- 防火墙
- 点对点
- Recommended minimum configuration:
- Example rule allowing access from your local networks.
- Adapt to list your (internal) IP networks from where browsing
- should be allowed
- Recommended minimum Access Permission configuration:
- Deny requests to certain unsafe ports
- Deny CONNECT to other than secure SSL ports
- http_access deny CONNECT !SSL_ports
- Only allow cachemgr access from localhost
- We strongly recommend the following be uncommented to protect innocent
- web applications running on the proxy server who think the only
- one who can access services on “localhost” is a local user
- http_access deny to_localhost
- INSERT YOUR OWN RULE(S) HERE TO ALLOW ACCESS FROM YOUR CLIENTS
- Example rule allowing access from your local networks.
- Adapt localnet in the ACL section to list your (internal) IP networks
- from where browsing should be allowed
- And finally deny all other access to this proxy
- http_access deny all
- Squid normally listens to port 3128
- Uncomment and adjust the following to add a disk cache directory.
- cache_dir ufs /var/spool/squid 100 16 256
- Leave coredumps in the first cache dir
- Add any of your own refresh_pattern entries above these.
- 点对站
- 站对站
不知不觉中,疫情已经来到第三个年头,居家办公逐渐成为常态;但大多企业内部系统(如 OA、ERP、CRM)要么位于本地局域网,要么白名单访问;而现在的家庭宽带获取 IP 变动频繁甚至没有公网 IP,如何更稳定的保证外勤员工都能使用这些系统是重中之重。
防火墙
放行或者关闭防火墙
systemctl stop firewalldsystemctl disable firewalldsetenforce 0
点对点
一台固定公网 IP 的(VPS)服务器搭建相应的服务即可,客户端与服务器之间建立链路,客户端通过服务器网络访问企业内部 OA、ERP、CRM 等系统(添加服务器 IP 到白名单)
Dante
服务部署
http://www.inet.no/dante/download.html
yum install epel-releaserpm -ivh https://dl.fedoraproject.org/pub/epel/7Server/x86_64/Packages/e/epel-release-7-13.noarch.rpm
编译安装
yum -y install gcc openssl-devel pcre-devel zlib-devel libtool c++ pam-devel pamwget ftp://ftp.inet.no/pub/socks/dante-1.4.3.tar.gz && tar xvzf dante-1.4.3.tar.gz && cd dante-1.4.3./configure && make && make install
RPM 安装
rpm -ivh https://mirror.ghettoforge.org/distributions/gf/el/7/plus/x86_64/dante-1.4.1-176.9.x86_64.rpm # 安装 danterpm -ivh https://mirror.ghettoforge.org/distributions/gf/el/7/plus/x86_64/dante-server-1.4.1-176.9.x86_64.rpm # 安装 dante-server
服务配置
需要授权账号
useradd -s /sbin/nologin sockerpasswd sockermkdir /var/run/sockd
vim /etc/sockd.conf,详细说明见《官方文档》
#loggingerrorlog: /var/log/sockd-error.loglogoutput: /var/log/sockd.log#debug: 2#server address specificationinternal: eth0 port = 1080external: eth0#server identities (not needed on solaris)#user.privileged: rootuser.notprivileged: socker#user.libwrap: libwrap#reverse dns lookup#srchost: nodnsmismatch#authentication methodsclientmethod: nonesocksmethod: none#### SOCKS client access rules###rule processing stops at the first match, no match results in blocking#block access to socks server from 192.0.2.22 (exception for pass rule below)# client block {# #block connections from 192.0.2.22/32# from: 192.0.2.22/24 to: 0.0.0.0/0# log: error # connect disconnect# }#allow connections from local network (192.0.2.0/24)client pass {from: 192.0.2.0/24 to: 0.0.0.0/0log: error # connect disconnect}#### SOCKS command rules###rule processing stops at the first match, no match results in blocking#block communication with www.example.org# socks block {# from: 0.0.0.0/0 to: www.example.org# command: bind connect udpassociate# log: error # connect disconnect iooperation# }#generic pass statement - bind/outgoing trafficsocks pass {from: 0.0.0.0/0 to: 0.0.0.0/0command: bind connect udpassociatelog: error # connect disconnect iooperation}#block incoming connections/packets from ftp.example.org# socks block {# from: ftp.example.org to: 0.0.0.0/0# command: bindreply udpreply# log: error # connect disconnect iooperation# }#generic pass statement for incoming connections/packetssocks pass {from: 0.0.0.0/0 to: 0.0.0.0/0command: bindreply udpreplylog: error # connect disconnect iooperation}
使用/usr/local/sbin/sockd -f /etc/sockd.conf命令运行
系统服务
vim /usr/lib/systemd/system/sockd.service
[Unit]Description=scokdAfter=network.target remote-fs.target nss-lookup.target[Service]Type=forkingExecStart=/usr/local/sbin/sockd -f /etc/sockd.confExecReload=kill -HUP `cat /var/run/sockd.pid`ExecStop=kill -9 `cat /var/run/sockd.pid`[Install]WantedBy=multi-user.target
alert: run_request(): mother unexpectedly closed the IPC control channel: mother unexpectedly exited
服务日志
tail -f /var/log/sockd-error.log
Squid
- 传统代理:适用于 Internet,需在客户机指定代理服务器的地址和端口
- 透明代理:
- 反向代理:
服务部署
#安装yum install -y squid#设置开机启动systemctl enable squid#启动服务systemctl start squid
服务配置
vim /etc/squid/squid.conf修改服务配置,如 acl 规则、服务端口http_port等 ```bash #Recommended minimum configuration:
#
Example rule allowing access from your local networks.
