这是一道经典而且简单的vm题目,没有什么太难的点,唯一比较坑的地方是,定义了很多的handler(其实也才几个),但是用到的很少。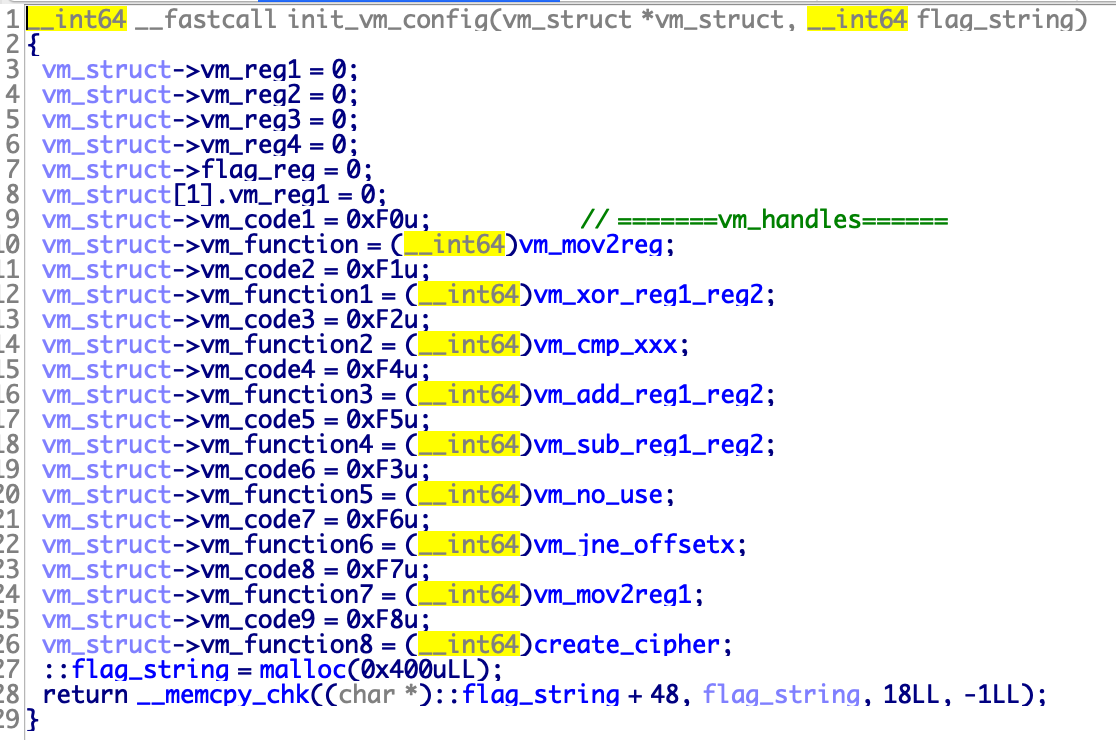

这样一看,解VM必备的参数就齐全了。就是简单运算加对比。
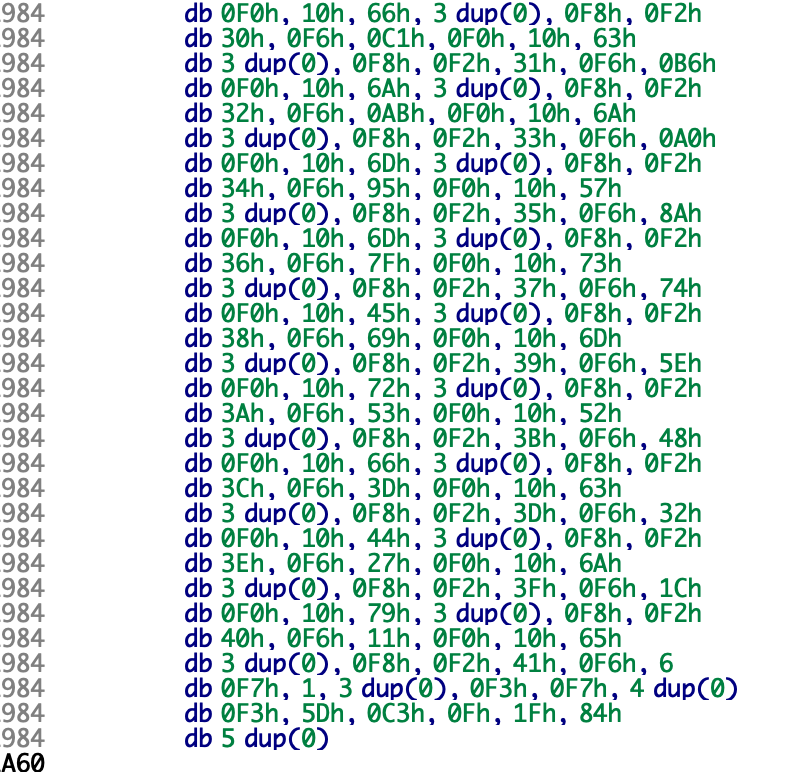
import reimport structvm_exec_code = [0xF0, 0x10, 0x66, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x30, 0xF6, 0xC1, 0xF0, 0x10, 0x63, 0x00, 0x00, 0x00,0xF8, 0xF2, 0x31, 0xF6, 0xB6, 0xF0, 0x10, 0x6A, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x32, 0xF6, 0xAB, 0xF0,0x10, 0x6A, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x33, 0xF6, 0xA0, 0xF0, 0x10, 0x6D, 0x00, 0x00, 0x00, 0xF8,0xF2, 0x34, 0xF6, 0x95, 0xF0, 0x10, 0x57, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x35, 0xF6, 0x8A, 0xF0, 0x10,0x6D, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x36, 0xF6, 0x7F, 0xF0, 0x10, 0x73, 0x00, 0x00, 0x00, 0xF8, 0xF2,0x37, 0xF6, 0x74, 0xF0, 0x10, 0x45, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x38, 0xF6, 0x69, 0xF0, 0x10, 0x6D,0x00, 0x00, 0x00, 0xF8, 0xF2, 0x39, 0xF6, 0x5E, 0xF0, 0x10, 0x72, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3A,0xF6, 0x53, 0xF0, 0x10, 0x52, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3B, 0xF6, 0x48, 0xF0, 0x10, 0x66, 0x00,0x00, 0x00, 0xF8, 0xF2, 0x3C, 0xF6, 0x3D, 0xF0, 0x10, 0x63, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3D, 0xF6,0x32, 0xF0, 0x10, 0x44, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3E, 0xF6, 0x27, 0xF0, 0x10, 0x6A, 0x00, 0x00,0x00, 0xF8, 0xF2, 0x3F, 0xF6, 0x1C, 0xF0, 0x10, 0x79, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x40, 0xF6, 0x11,0xF0, 0x10, 0x65, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x41, 0xF6, 0x06, 0xF7, 0x01, 0x00, 0x00, 0x00, 0xF3,0xF7, 0x00, 0x00, 0x00, 0x00, 0xF3]for i in range(len(vm_exec_code)):vm_exec_code[i] = chr(vm_exec_code[i])vm_exec_code = "".join(vm_exec_code)def vm_mov2reg(data):global vm_eipregx = ord(data[vm_eip + 1]) & 0xfprint "mov reg%d, 0x%x" % (regx + 1, struct.unpack("i", vm_exec_code[vm_eip + 2:vm_eip + 6])[0])vm_eip += 6def create_cipher(data):global vm_eipprint "call create_cipher then store reg1"vm_eip += 1def vm_cmp_xxx(data):global vm_eipprint "cmp reg1, flag_string%d" % (ord(data[vm_eip + 1]) - 0x30)vm_eip += 2def vm_jne_offsetx(data):global vm_eipprint "jne 0x%x" % ord(data[vm_eip + 1])vm_eip += 2def vm_mov2reg1(data):global vm_eiptmp_data = struct.unpack("i", vm_exec_code[vm_eip + 1:vm_eip + 5])[0]print "mov reg1, 0x%x" % tmp_datavm_eip += 5function_dic = {0xf0: vm_mov2reg,0xf8: create_cipher,0xf2: vm_cmp_xxx,0xf6: vm_jne_offsetx,0xf7: vm_mov2reg1}vm_eip = 0while True:vm_opcode = ord(vm_exec_code[vm_eip])if vm_opcode == 0xf3:print "END"breakfunction_dic[vm_opcode](vm_exec_code)
