[PASS] 7.1 - Ensure swarm mode is not Enabled, if not needed
[PASS] 7.2 - Ensure the minimum number of manager nodes have been created in a swarm (Swarm mode not enabled)
[PASS] 7.3 - Ensure swarm services are binded to a specific host interface (Swarm mode not enabled)
[PASS] 7.4 - Ensure data exchanged between containers are encrypted on different nodes on the overlay network
[PASS] 7.5 - Ensure Docker's secret management commands are used for managing secrets in a Swarm cluster (Swarm mode not enabled)
[PASS] 7.6 - Ensure swarm manager is run in auto-lock mode (Swarm mode not enabled)
[PASS] 7.7 - Ensure swarm manager auto-lock key is rotated periodically (Swarm mode not enabled)
[PASS] 7.8 - Ensure node certificates are rotated as appropriate (Swarm mode not enabled)
[PASS] 7.9 - Ensure CA certificates are rotated as appropriate (Swarm mode not enabled)
[PASS] 7.10 - Ensure management plane traffic has been separated from data plane traffic (Swarm mode not enabled)
[INFO] Checks: 105
[INFO] Score: 10
[root@rancher-server ~]#
FROM openjdk:8-jre-alpine3.9
RUN apk update && apk upgrade && apk add ca-certificates && update-ca-certificates \
&& apk add --update tzdata && cp /usr/share/zoneinfo/Asia/Shanghai /etc/localtime \
&& echo "Asia/Shanghai" > /etc/timezone \
&& rm -rf /var/cache/apk/*
ENV TZ=Asia/Shanghai
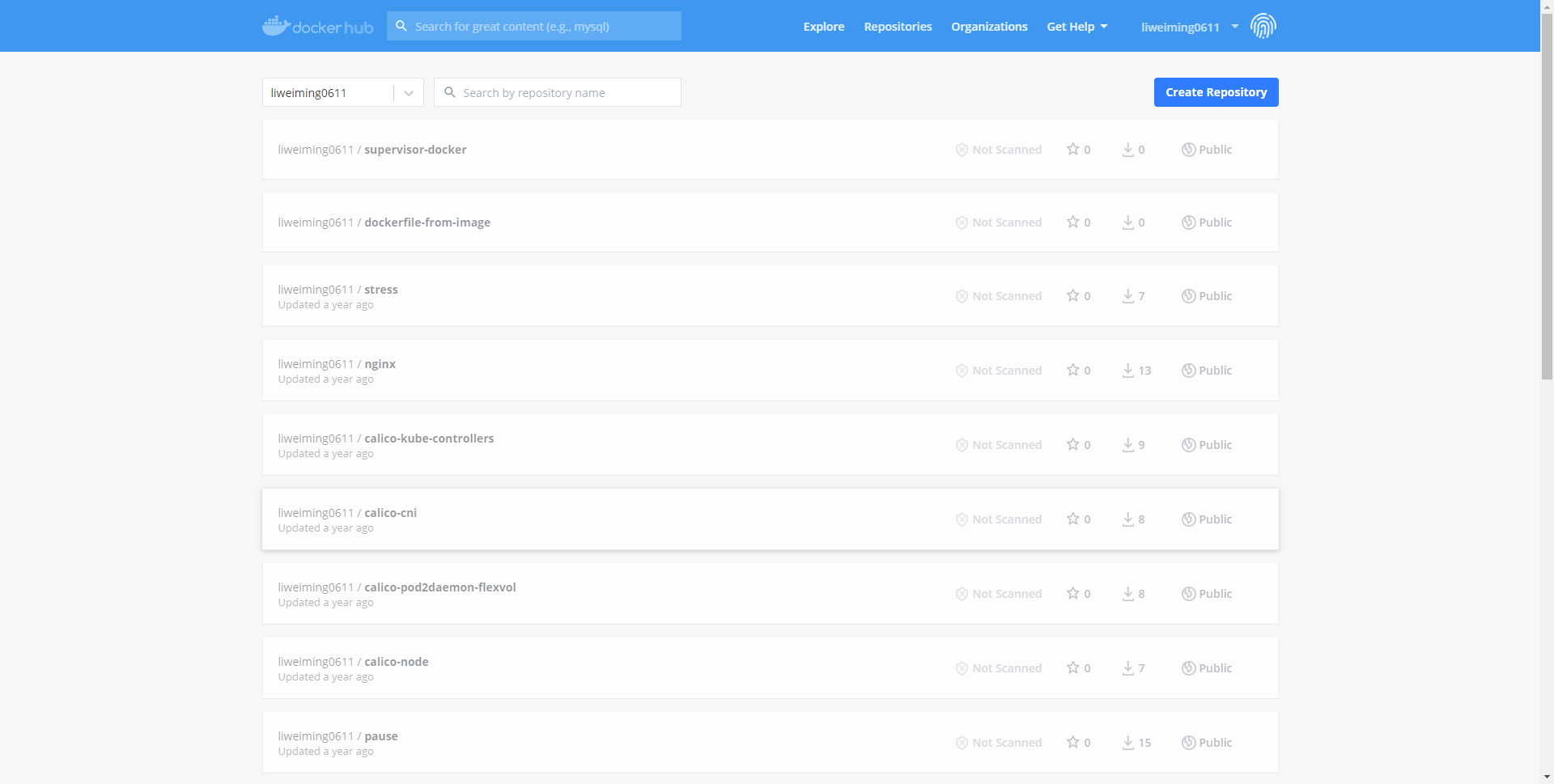
镜像仓库
Docker hub
引用
https://blog.51cto.com/dengaosky/2427258
官方私有仓库:Docker Registry
https://docs.docker.com/registry/
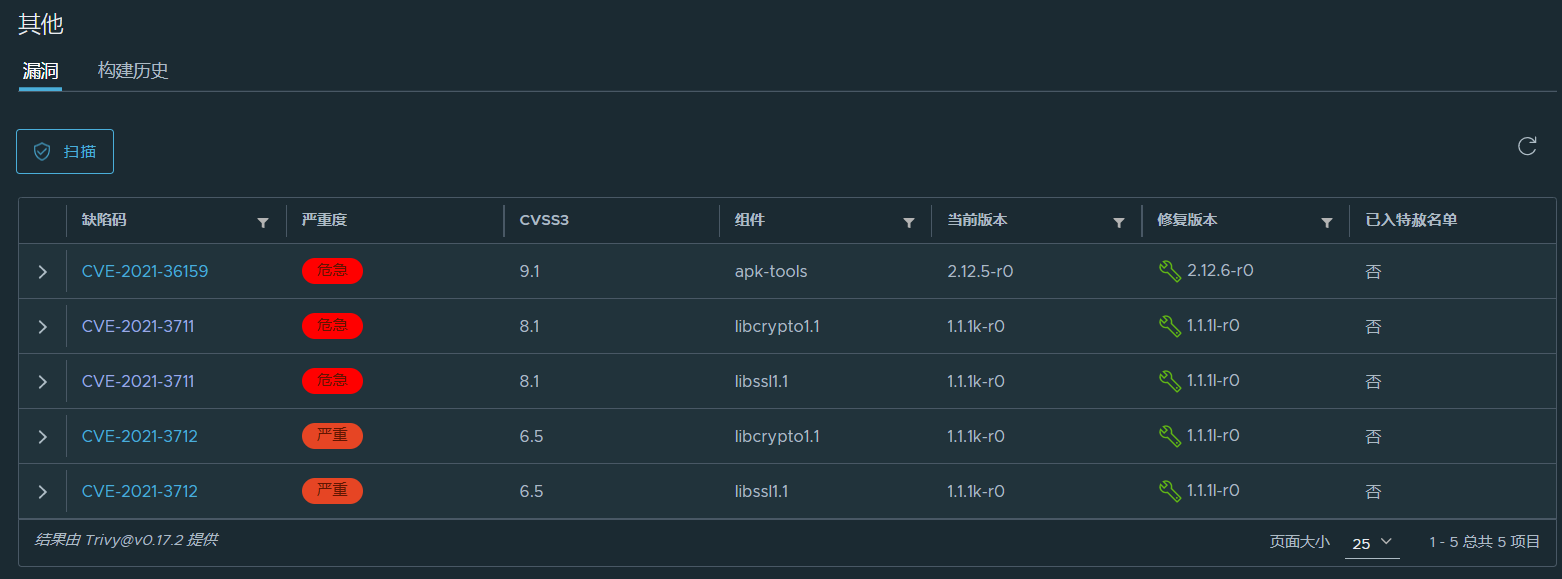
第三方仓库:harbor
https://goharbor.io/
项目地址
https://github.com/goharbor/harbor/releases
安装要求:
docker 17.06.0-ce+ and docker-compose 1.18.0+
安装手册
https://github.com/goharbor/harbor/tree/master/docs/1.10
Harbor的功能主要包括四大类:多用户的管控(基于角色访问控制和项目隔离)、镜像管理策略(存储配额、制品保留、漏洞扫描、来源签名、不可变制品、垃圾回收等)、安全与合规(身份认证、扫描和CVE例外规则等)和互操作性(Webhook、内容远程复制、可插拔扫描器、REST API、机器人账号等)
sudo ./install.sh --with-clair
docker tag nginx:latest 192.168.31.130/devops/nginx:v1
[root@docker-node1 harbor]# docker login 192.168.31.130
Username: liwm
Password:
WARNING! Your password will be stored unencrypted in /root/.docker/config.json.