Adapt to list your (internal) IP networks from where browsing
should be allowed
acl localnet src 10.0.0.0/8 # RFC1918 possible internal network acl localnet src 172.16.0.0/12 # RFC1918 possible internal network acl localnet src 192.168.0.0/16 # RFC1918 possible internal network acl localnet src fc00::/7 # RFC 4193 local private network range acl localnet src fe80::/10 # RFC 4291 link-local (directly plugged) machines
acl SSL_ports port 443 acl Safe_ports port 80 # http acl Safe_ports port 21 # ftp acl Safe_ports port 443 # https acl Safe_ports port 70 # gopher acl Safe_ports port 210 # wais acl Safe_ports port 1025-65535 # unregistered ports acl Safe_ports port 280 # http-mgmt acl Safe_ports port 488 # gss-http acl Safe_ports port 591 # filemaker acl Safe_ports port 777 # multiling http acl CONNECT method CONNECT
#
Recommended minimum Access Permission configuration:
#
Deny requests to certain unsafe ports
http_access deny !Safe_ports
Deny CONNECT to other than secure SSL ports
http_access deny CONNECT !SSL_ports
Only allow cachemgr access from localhost
http_access allow localhost manager http_access deny manager
We strongly recommend the following be uncommented to protect innocent
web applications running on the proxy server who think the only