然后跑一下就出flag了。
import os
def create_cipher(input_char):
if 65 <= input_char <= 90:
return (input_char + 2 - 65) % 26 + 65
elif 97 <= input_char <= 122:
return (input_char + 2 - 97) % 26 + 97
else:
return input_char
all_indexs = []
all_code = [0xF0, 0x10, 0x66, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x30, 0xF6, 0xC1, 0xF0, 0x10, 0x63, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x31, 0xF6, 0xB6, 0xF0, 0x10, 0x6A, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x32, 0xF6, 0xAB, 0xF0, 0x10, 0x6A, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x33, 0xF6, 0xA0, 0xF0, 0x10, 0x6D, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x34, 0xF6, 0x95, 0xF0, 0x10, 0x57, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x35, 0xF6, 0x8A, 0xF0, 0x10, 0x6D, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x36, 0xF6, 0x7F, 0xF0, 0x10, 0x73, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x37, 0xF6, 0x74, 0xF0, 0x10, 0x45, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x38, 0xF6, 0x69, 0xF0, 0x10, 0x6D, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x39, 0xF6, 0x5E, 0xF0, 0x10, 0x72, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3A, 0xF6, 0x53, 0xF0, 0x10, 0x52, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3B, 0xF6, 0x48, 0xF0, 0x10, 0x66, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3C, 0xF6, 0x3D, 0xF0, 0x10, 0x63, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3D, 0xF6, 0x32, 0xF0, 0x10, 0x44, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3E, 0xF6, 0x27, 0xF0, 0x10, 0x6A, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x3F, 0xF6, 0x1C, 0xF0, 0x10, 0x79, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x40, 0xF6, 0x11, 0xF0, 0x10, 0x65, 0x00, 0x00, 0x00, 0xF8, 0xF2, 0x41, 0xF6, 0x06, 0xF7, 0x01, 0x00, 0x00, 0x00, 0xF3, 0xF7, 0x00, 0x00, 0x00, 0x00, 0xF3, 0x5D, 0xC3, 0x0F, 0x1F, 0x84, 0x00, 0x00, 0x00, 0x00, 0x00]
start_flag = 0
while 1:
try:
tmp_flag = all_code.index(0xF0, start_flag)
all_indexs.append(tmp_flag)
start_flag = tmp_flag + 1
except Exception as e:
break
flag = ""
for i in range(len(all_indexs)):
flag += chr(create_cipher(all_code[all_indexs[i] + 2]))
print "DDCTF{%s}" % flag