Configure a credential helper to remove this warning. See
https://docs.docker.com/engine/reference/commandline/login/#credentials-store
Login Succeeded
[root@docker-node1 harbor]#
[root@docker-node1 harbor]# docker push 192.168.31.130/devops/nginx:v1
The push refers to repository [192.168.31.130/devops/nginx]
318be7aea8fc: Pushed
fe08d5d042ab: Pushed
f2cb0ecef392: Pushed
v1: digest: sha256:4a50ed86d8c86e35f530d4a168173677a192177eed14146fbb5728b1b3a2d4de size: 948
[root@docker-node1 harbor]# cat /etc/docker/daemon.json
{
"registry-mirrors": ["https://0bb06s1q.mirror.aliyuncs.com"],
"insecure-registries" : ["192.168.31.130"]
}
[root@docker-node1 harbor]#
dockers镜像导出和导入
导出:
[root@n9e ~]# docker image ls
REPOSITORY TAG IMAGE ID CREATED SIZE
docker.io/filebrowser/filebrowser latest 830d1363b1ef 4 days ago 33.4 MB
[root@n9e ~]# docker save -o /tmp/filebrowser.tar.gz docker.io/filebrowser/filebrowser:latest
[root@n9e ~]# ll /tmp/
total 32648
-rw------- 1 root root 33431040 Oct 26 09:18 filebrowser.tar.gz
drwx------ 2 root root 6 Oct 26 09:01 tmp.aV0PHawz9M
[root@n9e ~]#
导入:
docker load < filebrowser.tar.gz
[root@prod-smb-server01 tmp]# docker load < filebrowser.tar.gz
963d3c7196dd: Loading layer [==================================================>] 217.6kB/217.6kB
b62ffa58b9a4: Loading layer [==================================================>] 69.63kB/69.63kB
35f09ea19b05: Loading layer [==================================================>] 2.048kB/2.048kB
943906d44595: Loading layer [==================================================>] 33.12MB/33.12MB
Loaded image: filebrowser/filebrowser:latest
[root@prod-smb-server01 tmp]# docker image ls
REPOSITORY TAG IMAGE ID CREATED SIZE
filebrowser/filebrowser latest 830d1363b1ef 4 days ago 33.4MB
[root@prod-smb-server01 tmp]#
docker批量删除容器、镜像
1、删除所有容器
docker rm `docker ps -a -q`
2、删除所有镜像
docker rmi `docker images -q`
3、按条件删除镜像没有打标签
docker rmi `docker images -q | awk '/^<none>/ { print $3 }'`镜像名包含关键字
docker rmi --force `docker images | grep doss-api | awk '{print $3}'` //其中doss-api为关键字
Docker的镜像和容器可以有两种方式来导出
docker save #ID or #Name
docker export #ID or #Name
docker save和docker export的区别
对于Docker Save方法,会保存该镜像的所有历史记录
对于Docker Export 方法,不会保留历史记录,即没有commit历史
docker save保存的是镜像(image),docker export保存的是容器(container);
docker load用来载入镜像包,docker import用来载入容器包,但两者都会恢复为镜像;
docker load不能对载入的镜像重命名,而docker import可以为镜像指定新名称。
save命令
docker save [options] images [images...]
示例
docker save -o nginx.tar nginx:latest
或
docker save > nginx.tar nginx:latest
其中-o和>表示输出到文件,nginx.tar为目标文件,nginx:latest是源镜像名(name:tag)
load命令
docker load [options]
示例
docker load -i nginx.tar
或
docker load < nginx.tar
其中-i和<表示从文件输入。会成功导入镜像及相关元数据,包括tag信息
export命令
docker export [options] container
示例
docker export -o nginx-test.tar nginx-test
#导出为tar
docker export #ID or #Name > /home/export.tar
其中-o表示输出到文件,nginx-test.tar为目标文件,nginx-test是源容器名(name)
import命令
docker import [options] file|URL|- [REPOSITORY[:TAG]]
示例
docker import nginx-test.tar nginx:imp
或
cat nginx-test.tar | docker import - nginx:imp
查看镜像的Dockerfile文件