one who can access services on “localhost” is a local user
http_access deny to_localhost
#
INSERT YOUR OWN RULE(S) HERE TO ALLOW ACCESS FROM YOUR CLIENTS
#
Example rule allowing access from your local networks.
Adapt localnet in the ACL section to list your (internal) IP networks
from where browsing should be allowed
http_access allow localnet http_access allow localhost
And finally deny all other access to this proxy
http_access deny all
http_access allow all
Squid normally listens to port 3128
http_port 10000
Uncomment and adjust the following to add a disk cache directory.
cache_dir ufs /var/spool/squid 100 16 256
Leave coredumps in the first cache dir
coredump_dir /var/spool/squid
#
Add any of your own refresh_pattern entries above these.
# refresh_pattern ^ftp: 1440 20% 10080 refresh_pattern ^gopher: 1440 0% 1440 refresh_pattern -i (/cgi-bin/|\?) 0 0% 0 refresh_pattern . 0 20% 4320
修改完配置需要`systemctl restart squid`重启服务,不想访问的时候关闭服务即可<a name="RTavN"></a>### 服务日志```bashtail -f /var/log/squid/access.log
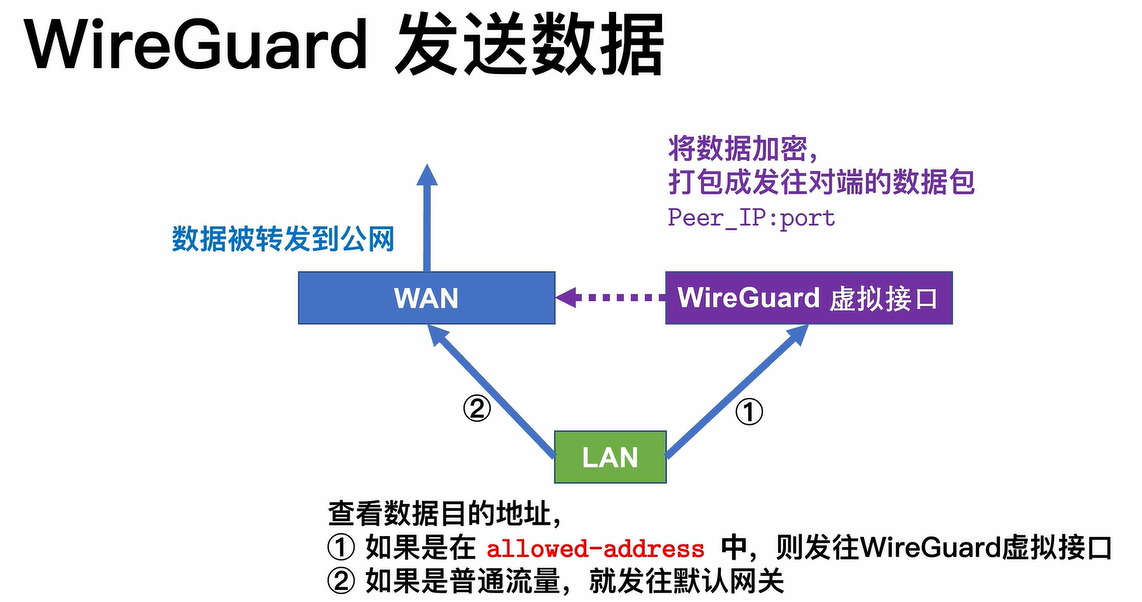
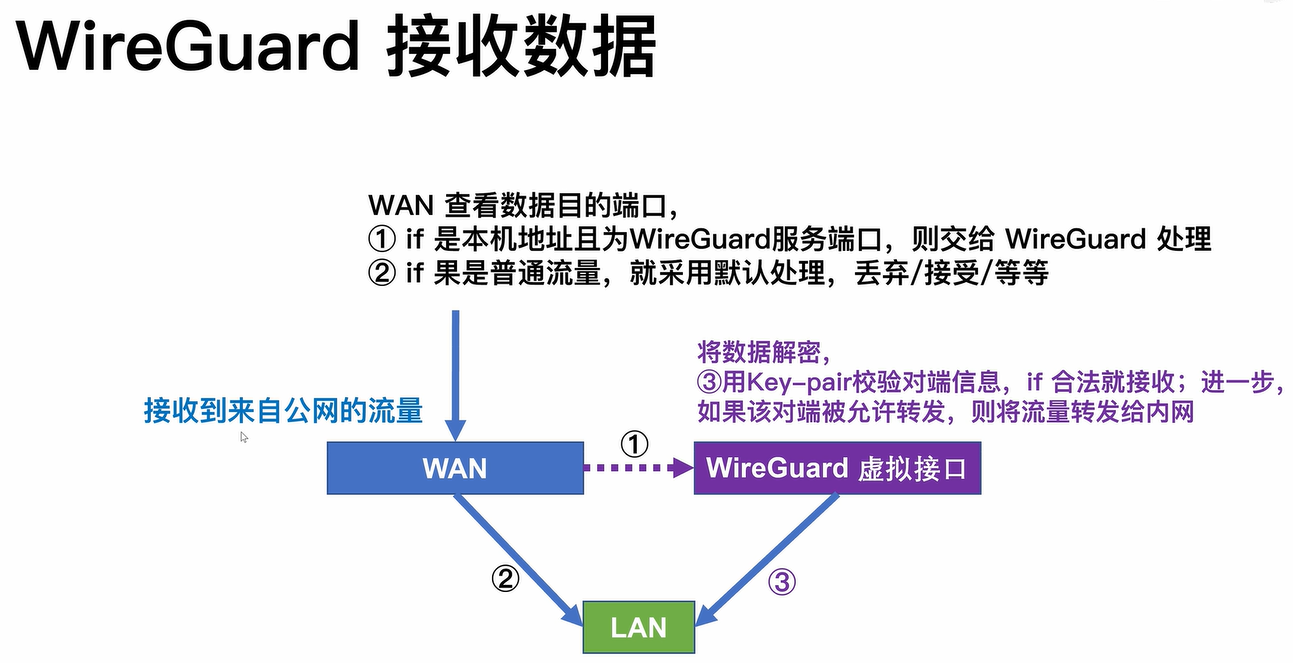
点对站
对于需要访问本地文件服务器、局域网其他资源的需求;点对站则是在点对点的基础上扩展而来,即服务需要部署在局域网内部服务器或者路由器网关上
IPsec
站对站
此类方案用于多地办公室组网、资源互通,从点对站升级而来;有钱的企业可以直接上BGP 组网,小公司性价比就不是很高了